A company’s product site recently had failed API calls, resulting in customers being unable to check out and purchase products. This type of failure could lead to the loss of customers and damage to the company’s reputation in the market.
Which of the following should the company implement to address the risk of system unavailability?
- A. User and entity behavior analytics
- B. Redundant reporting systems
- C. A self-healing system
- D. Application controls
Which of the following represents the MOST significant benefit of implementing a passwordless authentication solution?
- A. Biometric authenticators are immutable.
- B. The likelihood of account compromise is reduced.
- C. Zero trust is achieved.
- D. Privacy risks are minimized.
A review of the past year’s attack patterns shows that attackers stopped reconnaissance after finding a susceptible system to compromise. The company would like to find a way to use this information to protect the environment while still gaining valuable attack information.
Which of the following would be BEST for the company to implement?
- A. A WAF
- B. An IDS
- C. A SIEM
- D. A honeypot
A security architect is reviewing the following proposed corporate firewall architecture and configuration:
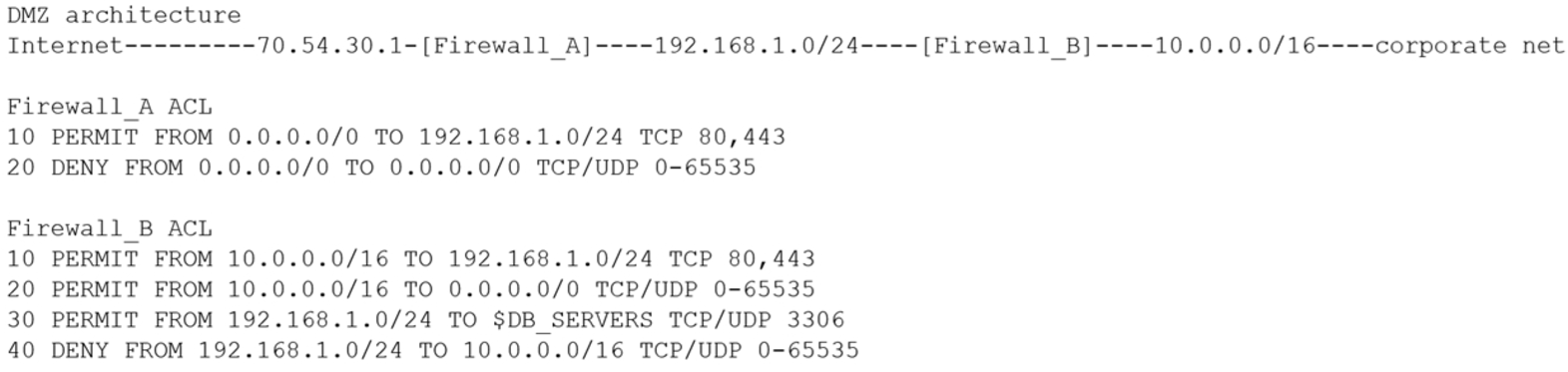
Both firewalls are stateful and provide Layer 7 filtering and routing. The company has the following requirements:
– Web servers must receive all updates via HTTP/S from the corporate network.
Web servers should not initiate communication with the Internet.

– Web servers should only connect to preapproved corporate database servers.
– Employees’ computing devices should only connect to web services over ports 80 and 443.
Which of the following should the architect recommend to ensure all requirements are met in the MOST secure manner? (Choose two.)
- A. Add the following to Firewall_A: 15 PERMIT FROM 10.0.0.0/16 TO 0.0.0.0/0 TCP 80,443
- B. Add the following to Firewall_A: 15 PERMIT FROM 192.168.1.0/24 TO 0.0.0.0 TCP 80,443
- C. Add the following to Firewall_A: 15 PERMIT FROM 10.0.0.0/16 TO 0.0.0.0/0 TCP/UDP 0-65535
- D. Add the following to Firewall_B: 15 PERMIT FROM 0.0.0.0/0 TO 10.0.0.0/16 TCP/UDP 0-65535
- E. Add the following to Firewall_B: 15 PERMIT FROM 10.0.0.0/16 TO 0.0.0.0 TCP/UDP 0-65535
- F. Add the following to Firewall_B: 15 PERMIT FROM 192.168.1.0/24 TO 10.0.2.10/32 TCP 80,443
As part of the customer registration process to access a new bank account, customers are required to upload a number of documents, including their passports and driver’s licenses. The process also requires customers to take a current photo of themselves to be compared against provided documentation.
Which of the following BEST describes this process?
- A. Deepfake
- B. Know your customer
- C. Identity proofing
- D. Passwordless
A user from the sales department opened a suspicious file attachment. The sales department then contacted the SOC to investigate a number of unresponsive systems, and the team successfully identified the file and the origin of the attack.
Which of the following is the NEXT step of the incident response plan?
- A. Remediation
- B. Containment
- C. Response
- D. Recovery
A recent data breach stemmed from unauthorized access to an employee’s company account with a cloud-based productivity suite. The attacker exploited excessive permissions granted to a third-party OAuth application to collect sensitive information.
Which of the following BEST mitigates inappropriate access and permissions issues?
- A. SIEM
- B. CASB
- C. WAF
- D. SOAR
A security engineer is hardening a company’s multihomed SFTP server. When scanning a public-facing network interface, the engineer finds the following ports are open:

– 25
– 110
– 137
– 138
– 139
– 445
Internal Windows clients are used to transferring files to the server to stage them for customer download as part of the company’s distribution process.
Which of the following would be the BEST solution to harden the system?
- A. Close ports 110, 138, and 139. Bind ports 22, 25, and 137 to only the internal interface.
- B. Close ports 25 and 110. Bind ports 137, 138, 139, and 445 to only the internal interface.
- C. Close ports 22 and 139. Bind ports 137, 138, and 445 to only the internal interface.
- D. Close ports 22, 137, and 138. Bind ports 110 and 445 to only the internal interface.
A recent data breach revealed that a company has a number of files containing customer data across its storage environment. These files are individualized for each employee and are used in tracking various customer orders, inquiries, and issues. The files are not encrypted and can be accessed by anyone. The senior management team would like to address these issues without interrupting existing processes.
Which of the following should a security architect recommend?
- A. A DLP program to identify which files have customer data and delete them
- B. An ERP program to identify which processes need to be tracked
- C. A CMDB to report on systems that are not configured to security baselines
- D. A CRM application to consolidate the data and provision access based on the process and need
A security analyst observes the following while looking through network traffic in a company’s cloud log:
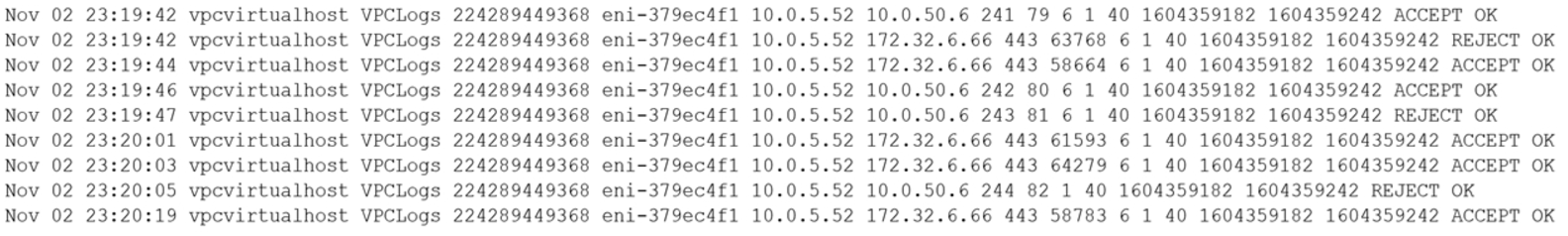
Which of the following steps should the security analyst take FIRST?
- A. Quarantine 10.0.5.52 and run a malware scan against the host.
- B. Access 10.0.5.52 via EDR and identify processes that have network connections.
- C. Isolate 10.0.50.6 via security groups.
- D. Investigate web logs on 10.0.50.6 to determine if this is normal traffic.
