Pass CompTIA CySA+ CS0-003 in Just 3 Days – Stress-Free, No Study Needed!
Have questions? Contact us directly on WhatsApp for quick support!
Free CompTIA CySA+ CS0-003 Dumps & Practice Questions
Prepare for the CompTIA Cybersecurity Analyst CySA+ CS0-003 exam with our completely free dumps and sample questions. No cost, no registration required.
Why Our CySA+ Free Dumps Are Perfect
First, you get access to the most recent CompTIA CySA+ CS0-003 questions for free. Next, our content is verified by cybersecurity professionals. Finally, there are no hidden fees or trial subscriptions.
Moreover, practicing with real questions helps you understand the exam format and reduces test anxiety. As a result, you can focus on passing the CySA+ certification efficiently.
How to Use Our Free CySA+ Dumps
- Step 1: Browse our free question sets.
- Step 2: Review and practice regularly.
- Step 3: Track your progress and improve weak areas.
Note: Using these dumps as a guide helps you focus your preparation and boost confidence before taking the official CS0-003 exam.
Sample CySA+ CS0-003 Questions – Free Access
- Question 1: How do you detect and respond to cybersecurity threats in a network?
- Question 2: What are the steps to configure SIEM solutions for monitoring security events?
- Question 3: How do you perform vulnerability assessments and prioritize remediation?
- Question 4: Which tools are used to analyze threat intelligence effectively?
- Question 5: How do you create incident response procedures for detected breaches?
All questions are 100% free and designed to help you practice for the real CySA+ exam.
Who Should Use These Free Dumps?
This resource is ideal for cybersecurity professionals, analysts, and IT security specialists preparing for CompTIA CySA+ CS0-003. If you want to study efficiently without spending money, these free dumps are perfect. Even if you are retaking the exam, practicing with real questions helps you succeed.
Start Practicing CySA+ Free Today
Access all our free dumps and sample questions now. Improve your knowledge, practice with real scenarios, and prepare confidently for the CompTIA CySA+ CS0-003 exam.
A recent zero-day vulnerability is being actively exploited, requires no user interaction or privilege escalation, and has a significant impact to confidentiality and integrity but not to availability. Which of the following CVE metrics would be most accurate for this zero-day threat?
- A. CVSS:31/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:K/A:L
- B. CVSS:31/AV:K/AC:L/PR:H/UI:R/S:C/C:H/I:H/A:L
- C. CVSS:31/AV:N/AC:L/PR:N/UI:H/S:U/C:L/I:N/A:H
- D. CVSS:31/AV:L/AC:L/PR:R/UI:R/S:U/C:H/I:L/A:H
Which of the following tools would work best to prevent the exposure of PII outside of an organization?
- A. PAM
- B. IDS
- C. PKI
- D. DLP
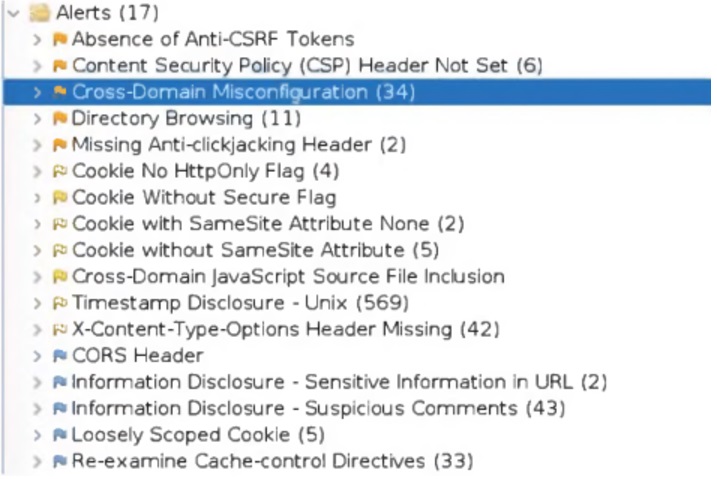
An organization conducted a web application vulnerability assessment against the corporate website, and the following output was observed:
Which of the following tuning recommendations should the security analyst share?
- A. Set an HttpOnly flag to force communication by HTTPS
- B. Block requests without an X-Frame-Options header
- C. Configure an Access-Control-Allow-Origin header to authorized domains
- D. Disable the cross-origin resource sharing header
Which of the following items should be included in a vulnerability scan report? (Choose two.)
- A. Lessons learned
- B. Service-level agreement
- C. Playbook
- D. Affected hosts
- E. Risk score
- F. Education plan
The Chief Executive Officer of an organization recently heard that exploitation of new attacks in the industry was happening approximately 45 days after a patch was released. Which of the following would best protect this organization?
- A. A mean time to remediate of 30 days
- B. A mean time to detect of 45 days
- C. A mean time to respond of 15 days
- D. Third-party application testing
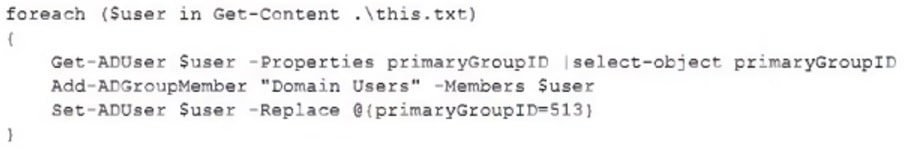
A security analyst recently joined the team and is trying to determine which scripting language is being used in a production script to determine if it is malicious. Given the following script:
Which of the following scripting languages was used in the script?
- A. PowerShell
- B. Ruby
- C. Python
- D. Shell script
A company’s user accounts have been compromised. Users are also reporting that the company’s internal portal is sometimes only accessible through HTTP, other times; it is accessible through HTTPS. Which of the following most likely describes the observed activity?
- A. There is an issue with the SSL certificate causing port 443 to become unavailable for HTTPS access
- B. An on-path attack is being performed by someone with internal access that forces users into port 80
- C. The web server cannot handle an increasing amount of HTTPS requests so it forwards users to port 80
- D. An error was caused by BGP due to new rules applied over the company’s internal routers
A security analyst is tasked with prioritizing vulnerabilities for remediation. The relevant company security policies are shown below:
Security Policy 1006: Vulnerability Management
1. The Company shall use the CVSSv3.1 Base Score Metrics (Exploitability and Impact) to prioritize the remediation of security vulnerabilities.
2. In situations where a choice must be made between confidentiality and availability, the Company shall prioritize confidentiality of data over availability of systems and data.
3. The Company shall prioritize patching of publicly available systems and services over patching of internally available system.
According to the security policy, which of the following vulnerabilities should be the highest priority to patch?
- A. Name: THOR.HAMMER –
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H
Internal System - B. Name: CAP.SHIELD –
CVSS 3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
External System - C. Name: LOKI.DAGGER –
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H
External System - D. Name: THANOS.GAUNTLET –
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
Internal System
Which of the following will most likely ensure that mission-critical services are available in the event of an incident?
- A. Business continuity plan
- B. Vulnerability management plan
- C. Disaster recovery plan
- D. Asset management plan
The Chief Information Security Officer wants to eliminate and reduce shadow IT in the enterprise. Several high-risk cloud applications are used that increase the risk to the organization. Which of the following solutions will assist in reducing the risk?
- A. Deploy a CASB and enable policy enforcement
- B. Configure MFA with strict access
- C. Deploy an API gateway
- D. Enable SSO to the cloud applications