Pass CompTIA CySA+ CS0-003 in Just 3 Days – Stress-Free, No Study Needed!
Have questions? Contact us directly on WhatsApp for quick support!
An incident response team receives an alert to start an investigation of an internet outage. The outage is preventing all users in multiple locations from accessing external SaaS resources. The team determines the organization was impacted by a DDoS attack. Which of the following logs should the team review first?
- A. CDN
- B. Vulnerability scanner
- C. DNS
- D. Web server
A malicious actor has gained access to an internal network by means of social engineering. The actor does not want to lose access in order to continue the attack. Which of the following best describes the current stage of the Cyber Kill Chain that the threat actor is currently operating in?
- A. Weaponization
- B. Reconnaissance
- C. Delivery
- D. Exploitation
An analyst finds that an IP address outside of the company network that is being used to run network and vulnerability scans across external-facing assets. Which of the following steps of an attack framework is the analyst witnessing?
- A. Exploitation
- B. Reconnaissance
- C. Command and control
- D. Actions on objectives
An incident response analyst notices multiple emails traversing the network that target only the administrators of the company. The email contains a concealed URL that leads to an unknown website in another country. Which of the following best describes what is happening? (Choose two.)
- A. Beaconing
- B. Domain Name System hijacking
- C. Social engineering attack
- D. On-path attack
- E. Obfuscated links
- F. Address Resolution Protocol poisoning
During security scanning, a security analyst regularly finds the same vulnerabilities in a critical application. Which of the following recommendations would best mitigate this problem if applied along the SDLC phase?
- A. Conduct regular red team exercises over the application in production
- B. Ensure that all implemented coding libraries are regularly checked
- C. Use application security scanning as part of the pipeline for the CI/CD flow
- D. Implement proper input validation for any data entry form
An analyst is reviewing a vulnerability report and must make recommendations to the executive team. The analyst finds that most systems can be upgraded with a reboot resulting in a single downtime window. However, two of the critical systems cannot be upgraded due to a vendor appliance that the company does not have access to. Which of the following inhibitors to remediation do these systems and associated vulnerabilities best represent?
- A. Proprietary systems
- B. Legacy systems
- C. Unsupported operating systems
- D. Lack of maintenance windows
The security team reviews a web server for XSS and runs the following Nmap scan: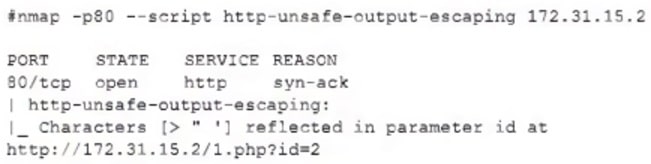
Which of the following most accurately describes the result of the scan?
- A. An output of characters > and ” as the parameters used m the attempt
- B. The vulnerable parameter ID http://172.31.15.2/1.php?id-2 and unfiltered characters returned
- C. The vulnerable parameter and unfiltered or encoded characters passed > and ” as unsafe
- D. The vulnerable parameter and characters > and ” with a reflected XSS attempt
Which of the following is the best action to take after the conclusion of a security incident to improve incident response in the future?
- A. Develop a call tree to inform impacted users
- B. Schedule a review with all teams to discuss what occurred
- C. Create an executive summary to update company leadership
- D. Review regulatory compliance with public relations for official notification
A security analyst received a malicious binary file to analyze. Which of the following is the best technique to perform the analysis?
- A. Code analysis
- B. Static analysis
- C. Reverse engineering
- D. Fuzzing
An incident response team found IoCs in a critical server. The team needs to isolate and collect technical evidence for further investigation. Which of the following pieces of data should be collected first in order to preserve sensitive information before isolating the server?
- A. Hard disk
- B. Primary boot partition
- C. Malicious files
- D. Routing table
- E. Static IP address
