Pass CompTIA CySA+ CS0-003 in Just 3 Days – Stress-Free, No Study Needed!
Have questions? Contact us directly on WhatsApp for quick support!
An analyst is reviewing a vulnerability report for a server environment with the following entries:
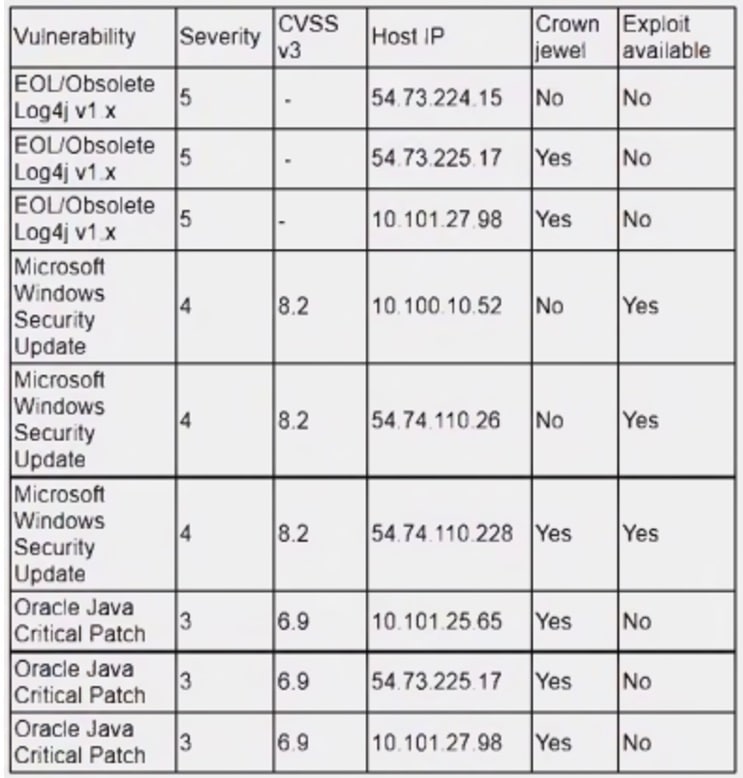
Which of the following systems should be prioritized for patching first?
- A. 10.101.27.98
- B. 54.73.225.17
- C. 54.74.110.26
- D. 54.74.110.228
A company is in the process of implementing a vulnerability management program, and there are concerns about granting the security team access to sensitive data. Which of the following scanning methods can be implemented to reduce the access to systems while providing the most accurate vulnerability scan results?
- A. Credentialed network scanning
- B. Passive scanning
- C. Agent-based scanning
- D. Dynamic scanning
A security analyst is trying to identify anomalies on the network routing. Which of the following functions can the analyst use on a shell script to achieve the objective most accurately?
- A. function x() { info=$(geoiplookup $1) && echo “$1 | $info” }
- B. function x() { info=$(ping -c 1 $1 | awk -F “/” ’END{print $5}’) && echo “$1 | $info” }
- C. function x() { info=$(dig $(dig -x $1 | grep PTR | tail -n 1 | awk -F “.in-addr” ’{print $1} ‘).origin.asn.cymru.com TXT +short) && echo “$1 | $info” }
- D. function x() { info=$(traceroute -m 40 $1 | awk ‘END{print $1}’) && echo “$1 | $info” }
There are several reports of sensitive information being disclosed via file sharing services. The company would like to improve its security posture against this threat. Which of the following security controls would best support the company in this scenario?
- A. Implement step-up authentication for administrators
- B. Improve employee training and awareness
- C. Increase password complexity standards
- D. Deploy mobile device management
Which of the following is the best way to begin preparation for a report titled “What We Learned” regarding a recent incident involving a cybersecurity breach?
- A. Determine the sophistication of the audience that the report is meant for
- B. Include references and sources of information on the first page
- C. Include a table of contents outlining the entire report
- D. Decide on the color scheme that will effectively communicate the metrics
A security analyst is performing an investigation involving multiple targeted Windows malware binaries. The analyst wants to gather intelligence without disclosing information to the attackers. Which of the following actions would allow the analyst to achieve the objective?
- A. Upload the binary to an air gapped sandbox for analysis
- B. Send the binaries to the antivirus vendor
- C. Execute the binaries on an environment with internet connectivity
- D. Query the file hashes using VirusTotal
Which of the following would help to minimize human engagement and aid in process improvement in security operations?
- A. OSSTMM
- B. SIEM
- C. SOAR
- D. OWASP
After conducting a cybersecurity risk assessment for a new software request, a Chief Information Security Officer (CISO) decided the risk score would be too high. The CISO refused the software request. Which of the following risk management principles did the CISO select?
- A. Avoid
- B. Transfer
- C. Accept
- D. Mitigate
Which of the following is an important aspect that should be included in the lessons-learned step after an incident?
- A. Identify any improvements or changes in the incident response plan or procedures
- B. Determine if an internal mistake was made and who did it so they do not repeat the error
- C. Present all legal evidence collected and turn it over to iaw enforcement
- D. Discuss the financial impact of the incident to determine if security controls are well spent
The security operations team is required to consolidate several threat intelligence feeds due to redundant tools and portals. Which of the following will best achieve the goal and maximize results?
- A. Single pane of glass
- B. Single sign-on
- C. Data enrichment
- D. Deduplication
