We HELP you PASS (CCNP 350-401) Implementing Cisco Enterprise Network Core Technologies (ENCOR) certification, without exam and training!
***Pay after you Pass***
Why is an AP joining a different WLC than the one specified through option 43?
- A. The AP is joining a primed WLC
- B. The APs broadcast traffic is unable to reach the WLC through Layer 2
- C. The AP multicast traffic is unable to reach the WLC through Layer 3
- D. The WLC is running a different software version
What is the difference between a RIB and a FIB?
• A. The FIB is populated based on RIB content.
• B. The RIB maintains a mirror image of the FIB.
• C. The RIB is used to make IP source prefix-based switching decisions.
• D. The FIB is where all IP routing information is stored.
Which QoS component alters a packet to change the way that traffic is treated in the network?
• A. policing
• B. classification
• C. marking
• D. shaping
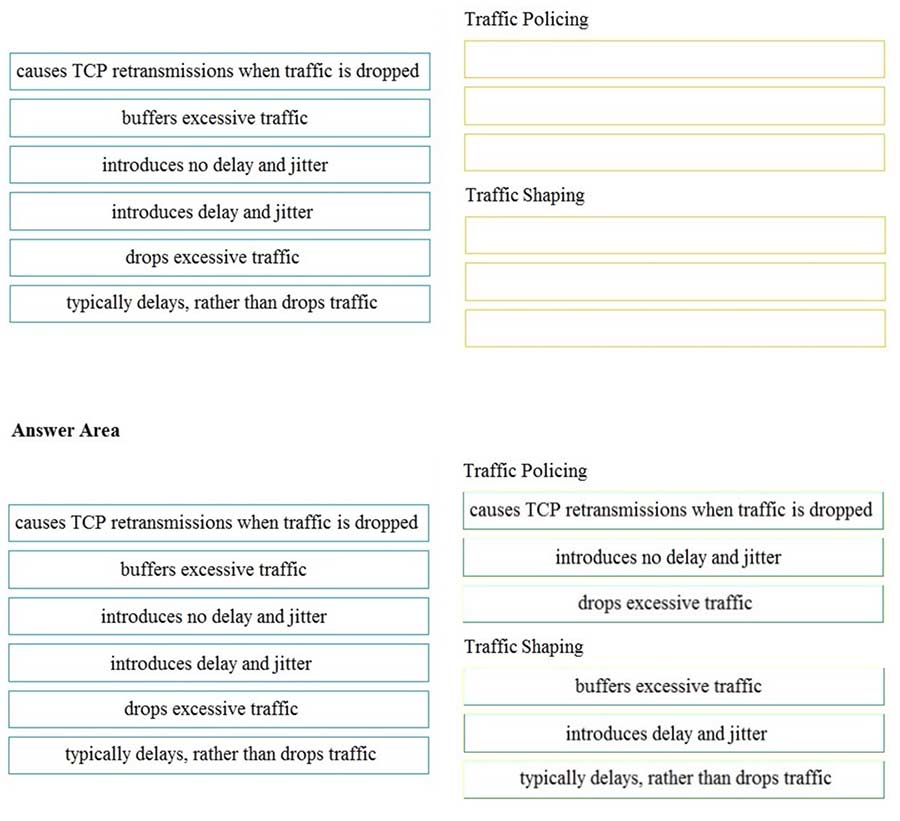
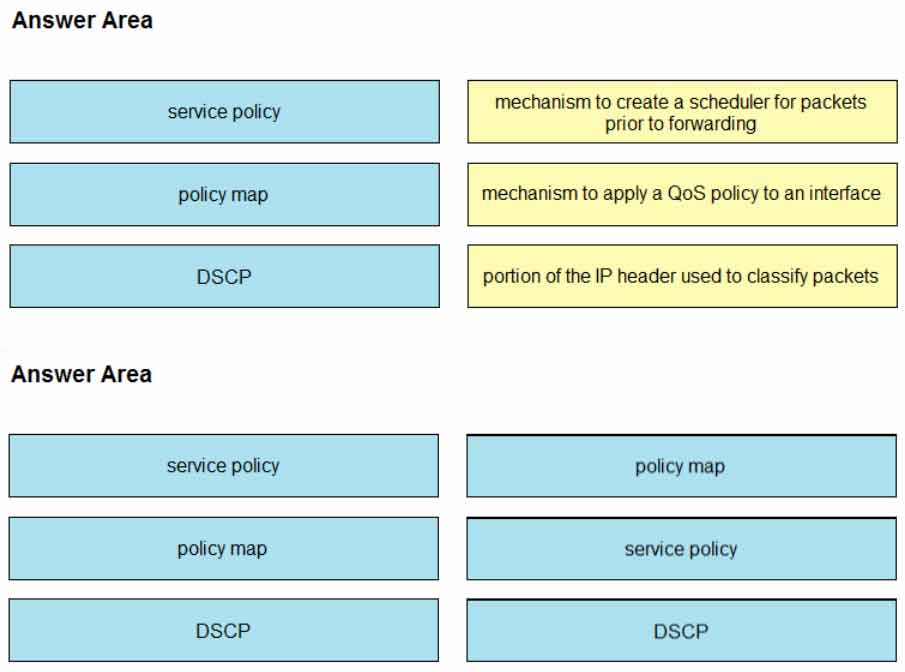
DRAG DROP –
Drag and drop the descriptions from the left onto the correct QoS components on the right.
Which statement about Cisco Express Forwarding is true?
• A. The CPU of a router becomes directly involved with packet-switching decisions.
• B. It uses a fast cache that is maintained in a router data plane.
• C. It maintains two tables in the data plane: the FIB and adjacency table.
• D. It makes forwarding decisions by a process that is scheduled through the IOS scheduler.
What is a benefit of deploying an on-premises infrastructure versus a cloud infrastructure
deployment?
• A. ability to quickly increase compute power without the need to install additional hardware
• B. less power and cooling resources needed to run infrastructure on-premises
• C. faster deployment times because additional infrastructure does not need to be purchased
• D. lower latency between systems that are physically located near each other
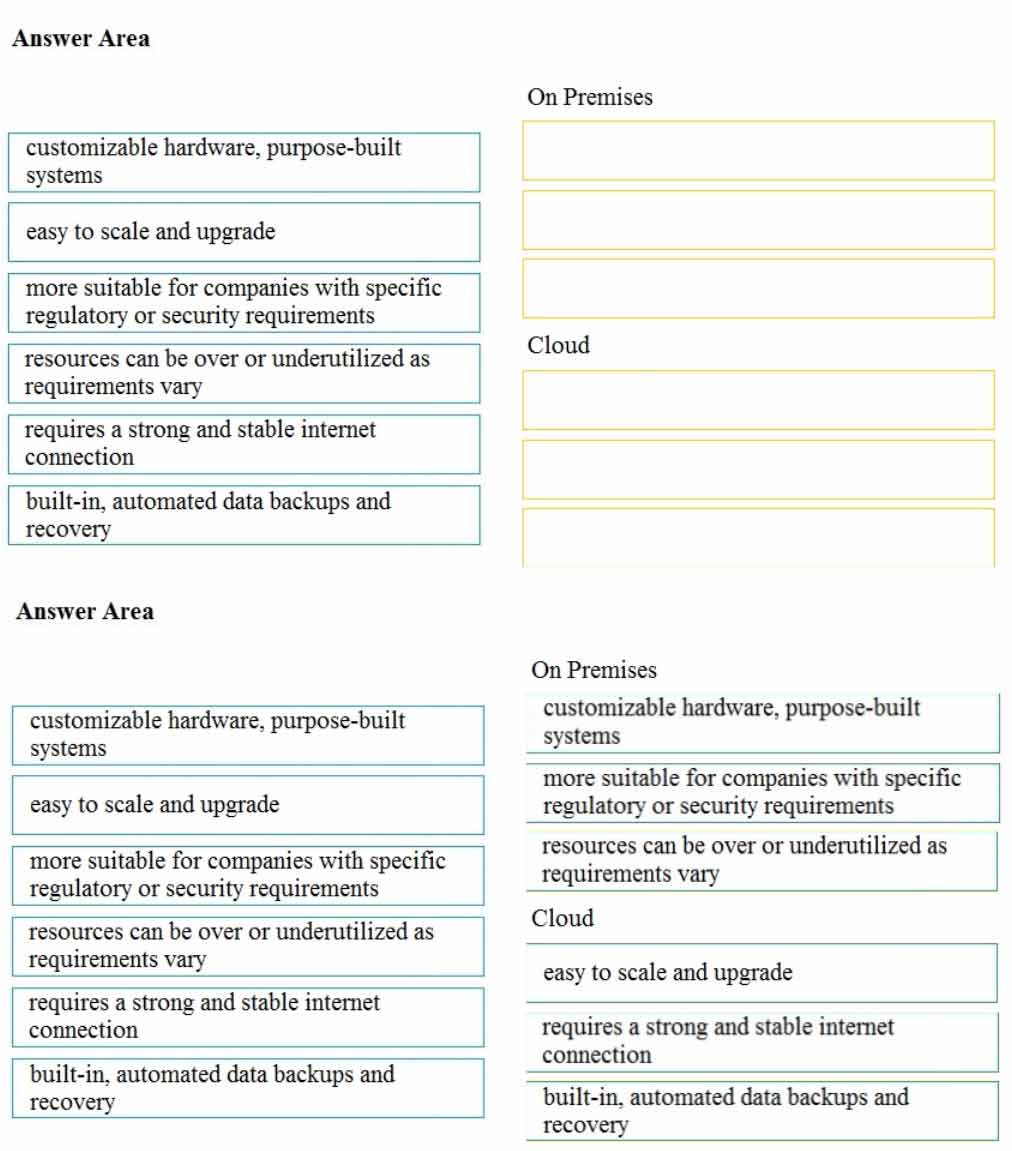
DRAG DROP –
Drag and drop the characteristics from the left onto the appropriate infrastructure deployment types
on the right.
Select and Place:
How does QoS traffic shaping alleviate network congestion?
• A. It drops packets when traffic exceeds a certain bitrate.
• B. It buffers and queues packets above the committed rate.
• C. It fragments large packets and queues them for delivery.
• D. It drops packets randomly from lower priority queues.
An engineer is describing QoS to a client.
Which two facts apply to traffic policing? (Choose two.)
• A. Policing should be performed as close to the source as possible.
• B. Policing adapts to network congestion by queuing excess traffic.
• C. Policing should be performed as close to the destination as possible.
• D. Policing drops traffic that exceeds the defined rate.
• E. Policing typically delays the traffic, rather than drops it.
Which component handles the orchestration plane of the Cisco SD-WAN?
• A. vBond
• B. vSmart
• C. vManage
• D. WAN Edge
What are two device roles in Cisco SD-Access fabric? (Choose two.)
• A. edge node
• B. vBond controller
• C. access switch
• D. core switch
• E. border node
What is the role of the vSmart controller in a Cisco SD-WAN environment?
• A. It performs authentication and authorization.
• B. It manages the control plane.
• C. It is the centralized network management system.
• D. It manages the data plane.
When a wired client connects to an edge switch in a Cisco SD-Access fabric, which component
decides whether the client has access to the network?
• A. edge node
• B. Identity Services Engine
• C. RADIUS server
• D. control-plane node
Which benefit is offered by a cloud infrastructure deployment but is lacking in an on-premises
deployment?
• A. virtualization
• B. supported systems
• C. storage capacity
• D. efficient scalability
Which action is the vSmart controller responsible for in a Cisco SD-WAN deployment?
• A. onboard WAN Edge nodes into the Cisco SD-WAN fabric
• B. gather telemetry data from WAN Edge routers
• C. distribute policies that govern data forwarding performed within the Cisco SD-WAN fabric
• D. handle, maintain, and gather configuration and status for nodes within the Cisco SD-WAN
fabric
Where is radio resource management performed in a Cisco SD-Access wireless solution?
• A. DNA Center
• B. control plane node
• C. wireless controller
• D. Cisco CMX
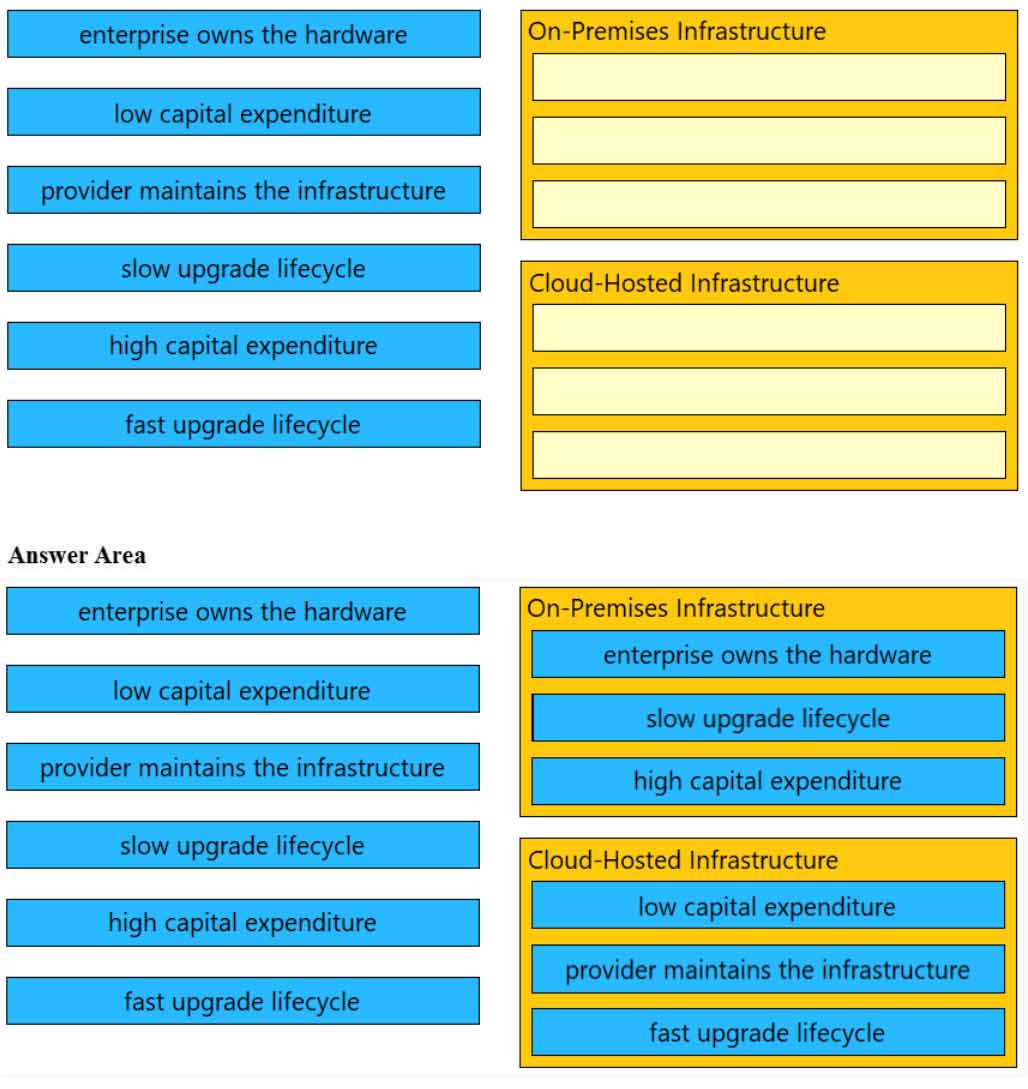
DRAG DROP –
Drag and drop the characteristics from the left onto the infrastructure types on the right.
How does the RIB differ from the FIB?
• A. The FIB maintains network topologies and routing tables. The RIB is a list of routes to particular network destinations.
• B. The FIB includes many routes to a single destination. The RIB is the best route to a single destination.
• C. The RIB is used to create network topologies and routing tables. The FIB is a list of routes to particular network destinations.
• D. The RIB includes many routes to the same destination prefix. The FIB contains only the best route.
Which technology is used to provide Layer 2 and Layer 3 logical networks in the Cisco SD-Access architecture?
• A. underlay network
• B. VPN routing/forwarding
• C. easy virtual network
• D. overlay network
What is the difference between CEF and process switching?
• A. CEF processes packets that are too complex for process switching to manage.
• B. Process switching is faster than CEF.
• C. CEF uses the FIB and the adjacency table to make forwarding decisions, whereas process switching punts each packet.
• D. CEF is more CPU-intensive than process switching.
What are two considerations when using SSO as a network redundancy feature? (Choose two.)
• A. requires synchronization between supervisors in order to guarantee continuous connectivity
• B. the multicast state is preserved during switchover
• C. must be combined with NSF to support uninterrupted Layer 3 operations
• D. both supervisors must be configured separately
• E. must be combined with NSF to support uninterrupted Layer 2 operations
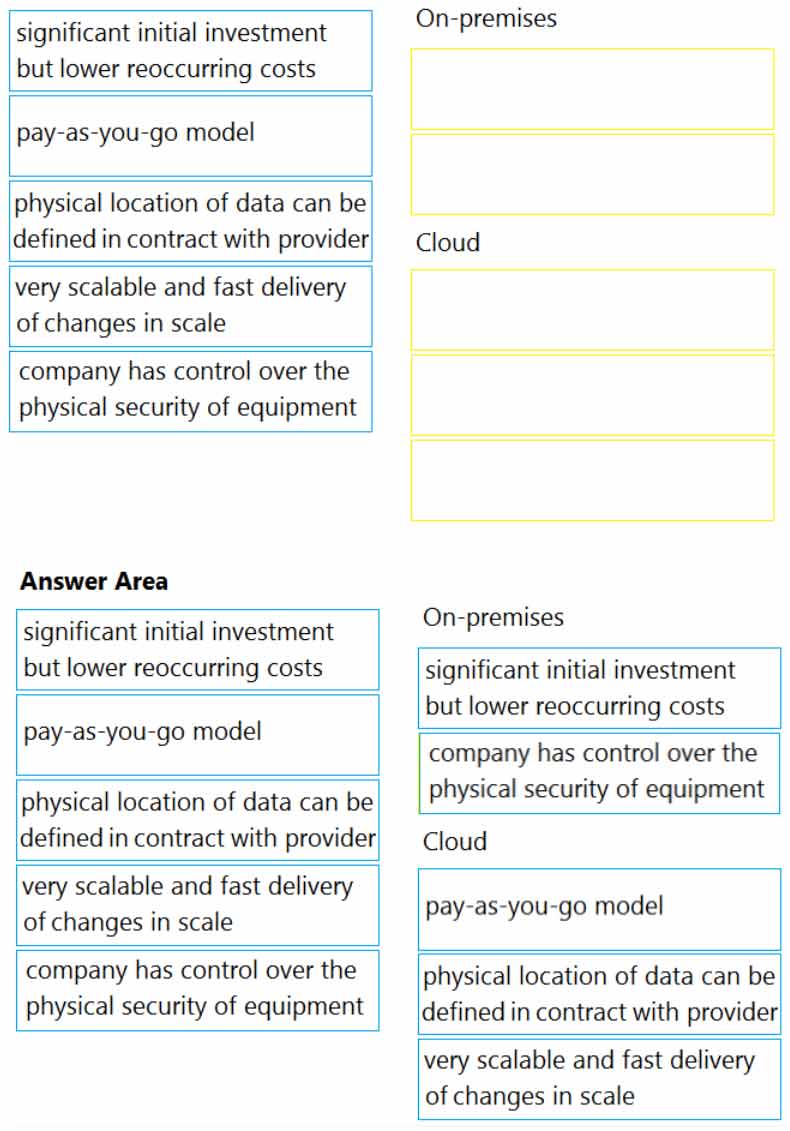
DRAG DROP –
Drag and drop the characteristics from the left onto the correct infrastructure deployment type on the right.
Select and Place:
In a Cisco SD-Access fabric, which control plane protocol is used for mapping and resolving endpoints?
• A. DHCP
• B. VXLAN
• C. SXP
• D. LISP
What are two differences between the RIB and the FIB? (Choose two.)
A. FIB is a database of routing prefixes, and the RIB is the information used to choose the egress interface for each packet.
• B. The FIB is derived from the data plane, and the RIB is derived from the FIB.
• C. The RIB is a database of routing prefixes, and the FIB is the information used to choose the egress interface for each packet.
• D. The RIB is derived from the control plane, and the FIB is derived from the RIB.
• E. The FIB is derived from the control plane, and the RIB is derived from the FIB.
Which two network problems indicate a need to implement QoS in a campus network? (Choose two.)
• A. port flapping
• B. excess jitter
• C. misrouted network packets
• D. duplicate IP addresses
• E. bandwidth-related packet loss
In a Cisco SD-Access wireless architecture, which device manages endpoint ID to edge node bindings?
• A. fabric control plane node
• B. fabric wireless controller
• C. fabric border node
• D. fabric edge node
DRAG DROP –
Drag and drop the QoS mechanisms from the left onto their descriptions on the right.
Select and Place:
Which control plane protocol is used between Cisco SD-WAN routers and vSmart controllers?
• A. TCP
• B. OMP
• C. UDP
• D. BGP
In a three-tier hierarchical campus network design, which action is a design best-practice for the core layer?
• A. provide QoS prioritization services such as marking, queueing, and classification for critical network traffic
• B. provide redundant Layer 3 point-to-point links between the core devices for more predictable and faster convergence
• C. provide advanced network security features such as 802.1X, DHCP snooping, VACLs, and port security
• D. provide redundant aggregation for access layer devices and first-hop redundancy protocols such as VRRP
What is a VPN in a Cisco SD-WAN deployment?
• A. common exchange point between two different services
• B. attribute to identify a set of services offered in specific places in the SD-WAN fabric
• C. virtualized environment that provides traffic isolation and segmentation in the SD-WAN fabric
• D. virtual channel used to carry control plane information
Which function does a fabric edge node perform in an SD-Access deployment?
• A. Connects endpoints to the fabric and forwards their traffic.
• B. Encapsulates end-user data traffic into LISP.
• C. Connects the SD-Access fabric to another fabric or external Layer 3 networks.
• D. Provides reachability between border nodes in the fabric underlay.
What is the role of a fusion router in an SD-Access solution?
• A. acts as a DNS server
• B. provides additional forwarding capacity to the fabric
• C. performs route leaking between user-defined virtual networks and shared services
• D. provides connectivity to external networks
Which action is the vSmart controller responsible for in an SD-WAN deployment?
• A. onboard vEdge nodes into the SD-WAN fabric
• B. gather telemetry data from vEdge routers
• C. distribute security information for tunnel establishment between vEdge routers
• D. manage, maintain, and gather configuration and status for nodes within the SD-WAN fabric
What is one fact about Cisco SD-Access wireless network deployments?
• A. The access point is part of the fabric overlay.
• B. The wireless client is part of the fabric overlay.
• C. The access point is part of the fabric underlay.
• D. The WLC is part of the fabric underlay.
In a Cisco SD-Access solution, what is the role of a fabric edge node?
• A. to connect external Layer 3 networks to the SD-Access fabric
• B. to connect wired endpoints to the SD-Access fabric
• C. to advertise fabric IP address space to external networks
• D. to connect the fusion router to the SD-Access fabric
What are two reasons a company would choose a cloud deployment over an on-prem deployment? (Choose two.)
• A. Cloud costs adjust up or down depending on the amount of resources consumed. On prem costs for hardware, power, and space are on-going regardless of usage.
• B. Cloud resources scale automatically to an increase in demand. On-prem requires additional capital expenditure.
• C. In a cloud environment, the company is in full control of access to their data. On-prem risks access to data due to service provider outages.
• D. In a cloud environment, the company controls technical issues. On-prem environments rely on the service provider to resolve technical issues.
• E. Cloud deployments require long implementation times due to capital expenditure processes. On-prem deployments can be accomplished quickly using operational expenditure processes.
What is the difference between the MAC address table and TCAM?
• A. TCAM is used to make L2 forwarding decisions. CAM is used to build routing tables.
• B. Router prefix lookups happen in CAM. MAC address table lookups happen in TCAM.
• C. The MAC address table supports partial matches. TCAM requires an exact match.
• D. The MAC address table is contained in CAM. ACL and QoS information is stored in TCAM.
Which controller is the single plane of management for Cisco SD-WAN?
• A. vBond
• B. vSmart
• C. vManage
• D. vEdge
A company plans to implement intent-based networking in its campus infrastructure.
Which design facilitates a migration from a traditional campus design to a programmable fabric design?
• A. two-tier
• B. Layer 2 access
• C. three-tier
• D. routed access
Which statement about a fabric access point is true?
• A. It is in local mode and must be connected directly to the fabric edge switch.
• B. It is in local mode and must be connected directly to the fabric border node.
• C. It is in FlexConnect mode and must be connected directly to the fabric border node.
• D. It is in FlexConnect mode and must be connected directly to the fabric edge switch.
A customer requests a network design that supports these requirements:
✑ FHRP redundancy
✑ multivendor router environment
✑ IPv4 and IPv6 hosts
Which protocol does the design include?
• A. VRRP version 2
• B. VRRP version 3
• C. GLBP
• D. HSRP version 2
While configuring an IOS router for HSRP with a virtual IP of 10.1.1.1, an engineer sees this log message.
Jan 1 12:12:12.111 : %HSRP-4-DIFFVIP1: GigabitEthernet0/0 Grp 1 active routers virtual IP address
10.1.1.1 is different to the locally configured address 10.1.1.25
Which configuration change must the engineer make?
• A. Change the HSRP group configuration on the local router to 1.
• B. Change the HSRP virtual address on the local router to 10.1.1.1.
• C. Change the HSRP virtual address on the remote router to 10.1.1.1.
• D. Change the HSRP group configuration on the remote router to 1.
A network administrator has designed a network with two multilayer switches on the distribution layer, which act as default gateways for the end hosts. Which two technologies allow every end host in a VLAN to use both gateways? (Choose two.)
• A. VRRP
• B. GLBP
• C. VSS
• D. MHSRP
• E. HSRP
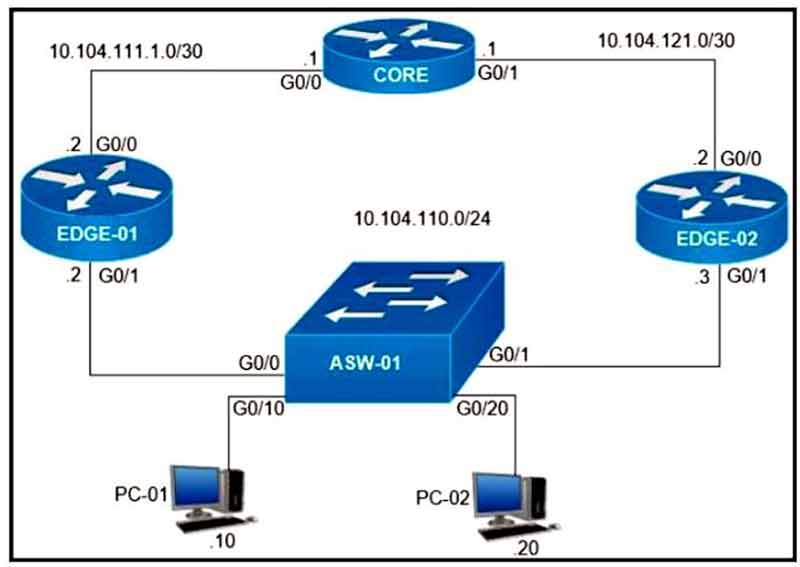
Refer to the exhibit. On which interfaces should VRRP commands be applied to provide first hop redundancy to PC-01 and PC-02?
• A. G0/0 and G0/1 on Core
• B. G0/0 on Edge-01 and G0/0 on Edge-02
• C. G0/1 on Edge-01 and G0/1 on Edge-02
• D. G0/0 and G0/1 on ASW-01
Under which network conditions is an outbound QoS policy that is applied on a router WAN interface most beneficial?
• A. under traffic classification and marking conditions
• B. under interface saturation conditions
• C. under all network conditions
• D. under network convergence conditions
An engineer must configure HSRP group 300 on a Cisco IOS router. When the router is functional, it must be the active HSRP router. The peer router has been configured using the default priority value.
Which command set is required?
• A. standby version 2 standby 300 priority 110 standby 300 preempt
• B. standby 300 priority 110 standby 300 timers 1 110
• C. standby version 2 standby 300 priority 90 standby 300 preempt
• D. standby 300 priority 90 standby 300 preempt
What is the function of a fabric border node in a Cisco SD-Access environment?
• A. To collect traffic flow information toward external networks.
• B. To connect the Cisco SD-Access fabric to another fabric or external Layer 3 networks.
• C. To attach and register clients to the fabric.
• D. To handle an ordered list of IP addresses and locations for endpoints in the fabric.
In a wireless Cisco SD-Access deployment, which roaming method is used when a user moves from one AP to another on a different access switch using a single WLC?
• A. Layer 3
• B. inter-xTR
• C. auto anchor
• D. fast roam
What is the recommended MTU size for a Cisco SD-Access Fabric?
• A. 4464
• B. 17914
• C. 9100
• D. 1500
What is the function of the fabric control plane node in a Cisco SD-Access deployment?
• A. It is responsible for policy application and network segmentation in the fabric.
• B. It performs traffic encapsulation and security profiles enforcement in the fabric.
• C. It holds a comprehensive database that tracks endpoints and networks in the fabric.
• D. It provides integration with legacy nonfabric-enabled environments.
What is the data policy in a Cisco SD-WAN deployment?
• A. list of ordered statements that define node configurations and authentication used within the SD-WAN overlay
• B. set of statements that defines how data is forwarded based on IP packet information and specific VPNs
• C. detailed database mapping several kinds of addresses with their corresponding location
• D. group of services tested to guarantee devices and links liveliness within the SD-WAN overlay
In Cisco SD-WAN, which protocol is used to measure link quality?
• A. IPsec
• B. OMP
• C. RSVP
• D. BFD
What is used to perform QoS packet classification?
• A. the Type field in the Layer 2 frame
• B. the Options field in the Layer 3 header
• C. the TOS field in the Layer 3 header
• D. the Flags field in the Layer 3 header
How do cloud deployments differ from on-premises deployments?
• A. Cloud deployments require longer implementation times than on-premises deployments.
• B. Cloud deployments are more customizable than on-premises deployments.
• C. Cloud deployments have lower upfront costs than on-premises deployments.
• D. Cloud deployments require less frequent upgrades than on-premises deployments.
Which controller is capable of acting as a STUN server during the onboarding process of Edge devices?
• A. vBond
• B. vSmart
• C. vManage
• D. PNP Server
How is 802.11 traffic handled in a fabric-enabled SSID?
• A. centrally switched back to WLC where the user traffic is mapped to a VXLAN on the WLC
• B. converted by the AP into 802.3 and encapsulated into VXLAN
• C. centrally switched back to WLC where the user traffic is mapped to a VLAN on the WLC
• D. converted by the AP into 802.3 and encapsulated into a VLAN
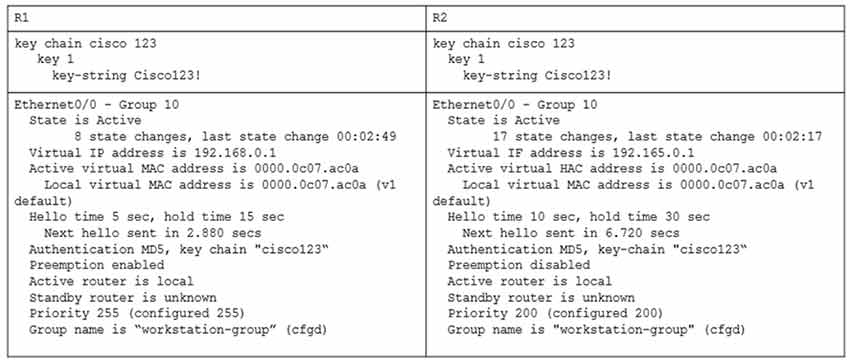
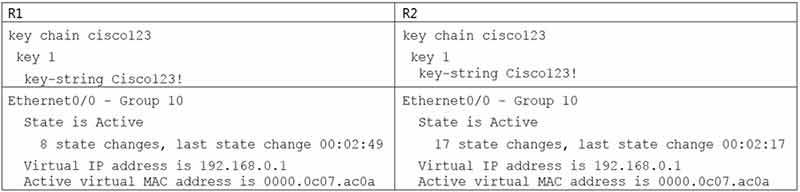
An engineer is installing a new pair of routers in a redundant configuration. When checking on the standby status of each router, the engineer notices that the routers are not functioning as expected.
Which action will resolve the configuration error?
• A. configure matching hold and delay timers
• B. configure matching key-strings
• C. configure matching priority values
• D. configure unique virtual IP addresses
Refer to the exhibit.

Router1 is currently operating as the HSRP primary with a priority of 110. Router1 fails and Router2 takes over the forwarding role. Which command on Router1 causes it to take over the forwarding role when it returns to service?
• A. standby 2 priority
• B. standby 2 preempt
• C. standby 2 track
• D. standby 2 timers
An engineer has deployed a single Cisco 5520 WLC with a management IP address of 172 16.50.5/24.
The engineer must register 50 new Cisco AIR-CAP2802I-
E-K9 access points to the WLC using DHCP option 43. The access points are connected to a switch in VLAN 100 that uses the 172.16.100.0/24 subnet. The engineer has configured the DHCP scope on the switch as follows:
Network 172.16.100.0 255.255.255.0
Default Router 172.16.100.1 –
Option 43 ASCII 172.16.50.5 –
The access points are failing to join the wireless LAN controller. Which action resolves the issue?
• A. configure option 43 Hex F104.AC10.3205
• B. configure option 43 Hex F104.CA10.3205
• C. configure dns-server 172.16.50.5
• D. configure dns-server 172. 16.100.1
What is the role of vSmart in a Cisco SD-WAN environment?
• A. to establish secure control plane connections
• B. to monitor, configure, and maintain SD-WAN devices
• C. to provide secure data plane connectivity over WAN links
• D. to perform initial authentication of devices
Which action is performed by Link Management Protocol in a Cisco StackWise Virtual domain?
• A. It determines which switch becomes active or standby.
• B. It determines if the hardware is compatible to form the StackWise Virtual domain.
• C. It rejects any unidirectional link traffic forwarding.
• D. It discovers the StackWise domain and brings up SVL interfaces.
What are two reasons why broadcast radiation is caused in the virtual machine environment? (Choose two.)
• A. vSwitch must interrupt the server CPU to process the broadcast packet.
• B. The Layer 2 domain can be large in virtual machine environments.
• C. Virtual machines communicate primarily through broadcast mode.
• D. Communication between vSwitch and network switch is broadcast based.
• E. Communication between vSwitch and network switch is multicast based.
Which two GRE features are configured to prevent fragmentation? (Choose two.)
• A. TCP window size
• B. IP MTU
• C. TCP MSS
• D. DF bit clear
• E. MTU ignore
Which LISP device is responsible for publishing EID-to-RLOC mappings for a site?
• A. ETR
• B. MR
• C. ITR
• D. MS
Refer to the exhibit.
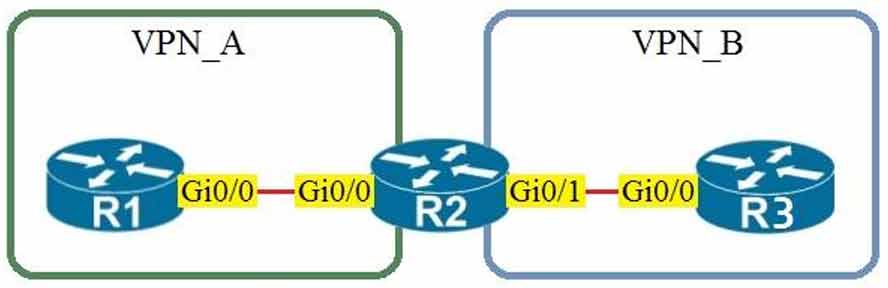
Assuming that R1 is a CE router, which VRF is assigned to Gi0/0 on R1?
• A. default VRF
• B. VRF VPN_A
• C. VRF VPN_B
• D. management VRF
What are two benefits of virtualizing the server with the use of VMs in a data center environment? (Choose two.)
• A. reduced rack space, power, and cooling requirements
• B. smaller Layer 2 domain
• C. increased security
• D. speedy deployment
• E. reduced IP and MAC address requirements
Which statement about route targets is true when using VRF-Lite?
• A. Route targets control the import and export of routes into a customer routing table.
• B. When BGP is configured, route targets are transmitted as BGP standard communities.
• C. Route targets allow customers to be assigned overlapping addresses.
• D. Route targets uniquely identify the customer routing table.
Which LISP infrastructure device provides connectivity between non-LISP sites and LISP sites by receiving non-LISP traffic with a LISP site destination?
• A. PITR
• B. map resolver
• C. map server
• D. PETR
Which statement explains why Type 1 hypervisor is considered more efficient than Type2 hypervisor?
• A. Type 1 hypervisor is the only type of hypervisor that supports hardware acceleration techniques.
• B. Type 1 hypervisor relies on the existing OS of the host machine to access CPU, memory, storage, and network resources.
• C. Type 1 hypervisor runs directly on the physical hardware of the host machine without relying on the underlying OS.
• D. Type 1 hypervisor enables other operating systems to run on it.
Which statement about VXLAN is true?
• A. VXLAN encapsulates a Layer 2 frame in an IP-UDP header, which allows Layer 2 adjacency across router boundaries.
• B. VXLAN uses the Spanning Tree Protocol for loop prevention.
• C. VXLAN extends the Layer 2 Segment ID field to 24-bits, which allows up to 4094 unique Layer 2 segments over the same network.
• D. VXLAN uses TCP as the transport protocol over the physical data center network.
Which TCP setting is tuned to minimize the risk of fragmentation on a GRE/IP tunnel?
• A. MSS
• B. MTU
• C. MRU
• D. window size
Which statement describes the IP and MAC allocation requirements for virtual machines on Type 1 hypervisors?
• A. Virtual machines do not require a unique IP or unique MAC. They share the IP and MAC address of the physical server.
• B. Each virtual machine requires a unique IP address but shares the MAC address with the physical server.
• C. Each virtual machine requires a unique IP and MAC addresses to be able to reach to other nodes.
• D. Each virtual machine requires a unique MAC address but shares the IP address with the physical server.
Which two namespaces does the LISP network architecture and protocol use? (Choose two.)
• A. TLOC
• B. RLOC
• C. DNS
• D. VTEP
• E. EID
Which two entities are Type 1 hypervisors? (Choose two.)
• A. Oracle VM VirtualBox
• B. Microsoft Hyper-V
• C. VMware server
• D. VMware ESXi
• E. Microsoft Virtual PC
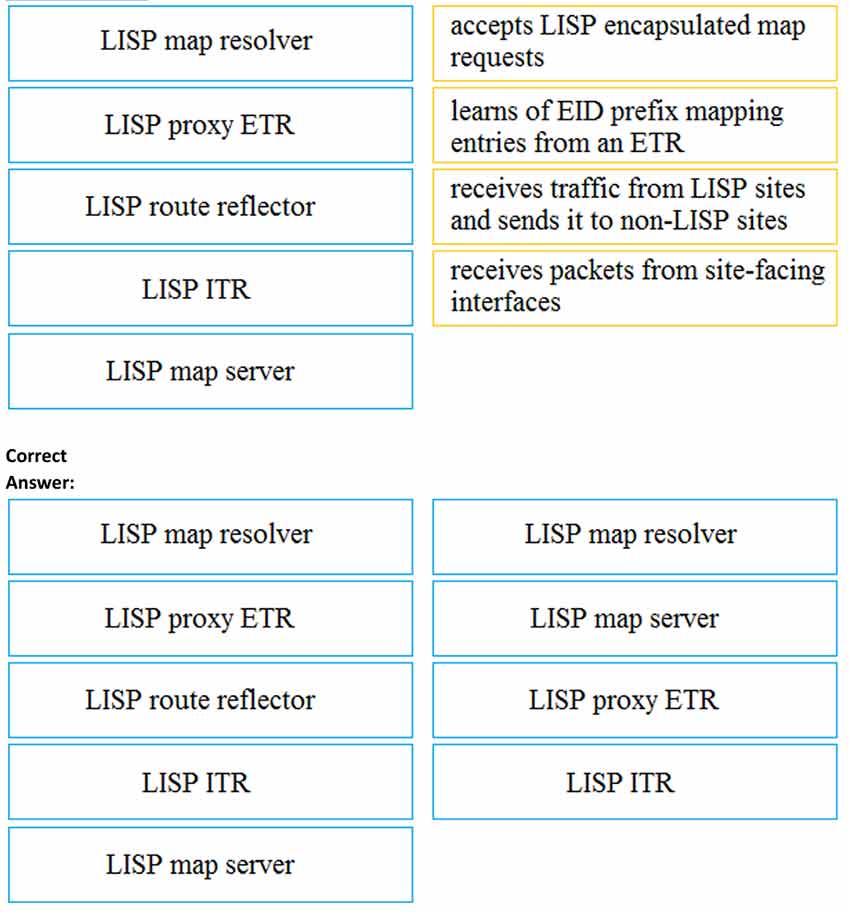
DRAG DROP –
Drag and drop the LISP components from the left onto the functions they perform on the right. Not all options are used.
Select and Place
Which action is a function of VTEP in VXLAN?
• A. tunneling traffic from IPv6 to IPv4 VXLANs
• B. allowing encrypted communication on the local VXLAN Ethernet segment
• C. encapsulating and de-encapsulating VXLAN Ethernet frames
• D. tunneling traffic from IPv4 to IPv6 VXLANs
Which two actions provide controlled Layer 2 network connectivity between virtual machines running on the same hypervisor? (Choose two.)
• A. Use a virtual switch provided by the hypervisor.
• B. Use a virtual switch running as a separate virtual machine.
• C. Use VXLAN fabric after installing VXLAN tunneling drivers on the virtual machines.
• D. Use a single routed link to an external router on stick.
• E. Use a single trunk link to an external Layer2 switch.
What is a Type 1 hypervisor?
• A. runs directly on a physical server and depends on a previously installed operating system
• B. runs directly on a physical server and includes its own operating system
• C. runs on a virtual server and depends on an already installed operating system
• D. runs on a virtual server and includes its own operating system
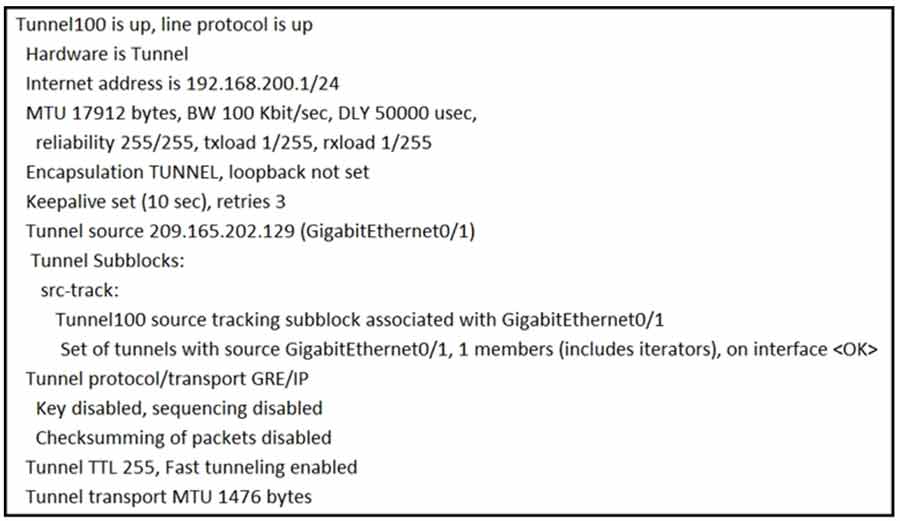
Refer to the exhibit. A network engineer configures a GRE tunnel and enters the show interface
tunnel command. What does the output confirm about the configuration?
• A. The keepalive value is modified from the default value.
• B. The physical interface MTU is 1476 bytes.
• C. The tunnel mode is set to the default.
• D. Interface tracking is configured.
What it the purpose of the LISP routing and addressing architecture?
• A. It creates two entries for each network node, one for its identity and another for its location on the network.
• B. It allows LISP to be applied as a network virtualization overlay though encapsulation.
• C. It allows multiple instances of a routing table to co-exist within the same router.
• D. It creates head-end replication used to deliver broadcast and multicast frames to the entire network.
What function does VXLAN perform in a Cisco SD-Access deployment?
• A. policy plane forwarding
• B. control plane forwarding
• C. data plane forwarding
• D. systems management and orchestration
Refer to the exhibit.
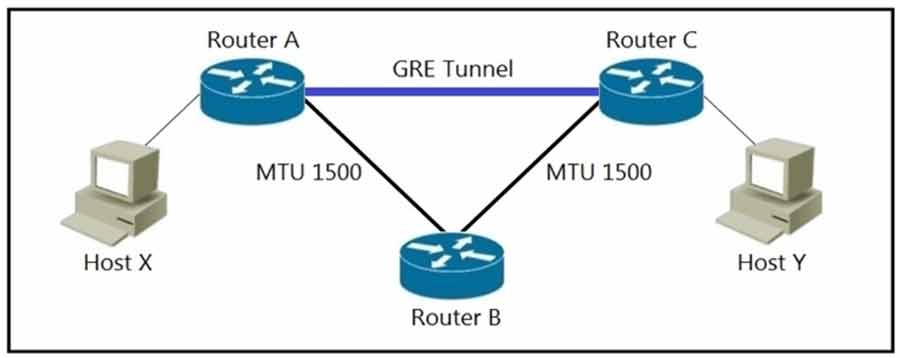
MTU has been configured on the underlying physical topology, and no MTU command has been configured on the tunnel interfaces.
What happens when a 1500-byte IPv4 packet traverses the GRE tunnel from host X to host Y, assuming the DF bit is cleared?
• A. The packet is discarded on router B
• B. The packet arrives on router C without fragmentation
• C. The packet arrives on router C fragmented
• D. The packet is discarded on router A
Which entity is responsible for maintaining Layer 2 isolation between segments in a VXLAN environment?
• A. VNID
• B. switch fabric
• C. VTEP
• D. host switch
What is an emulated machine that has dedicated compute, memory, and storage resources and a fully installed operating system?
• A. mainframe
• B. host
• C. virtual machine
• D. container
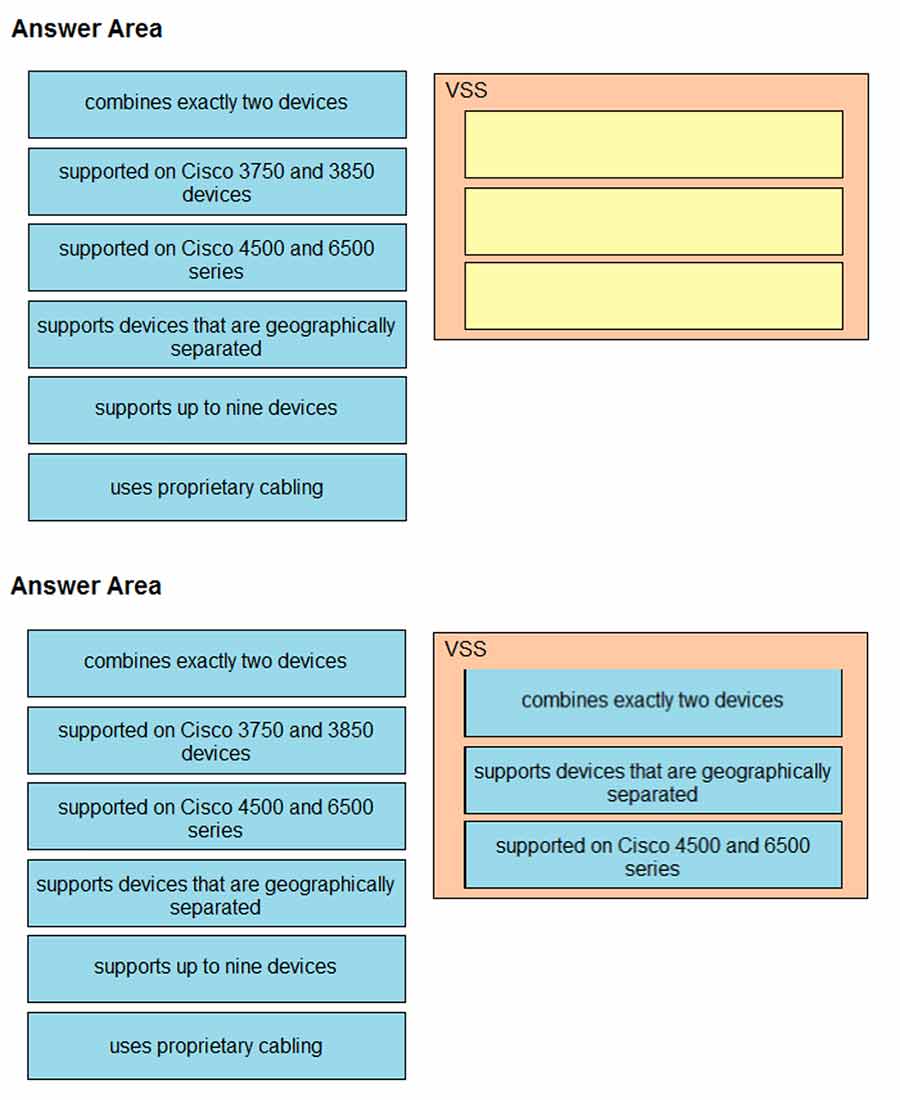
DRAG DROP –
Drag and drop the descriptions of the VSS technology from the left to the right. Not all options are used.
Which technology does VXLAN use to provide segmentation for Layer 2 and Layer 3 traffic?
• A. bridge domain
• B. VLAN
• C. VNI
• D. VRF
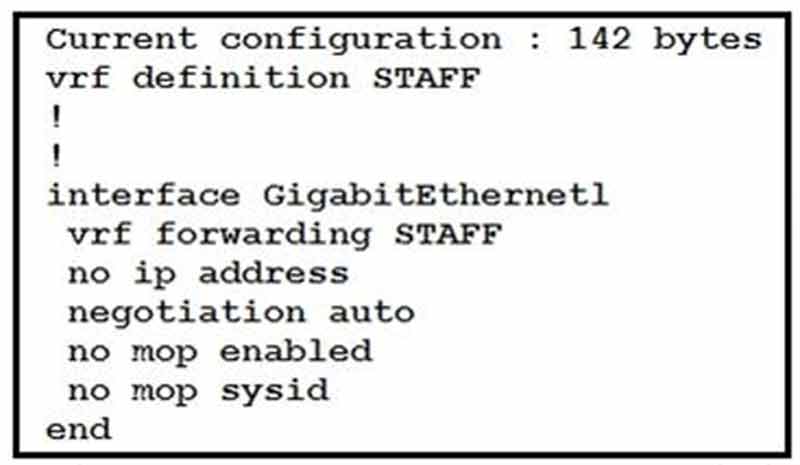
Refer to the exhibit. An engineer must assign an IP address of 192.168.1.1/24 to the GigabitEthernet1 interface. Which two commands must be added to the existing configuration to accomplish this task? (Choose two.)
• A. Router(config-if)#ip address 192.168.1.1 255.255.255.0
• B. Router(config-vrf)#address-family ipv4
• C. Router(config-vrf)#ip address 192.168.1.1 255.255.255.0
• D. Router(config-if)#address-family ipv4
• E. Router(config-vrf)#address-family ipv6
The following system log message is presented after a network administrator configures a GRE tunnel:
%TUN-RECURDOWN Interface Tunnel 0 temporarily disabled due to recursive routing Why is Tunnel 0 disabled?
• A. Because dynamic routing is not enabled.
• B. Because the tunnel cannot reach its tunnel destination.
• C. Because the best path to the tunnel destination is through the tunnel itself.
• D. Because the router cannot recursively identify its egress forwarding interface.
What is a benefit of using a Type 2 hypervisor instead of a Type 1 hypervisor?
• A. better application performance
• B. improved security because the underlying OS is eliminated
• C. improved density and scalability
• D. ability to operate on hardware that is running other OSs
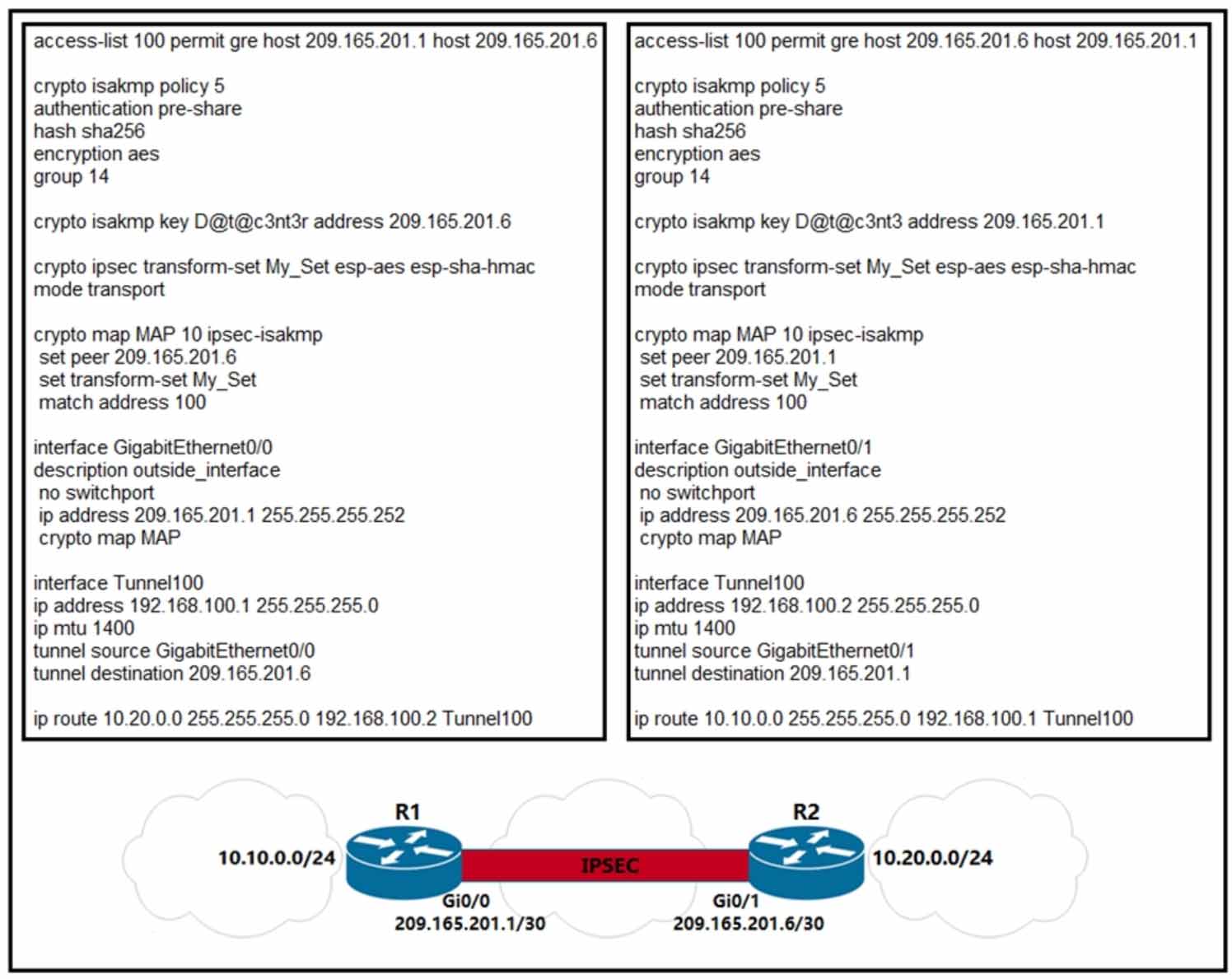
Refer to the exhibit. A network engineer must simplify the IPsec configuration by enabling IPsec over GRE using IPsec profiles. Which two configuration changes accomplish this? (Choose two).
• A. Create an IPsec profile, associate the transform-set ACL, and apply the profile to the tunnel interface.
• B. Apply the crypto map to the tunnel interface and change the tunnel mode to tunnel mode ipsec ipv4.
• C. Remove all configuration related to crypto map from R1 and R2 and eliminate the ACL.
• D. Create an IPsec profile, associate the transform-set, and apply the profile to the tunnel interface.
• E. Remove the crypto map and modify the ACL to allow traffic between 10.10.0.0/24 to 10.20.0.0/24.
What is a benefit of a virtual machine when compared with a physical server?
• A. Multiple virtual servers can be deployed on the same physical server without having to buy additional hardware.
• B. Virtual machines increase server processing performance.
• C. The CPU and RAM resources on a virtual machine cannot be affected by other virtual machines.
• D. Deploying a virtual machine is technically less complex than deploying a physical server.
What is required for a virtual machine to run?
• A. a Type 1 hypervisor and a host operating system
• B. a hypervisor and physical server hardware
• C. only a Type 1 hypervisor
• D. only a Type 2 hypervisor
Which entity is a Type 1 hypervisor?
• A. Oracle VM VirtualBox
• B. Citrix XenServer
• C. VMware server
• D. Microsoft Virtual PC
What are two benefits of virtual switching when compared to hardware switching? (Choose two.)
• A. increased MTU size
• B. VM-level isolation
• C. extended 802.1Q VLAN range
• D. hardware independence
• E. increased flexibility
What is a characteristic of a virtual machine?
• A. It must run the same operating system as its host.
• B. It is deployable without a hypervisor to host it.
• C. It must be aware of other virtual machines, in order to allocate physical resources for them.
• D. It relies on hypervisors to allocate computing resources for it.
Which LISP component is required for a LISP site to communicate with a non-LISP site?
• A. Proxy ITR
• B. ITR
• C. ETR
• D. Proxy ETR
Which two components are supported by LISP? (Choose two.)
• A. proxy ETR
• B. egress tunnel router
• C. route reflector
• D. HMAC algorithm
• E. spoke
What is the function of a VTEP in VXLAN?
• A. provide the routing underlay and overlay for VXLAN headers
• B. dynamically discover the location of end hosts in a VXLAN fabric
• C. encapsulate and de-encapsulate traffic into and out of the VXLAN fabric
• D. statically point to end host locations of the VXLAN fabric
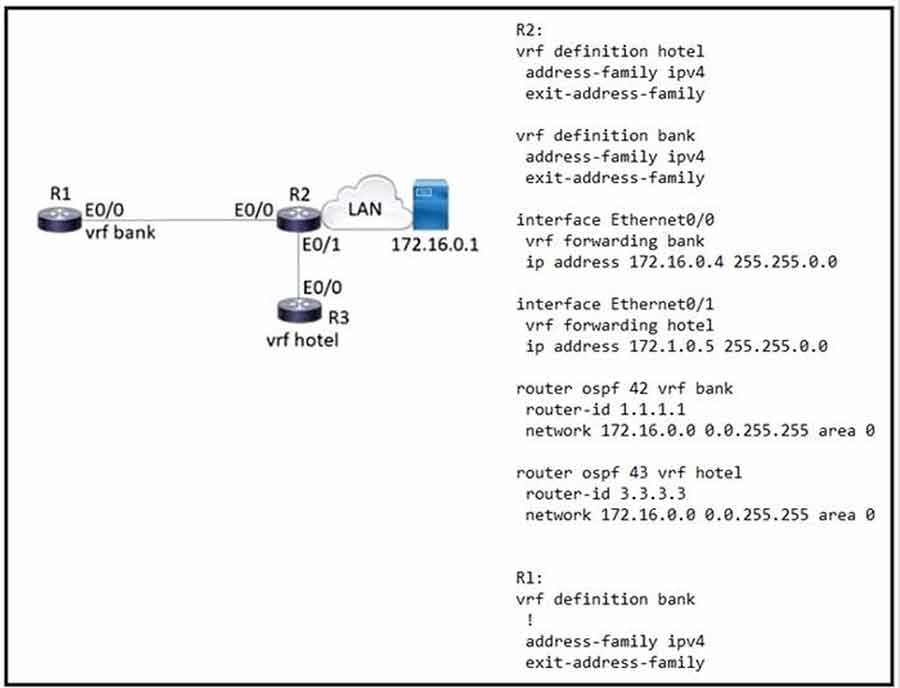
Refer to the exhibit. Which configuration must be applied to R1 to enable R1 to reach the server at 172.16.0.1?
• A. interface Ethernet0/0 ip address 172.16.0.7 255.255.0.0 router ospf 44 vrf bank network 172.16.0.0 255.255.0.0
• B. interface Ethernet0/0 vrf forwarding hotel ip address 172.16.0.7 255.255.0.0 router ospf 44 vrf Hotel network 172.16.0.0 0.0.255.255 area 0
• C. interface Ethernet0/0 vrf forwarding bank ip address 172.16.0.7 255.255.0.0 router ospf 44 vrf bank network 172.16.0.0 0.0.255.255 area 0
• D. interface Ethernet0/0 ip address 172.16.0.7 255.255.0.0 router ospf 44 vrf hotel network 172.16.0.0 255.255.0.0
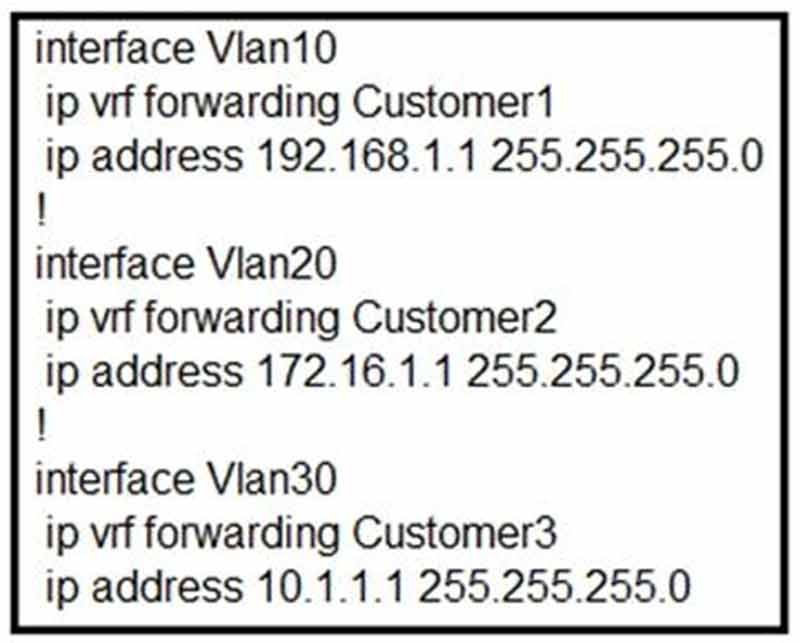
Refer to the exhibit. Which configuration allows Customer2 hosts to access the FTP server of Customer1 that has the IP address of 192.168.1.200?
• A. ip route vrf Customer1 172.16.1.0 255.255.255.0 172.16.1.1 global ip route vrf Customer2 192.168.1.200 255.255.255.255 192.168.1.1 global ip route 192.168.1.0 255.255.255.0 Vlan10 ip route 172.16.1.0 255.255.255.0 Vlan20
• B. ip route vrf Customer1 172.16.1.1 255.255.255.255 172.16.1.1 global ip route vrf Customer2 192.168.1.200 255.255.255.0 192.168.1.1 global ip route 192.168.1.0 255.255.255.0 Vlan10 ip route 172.16.1.0 255.255.255.0 Vlan20
• C. ip route vrf Customer1 172.16.1.0 255.255.255.0 172.16.1.1 Customer2 ip route vrf Customer2 192.168.1.200 255.255.255.255 192.168.1.1 Customer1
• D. ip route vrf Customer1 172.16.1.0 255.255.255.0 172.16.1.1 Customer1 ip route vrf Customer2 192.168.1.200 255.255.255.255 192.168.1.1 Customer2
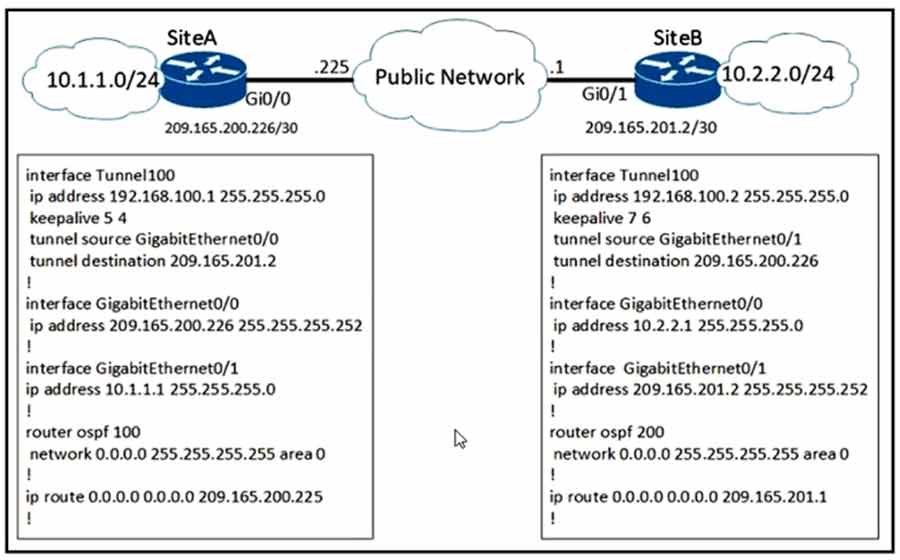
Refer to the exhibit. A network engineer configures a new GRE tunnel and enters the show run command. What does the output verify?
• A. The tunnel keepalive is configured incorrectly because they must match on both sites.
• B. The tunnel destination will be known via the tunnel interface.
• C. The tunnel will be established and work as expected.
• D. The default MTU of the tunnel interface is 1500 bytes.
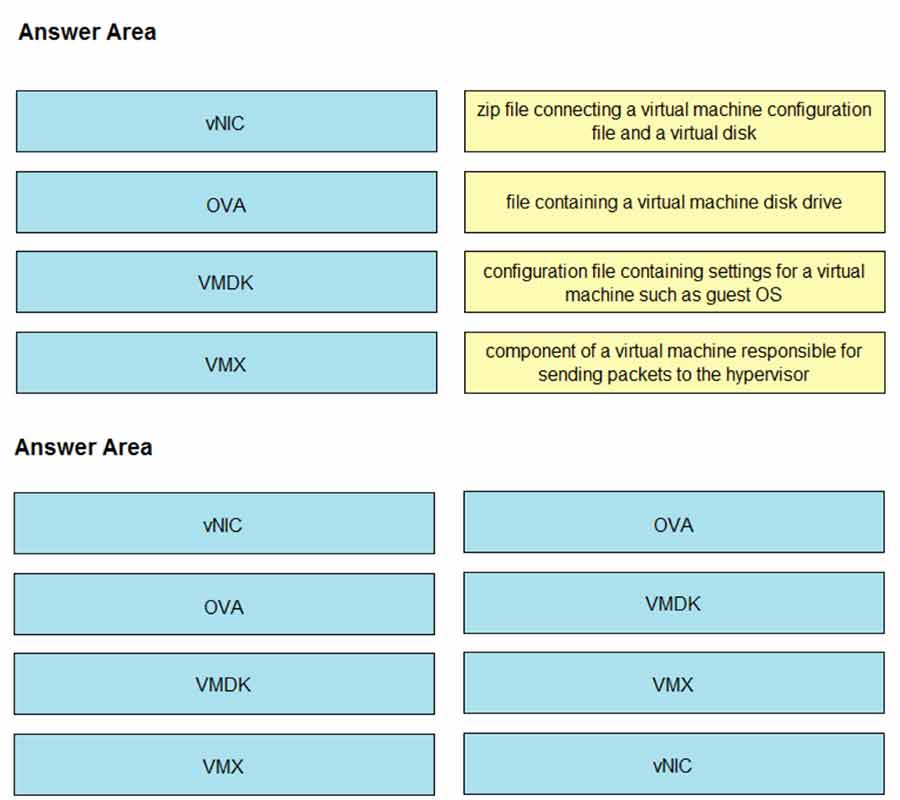
DRAG DROP –
Drag and drop the virtual components from the left onto their descriptions on the right.
Select and Place:
Which element enables communication between guest VMs within a virtualized environment?
• A. hypervisor
• B. virtual router
• C. vSwitch
• D. pNIC
Which two methods are used to reduce the AP coverage area? (Choose two.)
• A. Reduce channel width from 40 MHz to 20 MHz.
• B. Reduce AP transmit power.
• C. Enable Fastlane.
• D. Increase minimum mandatory data rate.
• E. Disable 2.4 GHz and use only 5 GHz.
Which antenna type should be used for a site-to-site wireless connection?
• A. patch
• B. dipole
• C. omnidirectional
• D. Yagi
In a wireless network environment, what is calculated using the numerical values of the transmitter power level, cable loss, and antenna gain?
• A. SNR
• B. RSSI
• C. EIRP
• D. dBi
What does the LAP send when multiple WLCs respond to the CISCO-CAPWAP CONTROLLER.localdomain hostname during the CAPWAP discovery and join process?
• A. unicast discovery request to the first WLC that resolves the domain name
• B. broadcast discovery request
• C. join request to all the WLCs
• D. unicast discovery request to each WLC
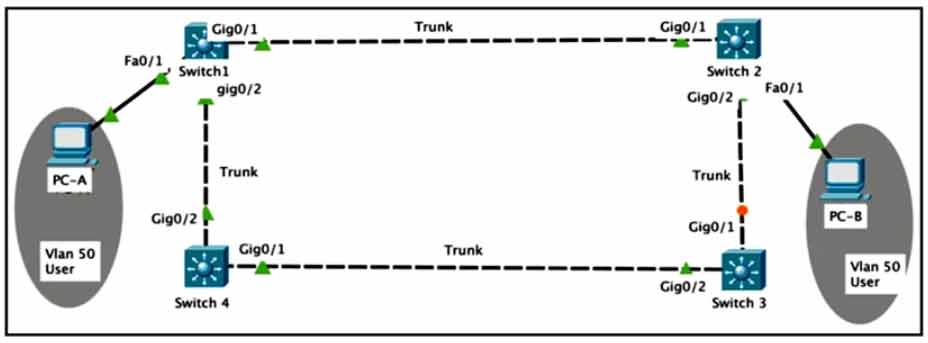
Refer to the exhibit.
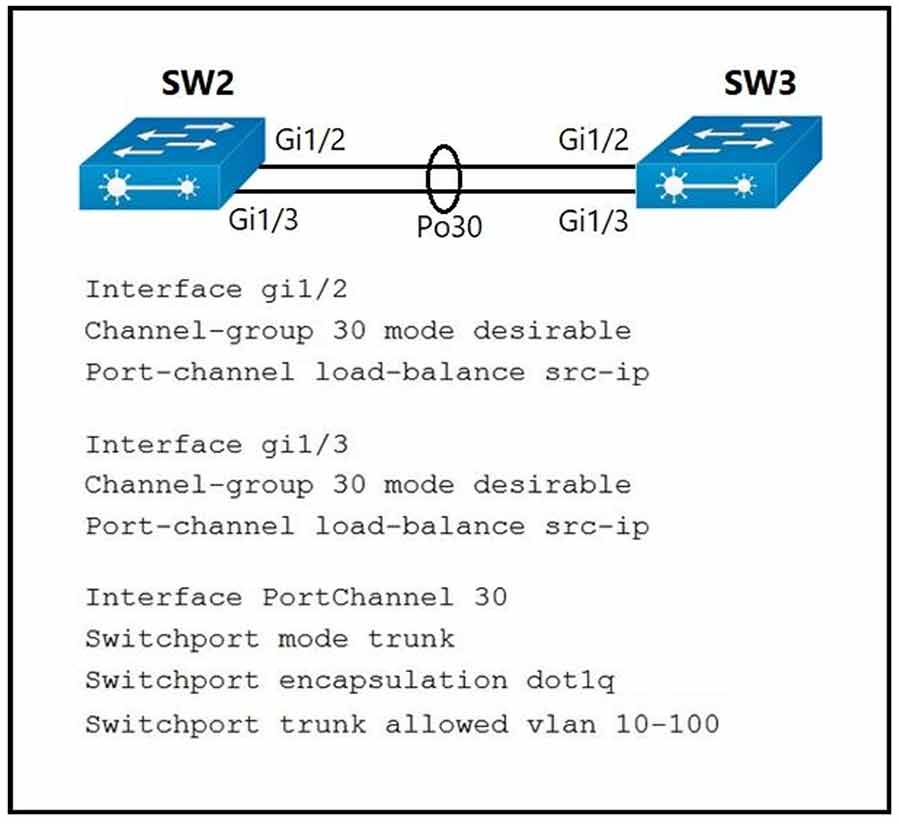
A port channel is configured between SW2 and SW3. SW2 is not running a Cisco operating system.
When all physical connections are made, the port channel does not establish.
Based on the configuration excerpt of SW3, what is the cause of the problem?
• A. The port-channel mode should be set to auto.
• B. The port channel on SW2 is using an incompatible protocol.
• C. The port-channel trunk is not allowing the native VLAN.
• D. The port-channel interface load balance should be set to src-mac.
What is a fact about Cisco EAP-FAST?
• A. It requires a client certificate.
• B. It is an IETF standard.
• C. It does not require a RADIUS server certificate.
• D. It operates in transparent mode.
Which DNS lookup does an access point perform when attempting CAPWAP discovery?
• A. CISCO-CONTROLLER.local
• B. CAPWAP-CONTROLLER.local
• C. CISCO-CAPWAP-CONTROLLER.local
• D. CISCO-DNA-CONTROLLER.local
Refer to the exhibit.
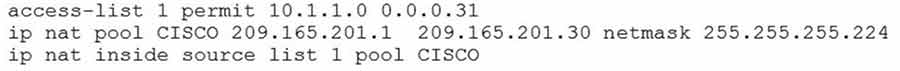
What are two effects of this configuration? (Choose two.)
• A. It establishes a one-to-one NAT translation.
• B. The 209.165.201.0/27 subnet is assigned as the outside local address range.
• C. The 10.1.1.0/27 subnet is assigned as the inside local addresses.
• D. Inside source addresses are translated to the 209.165.201.0/27 subnet.
• E. The 10.1.1.0/27 subnet is assigned as the inside global address range.
An engineer configures a WLAN with fast transition enabled. Some legacy clients fail to connect to this WLAN.
Which feature allows the legacy clients to connect while still allowing other clients to use fast transition based on their OUIs?
• A. over the DS
• B. 802.11k
• C. adaptive R
• D. 802.11v
What are two common sources of interference for Wi-Fi networks? (Choose two.)
• A. LED lights
• B. radar
• C. fire alarm
• D. conventional oven
• E. rogue AP
Which two pieces of information are necessary to compute SNR? (Choose two.)
• A. transmit power
• B. noise floor
• C. EIRP
• D. RSSI
• E. antenna gain
Which OSPF network types are compatible and allow communication through the two peering devices?
• A. point-to-multipoint to nonbroadcast
• B. broadcast to nonbroadcast
• C. point-to-multipoint to broadcast
• D. broadcast to point-to-point
Refer to the exhibit.
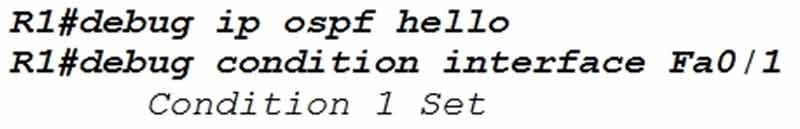
Which statement about the OSPF debug output is true?
• A. The output displays OSPF hello messages which router R1 has sent or received on interface Fa0/1.
• B. The output displays all OSPF messages which router R1 has sent or received on all interfaces.
• C. The output displays all OSPF messages which router R1 has sent or received on interface Fa0/1.
• D. The output displays OSPF hello and LSACK messages which router R1 has sent or received.
Which statement about multicast RPs is true?
• A. RPs are required only when using protocol independent multicast dense mode.
• B. RPs are required for protocol independent multicast sparse mode and dense mode.
• C. By default, the RP is needed periodically to maintain sessions with sources and receivers.
• D. By default, the RP is needed only to start new sessions with sources and receivers.
To increase total throughput and redundancy on the links between the wireless controller and switch, the customer enabled LAG on the wireless controller.
Which EtherChannel mode must be configured on the switch to allow the WLC to connect?
• A. Active
• B. Passive
• C. On
• D. Auto
Based on this interface configuration, what is the expected state of OSPF adjacency?
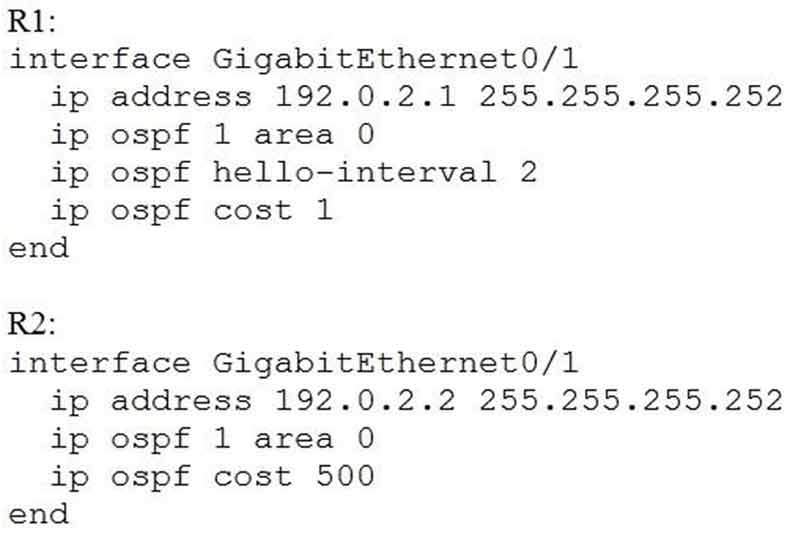
• A. 2WAY/DROTHER on both routers
• B. not established
• C. FULL on both routers
• D. FULL/BDR on R1 and FULL/BDR on R2
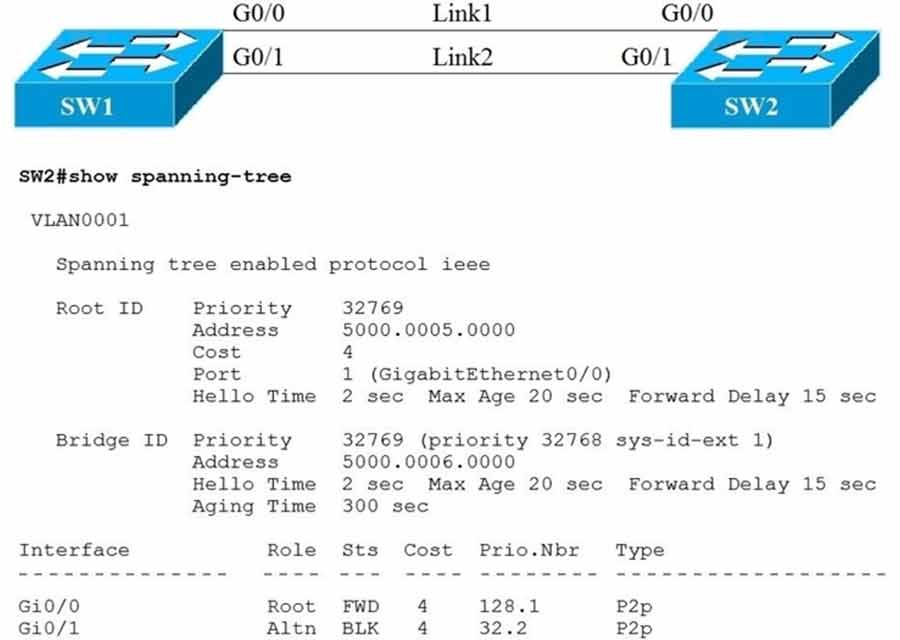
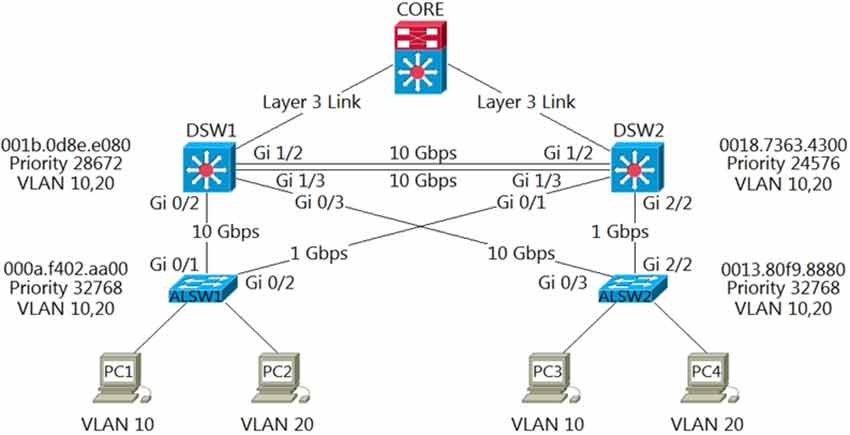
Link1 is a copper connection and Link2 is a fiber connection. The fiber port must be the primary port for all forwarding. The output of the show spanning-tree command on SW2 shows that the fiber port is blocked by spanning tree. An engineer enters the spanning-tree port-priority 32 command on G0/1 on SW2, but the port remains blocked.
Which command should be entered on the ports that are connected to Link2 to resolve the issue?
• A. Enter spanning-tree port-priority 4 on SW2.
• B. Enter spanning-tree port-priority 32 on SW1.
• C. Enter spanning-tree port-priority 224 on SW1.
• D. Enter spanning-tree port-priority 64 on SW2.
Which behavior can be expected when the HSRP version is changed from 1 to 2?
• A. No changes occur because the standby router is upgraded before the active router.
• B. No changes occur because version 1 and 2 use the same virtual MAC OUI.
• C. Each HSRP group reinitializes because the virtual MAC address has changed.
• D. Each HSRP group reinitializes because the multicast address has changed.
Refer to the exhibit.
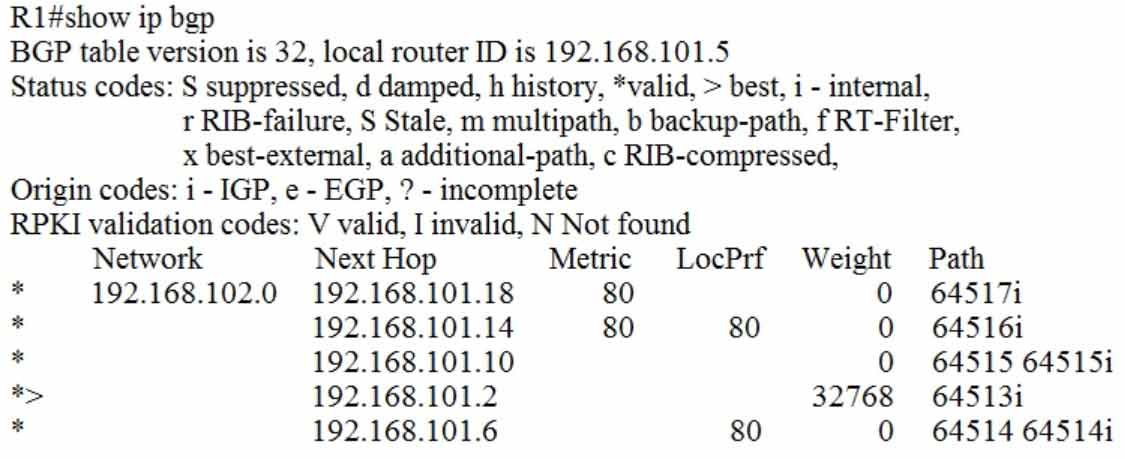
Which IP address becomes the active next hop for 192.168.102.0/24 when 192.168.101.2 fails?
• A. 192.168.101.10
• B. 192.168.101.14
• C. 192.168.101.6
• D. 192.168.101.18
Which PAgP mode combination prevents an EtherChannel from forming?
• A. auto/desirable
• B. desirable/desirable
• C. desirable/auto
• D. auto/auto
If a VRRP master router fails, which router is selected as the new master router?
• A. router with the lowest priority
• B. router with the highest priority
• C. router with the highest loopback address
• D. router with the lowest loopback address
Which two mechanisms are available to secure NTP? (Choose two.)
• A. IPsec
• B. IP prefix list-based
• C. encrypted authentication
• D. TACACS-based authentication
• E. IP access list-based
In OSPF, which LSA type is responsible for pointing to the ASBR router?
• A. type 1
• B. type 2
• C. type 3
• D. type 4
Refer to the exhibit.

VLANs 50 and 60 exist on the trunk links between all switches. All access ports on SW3 are configured for VLAN 50 and SW1 is the VTP server.
Which command ensures that SW3 receives frames only from VLAN 50?
• A. SW1(config)#vtp mode transparent
• B. SW3(config)#vtp mode transparent
• C. SW2(config)#vtp pruning
• D. SW1(config)#vtp pruning
Which First Hop Redundancy Protocol maximizes uplink utilization and minimizes the amount of configuration that is necessary?
• A. GLBP
• B. HSRP v2
• C. VRRP
• D. HSRP v1
Refer to the exhibit.
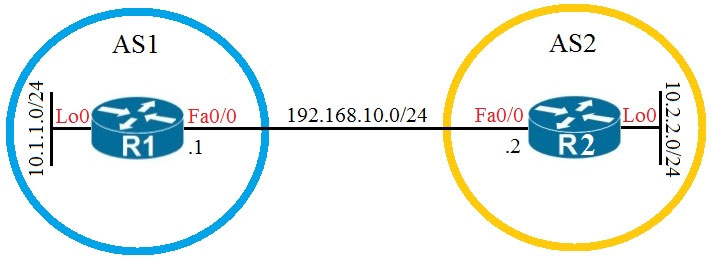
Which configuration establishes EBGP neighborship between these two directly connected neighbors and exchanges the loopback network of the two routers through BGP?
• A. R1(config)#router bgp 1 R1(config-router)#neighbor 192.168.10.2 remote-as 2 R1(config router)#network 10.1.1.0 mask 255.255.255.0 R2(config)#router bgp 2 R2(config router)#neighbor 192.168.10.1 remote-as 1 R2(config-router)#network 10.2.2.0 mask 255.255.255.0
• B. R1(config)#router bgp 1 R1(config-router)#neighbor 10.2.2.2 remote-as 2 R1(config router)#network 10.1.1.0 mask 255.255.255.0 R2(config)#router bgp 2 R2(config router)#neighbor 10.1.1.1 remote-as 1 R2(config-router)#network 10.2.2.0 mask 255.255.255.0
• C. R1(config)#router bgp 1 R1(config-router)#neighbor 192.168.10.2 remote-as 2 R1(config router)#network 10.0.0.0 mask 255.0.0.0 R2(config)#router bgp 2 R2(config router)#neighbor 192.168.10.1 remote-as 1 R2(config-router)#network 10.0.0.0 mask 255.0.0.0
• D. R1(config)#router bgp 1 R1(config-router)#neighbor 10.2.2.2 remote-as 2 R1(config router)#neighbor 10.2.2.2 update-source lo0 R1(config-outer)#network 10.1.1.0 mask 255.255.255.0 R2(config)#router bgp 2 R2(config-router)#neighbor 10.1.1.1 remote-as 1 R2(config-router)#neighbor 10.1.1.1 update-source lo0 R2(config-router)#network 10.2.2.0 mask 255.255.255.0
Refer to the exhibit.
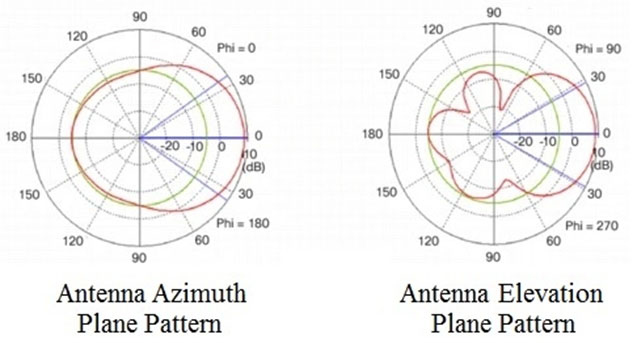
Which type of antenna do the radiation patterns present?
• A. Yagi
• B. patch
• C. omnidirectional
• D. dipole
Which reason could cause an OSPF neighborship to be in the EXSTART/EXCHANGE state?
• A. mismatched OSPF link costs
• B. mismatched OSPF network type
• C. mismatched areas
• D. mismatched MTU size
When configuring WPA2 Enterprise on a WLAN, which additional security component configuration is required?
• A. PKI server
• B. NTP server
• C. RADIUS server
• D. TACACS server
A customer has several small branches and wants to deploy a Wi-Fi solution with local management using CAPWAP.
Which deployment model meets this requirement?
• A. local mode
• B. autonomous
• C. SD-Access wireless
• D. Mobility Express
Refer to the exhibit.
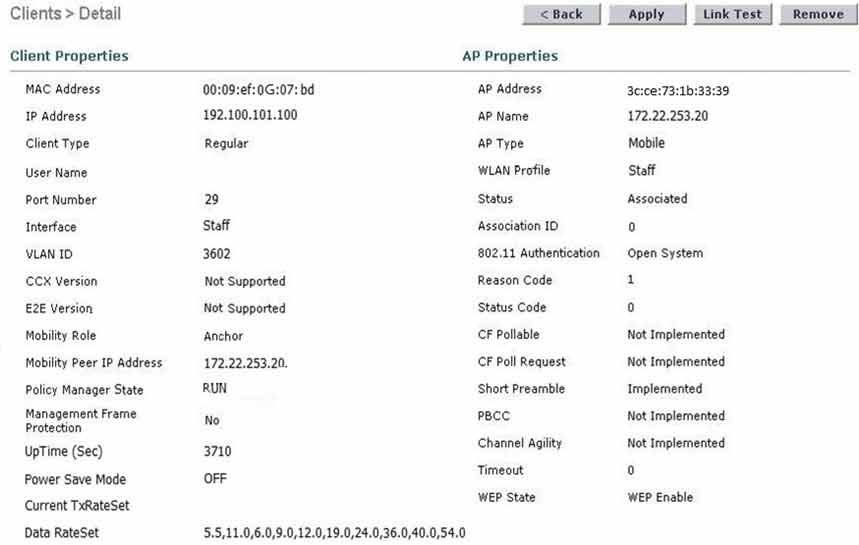
The WLC administrator sees that the controller to which a roaming client associates has Mobility Role Anchor configured under Clients > Detail.
Which type of roaming is supported?
• A. indirect
• B. Layer 3 intercontroller
• C. intracontroller
• D. Layer 2 intercontroller
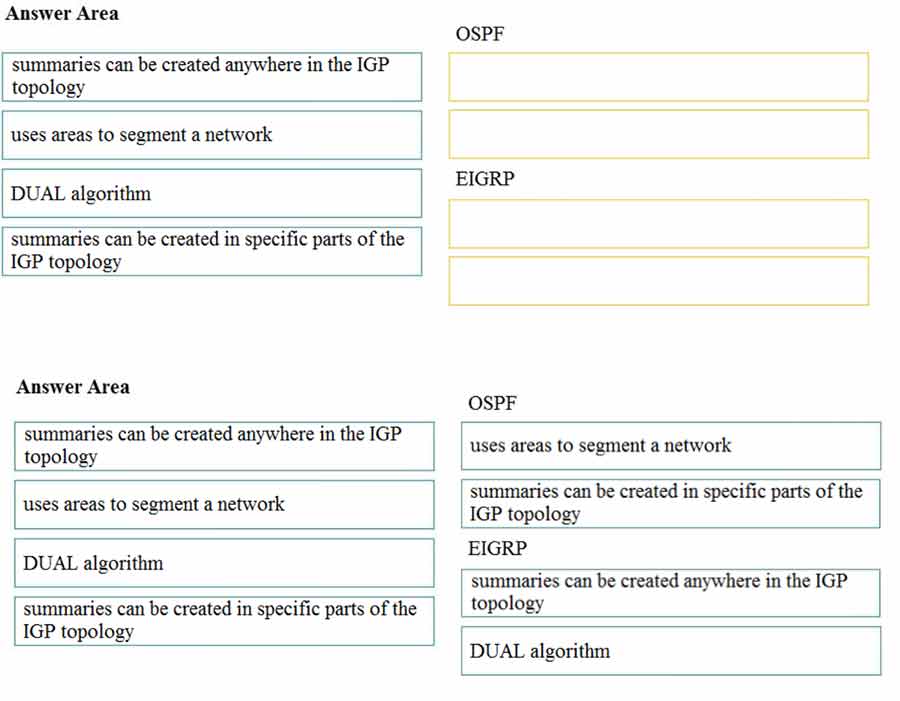
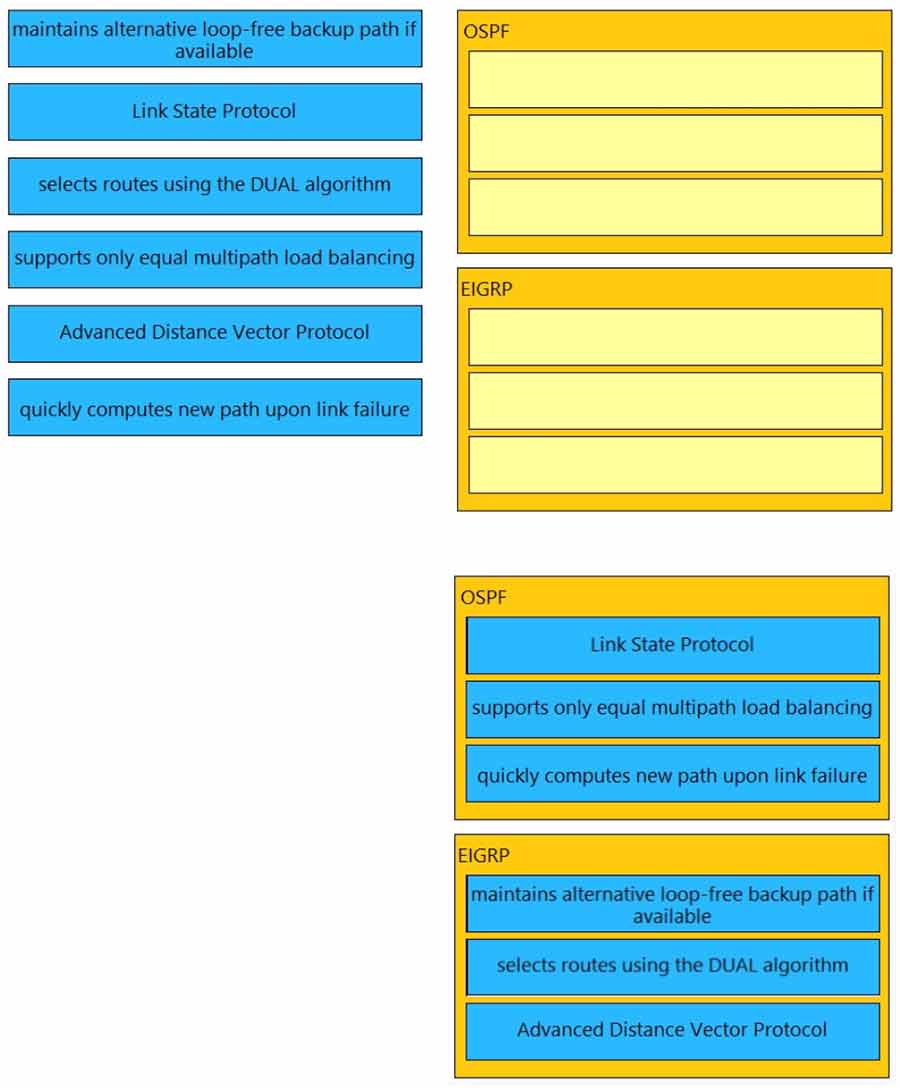
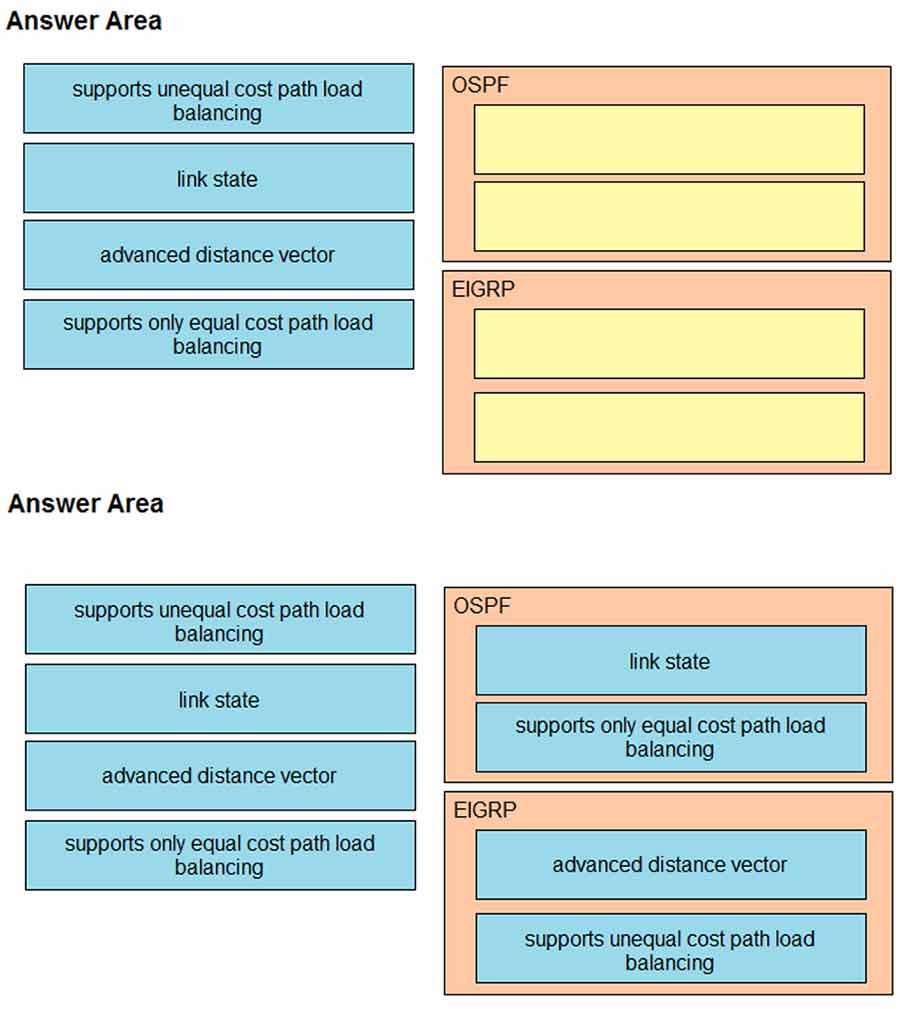
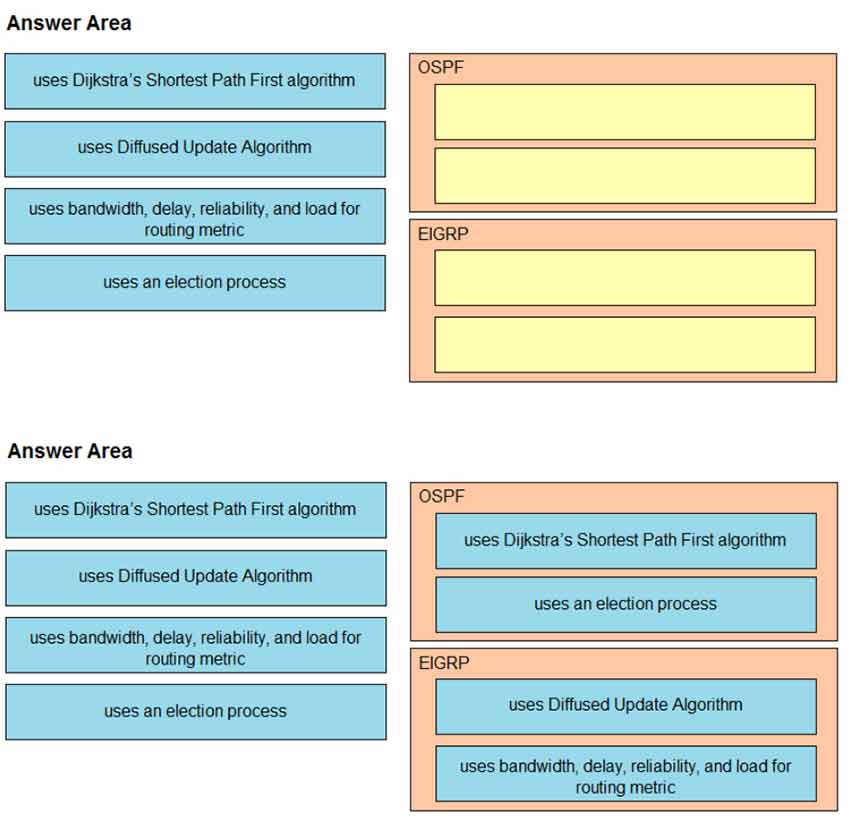
DRAG DROP –
Drag and drop the characteristics from the left onto the correct routing protocol types on the right.
Select and Place:
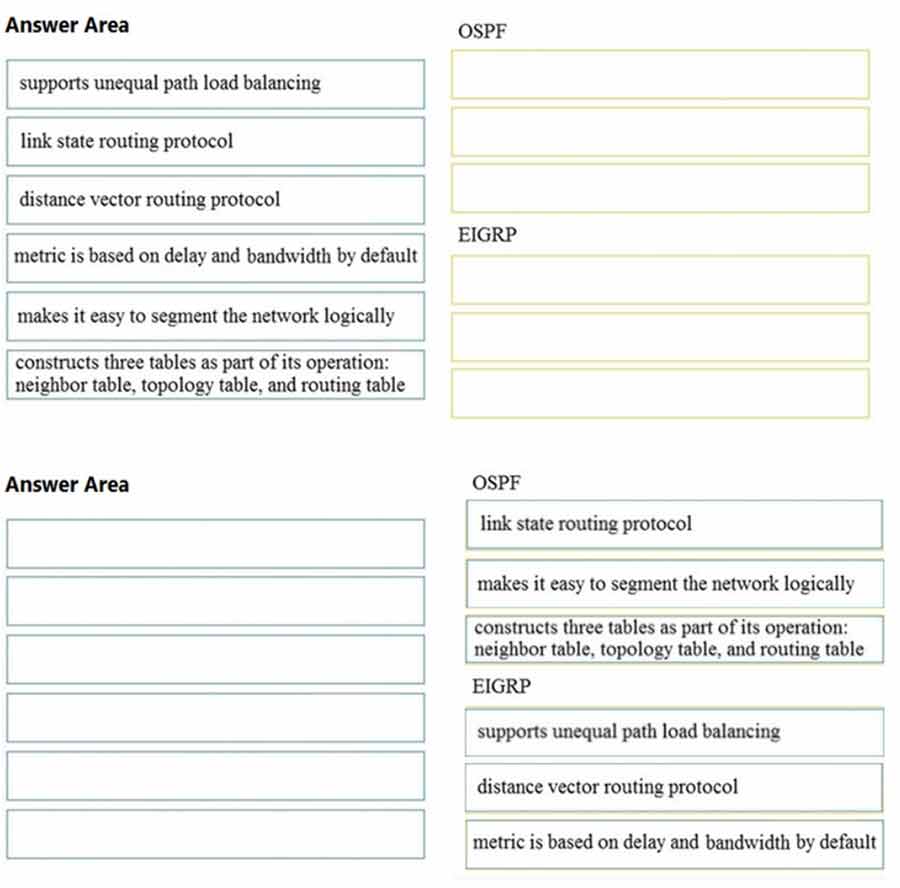
Which feature is supported by EIGRP but is not supported by OSPF?
• A. route filtering
• B. unequal-cost load balancing
• C. route summarization
• D. equal-cost load balancing
What is the correct EBGP path attribute list, ordered from most preferred to least preferred, that the BGP best-path algorithm uses?
• A. local preference, weight, AS path, MED
• B. weight, local preference, AS path, MED
• C. weight, AS path, local preference, MED
• D. local preference, weight, MED, AS path
A local router shows an EBGP neighbor in the Active state.
Which statement is true about the local router?
• A. The local router is attempting to open a TCP session with the neighboring router.
• B. The local router is receiving prefixes from the neighboring router and adding them in RIB IN.
• C. The local router has active prefixes in the forwarding table from the neighboring router.
• D. The local router has BGP passive mode configured for the neighboring router.
Refer to the exhibit.
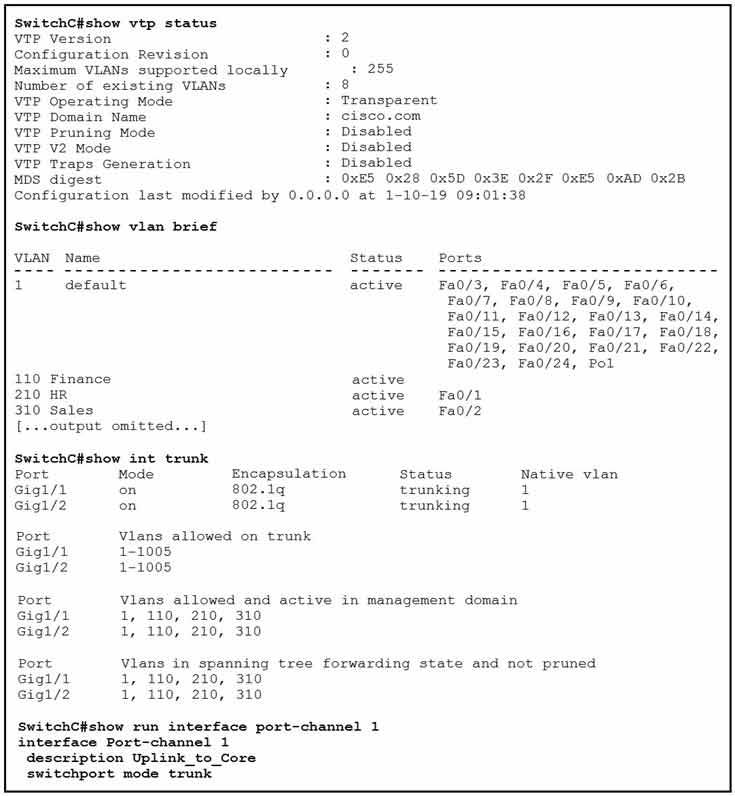
SwitchC connects HR and Sales to the Core switch. However, business needs require that no traffic from the Finance VLAN traverse this switch.
Which command meets this requirement?
• A. SwitchC(config)#vtp pruning vlan 110
• B. SwitchC(config)#vtp pruning
• C. SwitchC(config)#interface port-channel 1 SwitchC(config-if)#switchport trunk allowed vlan add 210,310
• D. SwitchC(config)#interface port-channel 1 SwitchC(config-if)#switchport trunk allowed vlan remove 110
Refer to the exhibit.
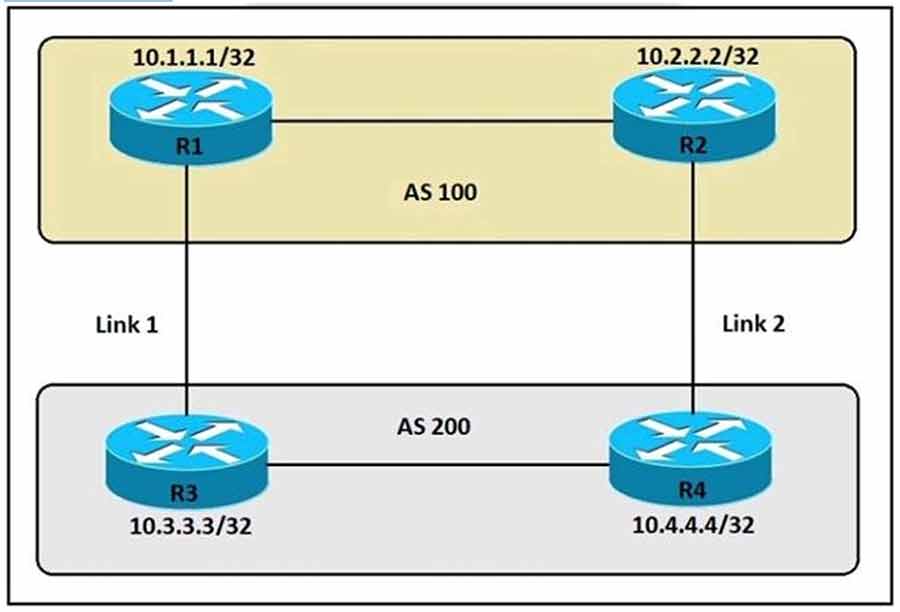
An engineer must ensure that all traffic leaving AS 200 will choose Link 2 as the exit point. Assuming that all BGP neighbor relationships have been formed and that the attributes have not been changed on any of the routers, which configuration accomplishes this task?
• A. R4(config-router)bgp default local-preference 200
• B. R3(config-router)bgp default local-preference 200
• C. R4(config-router)neighbor 10.2.2.2 weight 200
• D. R3(config-router)neighbor 10.1.1.1 weight 200
Which feature of EIGRP is not supported in OSPF?
• A. load balancing of unequal-cost paths
• B. load balance over four equal-cost paths
• C. uses interface bandwidth to determine best path
• D. per-packet load balancing over multiple paths
Which NTP Stratum level is a server that is connected directly to an authoritative time source?
• A. Stratum 0
• B. Stratum 1
• C. Stratum 14
• D. Stratum 15
An engineer reconfigures the port-channel between SW1 and SW2 from an access port to a trunk and immediately notices this error in SW1’s log:
*Mar 1 09:47:22.245: %PM-4-ERR_DISABLE: bpduguard error detected on Gi0/0, putting Gi0/0 in err disable state
Which command set resolves this error?
• A. SW1(config-if)#interface Gi0/0 SW1(config-if)#no spanning-tree bpdufilter SW1(config if)#shut SW1(config-if)#no shut
• B. SW1(config-if)#interface Gi0/0 SW1(config-if)#no spanning-tree bpduguard enable SW1(config-if)#shut SW1(config-if)#no shut
• C. SW1(config-if)#interface Gi0/0 SW1(config-if)#spanning-tree bpduguard enable SW1(config-if)#shut SW1(config-if)#no shut
• D. SW1(config-if)#interface Gi0/1 SW1(config-if)#spanning-tree bpduguard enable SW1(config-if)#shut SW1(config-if)#no shut
When a wireless client roams between two different wireless controllers, a network connectivity outage is experienced for a period of time.
Which configuration issue would cause this problem?
• A. Not all of the controllers in the mobility group are using the same mobility group name.
• B. Not all of the controllers within the mobility group are using the same virtual interface IP address.
• C. All of the controllers within the mobility group are using the same virtual interface IP address.
• D. All of the controllers in the mobility group are using the same mobility group name.
What is the role of the RP in PIM sparse mode?
• A. The RP maintains default aging timeouts for all multicast streams requested by the receivers.
• B. The RP acts as a control-plane node only and does not receive or forward multicast packets.
• C. The RP is the multicast router that is the root of the PIM-SM shared multicast distribution tree.
• D. The RP responds to the PIM join messages with the source of a requested multicast group.
Why is an AP joining a different WLC than the one specified through option 43?
• A. The AP is joining a primed WLC
• B. The APs broadcast traffic is unable to reach the WLC through Layer 2
• C. The AP multicast traffic is unable to reach the WLC through Layer 3
• D. The WLC is running a different software version
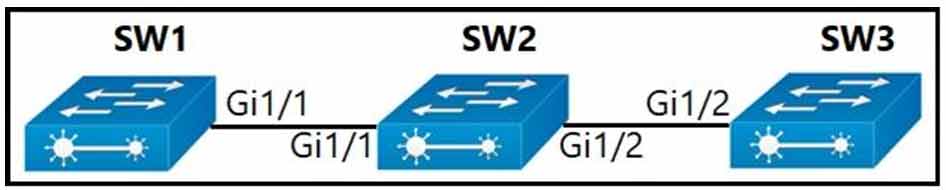
Company policy restricts VLAN 10 to be allowed only on SW1 and SW2. All other VLANs can be on all three switches. An administrator has noticed that VLAN 10 has propagated to SW3.
Which configuration corrects the issue?
• A. SW1(config)#int gi1/1 SW1(config)#switchport trunk allowed vlan 1-9,11-4094
• B. SW2(config)#int gi1/2 SW2(config)#switchport trunk allowed vlan 10
• C. SW2(config)#int gi1/2 SW2(config)#switchport trunk allowed vlan 1-9,11-4094
• D. SW1(config)#int gi1/1 SW1(config)#switchport trunk allowed vlan 10
Which First Hop Redundancy Protocol should be used to meet a design requirement for more efficient default gateway bandwidth usage across multiple devices?
• A. GLBP
• B. LACP
• C. HSRP
• D. VRRP
A client device roams between access points located on different floors in an atrium. The access points are joined to the same controller and configured in local mode. The access points are in different AP groups and have different IP addresses, but the client VLAN in the groups is the same.
Which type of roam occurs?
• A. inter-controller
• B. inter-subnet
• C. intra-VLAN
• D. intra-controller
Which DHCP option helps lightweight APs find the IP address of a wireless LAN controller?
• A. Option 43
• B. Option 60
• C. Option 67
• D. Option 150
Refer to the exhibit.
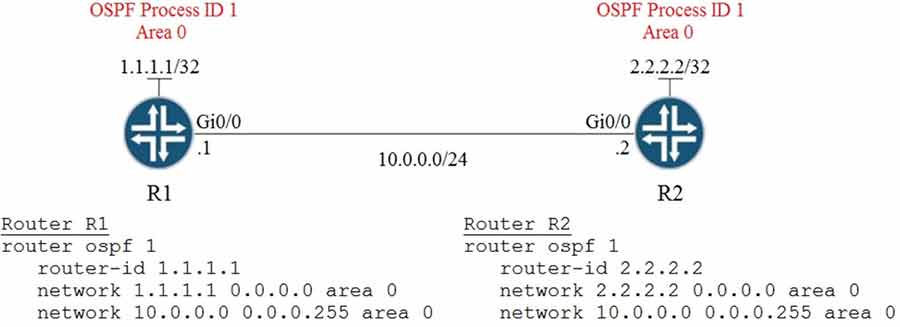
A network engineer is configuring OSPF between router R1 and router R2. The engineer must ensure that a DR/BDR election does not occur on the Gigabit Ethernet interfaces in area 0.
Which configuration set accomplishes this goal?
• A. R1(config-if)interface Gi0/0 R1(config-if)ip ospf network point-to-point R2(config if)interface Gi0/0 R2(config-if)ip ospf network point-to-point
• B. R1(config-if)interface Gi0/0 R1(config-if)ip ospf network broadcast R2(config-if)interface Gi0/0 R2(config-if)ip ospf network broadcast
• C. R1(config-if)interface Gi0/0 R1(config-if)ip ospf database-filter all out R2(config-if)interface Gi0/0 R2(config-if)ip ospf database-filter all out
• D. R1(config-if)interface Gi0/0 R1(config-if)ip ospf priority 1 R2(config-if)interface Gi0/0 R2(config-if)ip ospf priority 1
Refer to the exhibit.
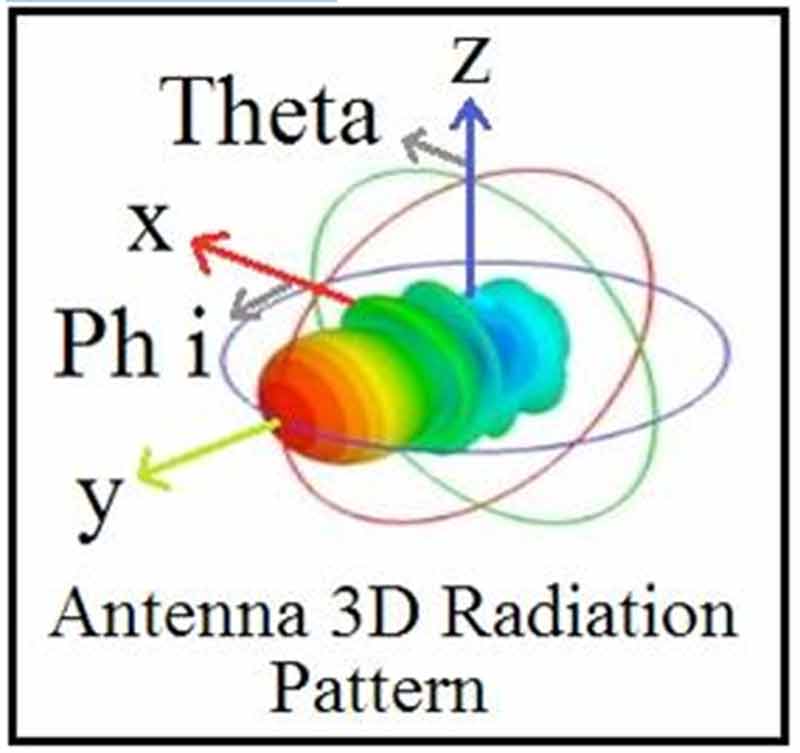
Which type of antenna does the radiation pattern represent?
• A. multidirectional
• B. directional patch
• C. omnidirectional
• D. Yagi
Wireless users report frequent disconnections from the wireless network. While troubleshooting, a network engineer finds that after the user is disconnected, the connection re-establishes automatically without any input required. The engineer also notices these message logs:
AP ‘AP2’ is down. Reason: Radio channel set. 6:54:04 PM
AP ‘AP4’ is down. Reason: Radio channel set. 6:44:49 PM
AP ‘AP7’ is down. Reason: Radio channel set. 6:34:32 PM
Which action reduces the user impact?
• A. enable coverage hole detection
• B. increase the AP heartbeat timeout
• C. enable BandSelect
• D. increase the dynamic channel assignment interval
Refer to the exhibit.
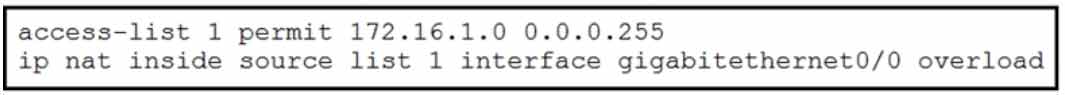
The inside and outside interfaces in the NAT configuration of this device have been correctly identified.
What is the effect of this configuration?
• A. NAT64
• B. dynamic NAT
• C. static NAT
• D. PAT
DRAG DROP –
Drag and drop the descriptions from the left onto the routing protocol they describe on the right.
Select and Place:
What is the purpose of an RP in PIM?
• A. send join messages toward a multicast source SPT
• B. ensure the shortest path from the multicast source to the receiver
• C. receive IGMP joins from multicast receivers
• D. secure the communication channel between the multicast sender and receiver
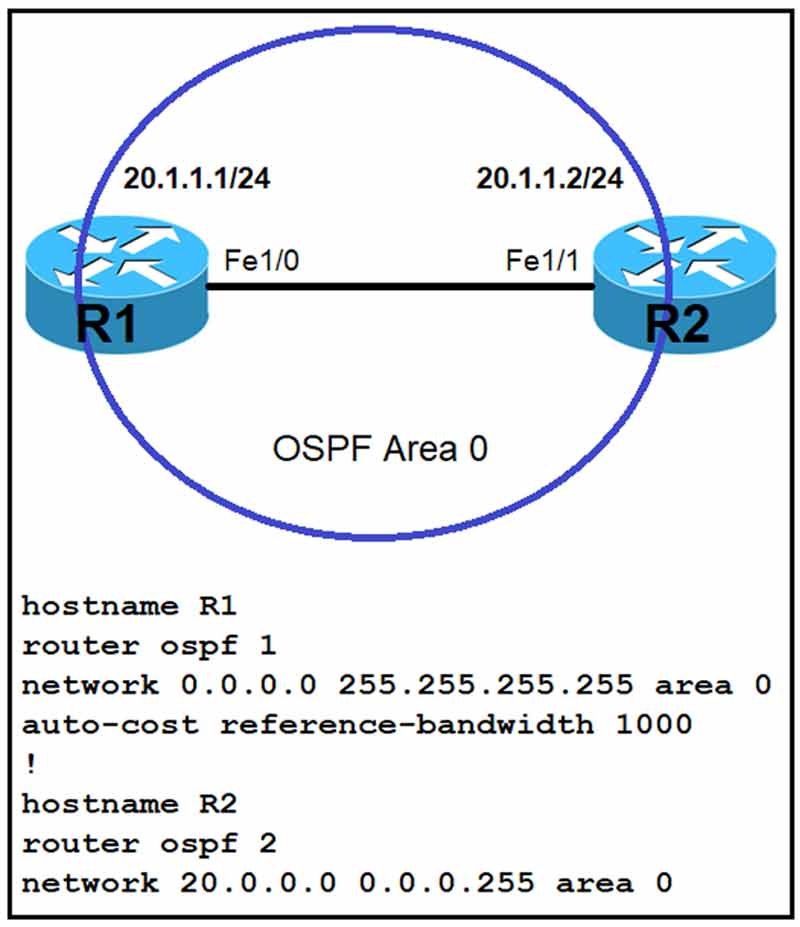
Refer to the exhibit. Which command must be applied to R2 for an OSPF neighborship to form?
• A. network 20.1.1.2 255.255.0.0 area 0
• B. network 20.1.1.2 0.0.0.0 area 0
• C. network 20.1.1.2 255.255.255.255 area 0
• D. network 20.1.1.2 0.0.255.255 area 0
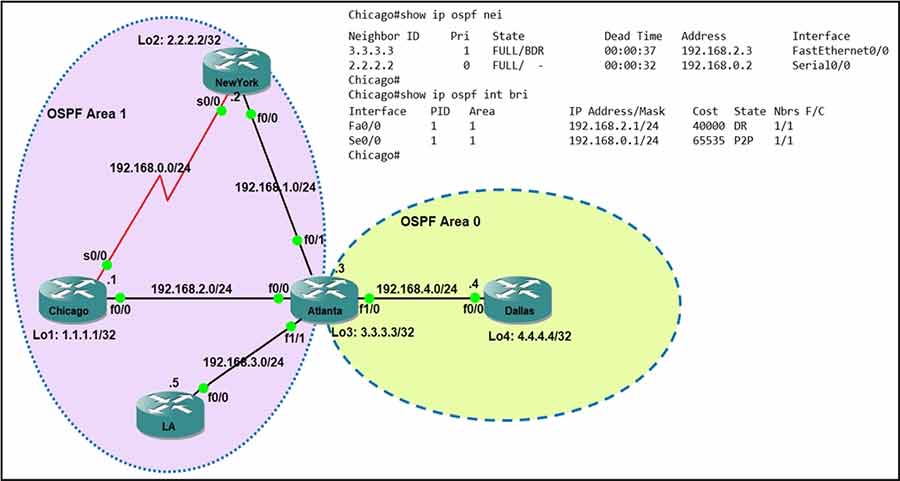
Refer to the exhibit. Which router is the designated router on the segment 192.168.0.0/24?
• A. This segment has no designated router because it is a p2p network type.
• B. Router Chicago because it has a lower router ID.
• C. Router NewYork because it has a higher router ID.
• D. This segment has no designated router because it is a nonbroadcast network type.
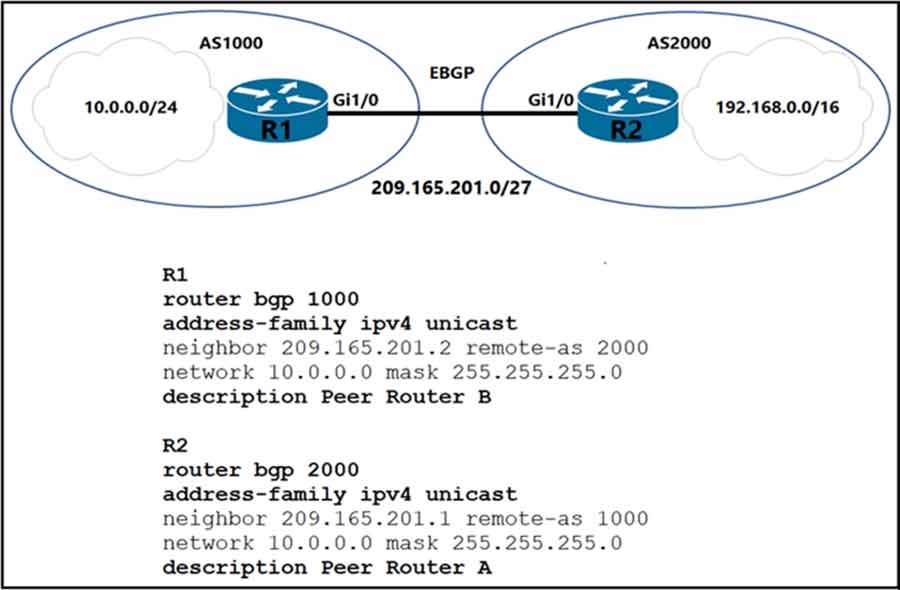
Refer to the exhibit. Which two commands are needed to allow for full reachability between AS 1000 and AS 2000? (Choose two.)
• A. R2#no network 10.0.0.0 255.255.255.0
• B. R2#network 209.165.201.0 mask 255.255.192.0
• C. R2#network 192.168.0.0 mask 255.255.0.0
• D. R1#no network 10.0.0.0 255.255.255.0
• E. R1#network 192.168.0.0 mask 255.255.0.0
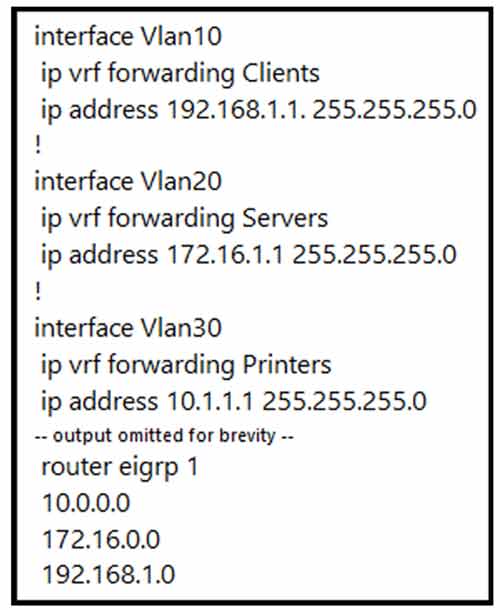
Refer to the exhibit. An engineer attempts to configure a router on a stick to route packets between Clients, Servers, and Printers; however, initial tests show that this configuration is not working. Which command set resolves this issue?
• A. interface Vlan10 no ip vrf forwarding Clients ! interface Vlan20 no ip vrf forwarding Servers ! interface Vlan30 no ip vrf forwarding Printers
• B. router eigrp 1 network 10.0.0.0 255.255.255.0 network 172.16.0.0 255.255.255.0 network 192.168.1.0 255.255.255.0
• C. interface Vlan10 no ip vrf forwarding Clients ip address 192.168.1.1. 255.255.255.0 ! interface Vlan20 no ip vrf forwarding Servers ip address 172.16.1.1 255.255.255.0 ! interface Vlan30 no ip vrf forwarding Printers ip address 10.1.1.1 255.255.255.0
• D. router eigrp 1 network 10.0.0.0 255.0.0.0 network 172.16.0.0 255.255.0.0 network 192.168.1.0 255.255.0.0
How does SSO work with HSRP to minimize network disruptions?
• A. It enables HSRP to elect another switch in the group as the active HSRP switch.
• B. It ensures fast failover in the case of link failure.
• C. It enables data forwarding along known routes following a switchover, while the routing protocol reconverges.
• D. It enables HSRP to failover to the standby RP on the same device.
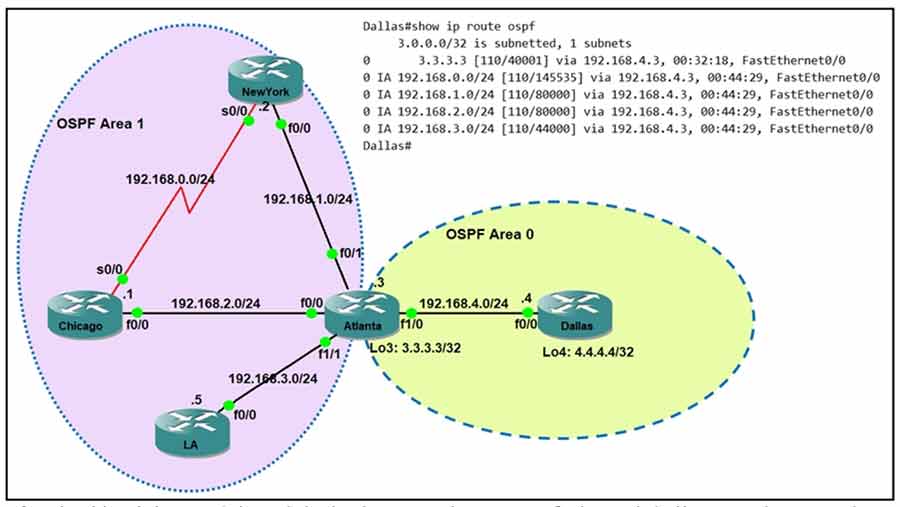
Refer to the exhibit. Which command when applied to the Atlanta router reduces type 3 LSA flooding into the backbone area and summarizes the inter-area routes on the Dallas router?
• A. Atlanta(config-router)#area 0 range 192.168.0.0 255.255.252.0
• B. Atlanta(config-router)#area 1 range 192.168.0.0 255.255.248.0
• C. Atlanta(config-router)#area 0 range 192.168.0.0 255.255.248.0
• D. Atlanta(config-router)#area 1 range 192.168.0.0 255.255.252.0
An engineer must configure interface GigabitEthernet0/0 for VRRP group 10. When the router has the highest priority in the group, it must assume the master role.
Which command set must be added to the initial configuration to accomplish this task?
Initial Configuration –
interface GigabitEthernet0/0
description To IDF A 38-24-044.40
ip address 172.16.13.2 255.255.255.0
• A. standby 10 ip 172.16.13.254 255.255.255.0 standby 10 preempt
• B. vrrp group 10 ip 172.16.13.254 255.255.255.0 vrrp group 10 priority
• C. standby 10 ip 172.16.13.254 standy 10 priority 120
• D. vrrp 10 ip 172.16.13.254 vrrp 10 preempt
DRAG DROP –
Drag and drop the characteristics from the left onto the routing protocols they describe on the right.
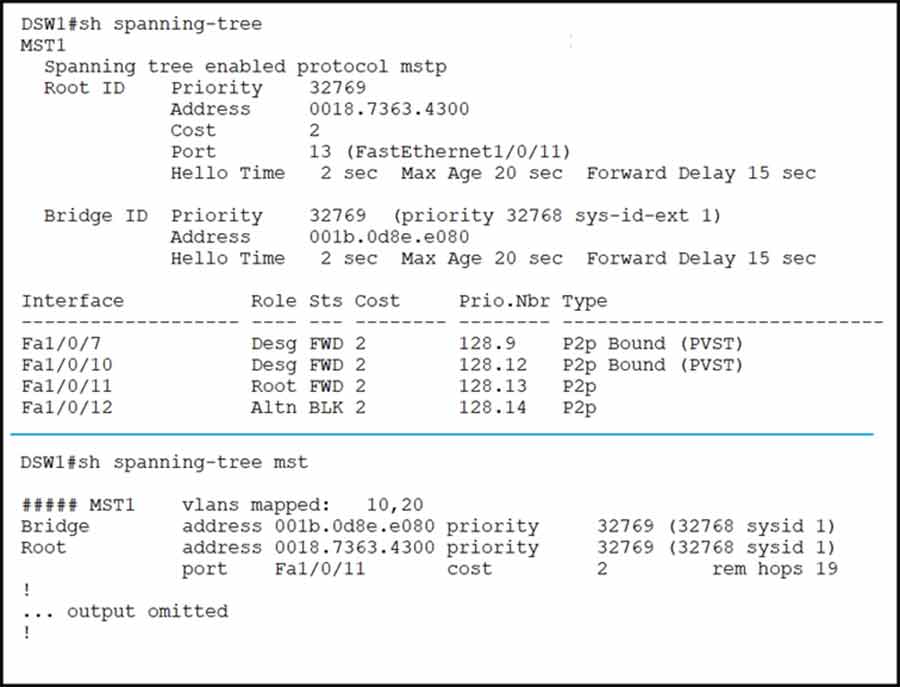
Refer to the exhibit. Which two commands ensure that DSW1 becomes the root bridge for VLAN 10 and 20? (Choose two.)
• A. spanning-tree mst 1 priority 4096
• B. spanning-tree mst 1 root primary
• C. spanning-tree mst vlan 10,20 priority root
• D. spanning-tree mst 1 priority 1
• E. spanning-tree mstp vlan 10,20 root primary
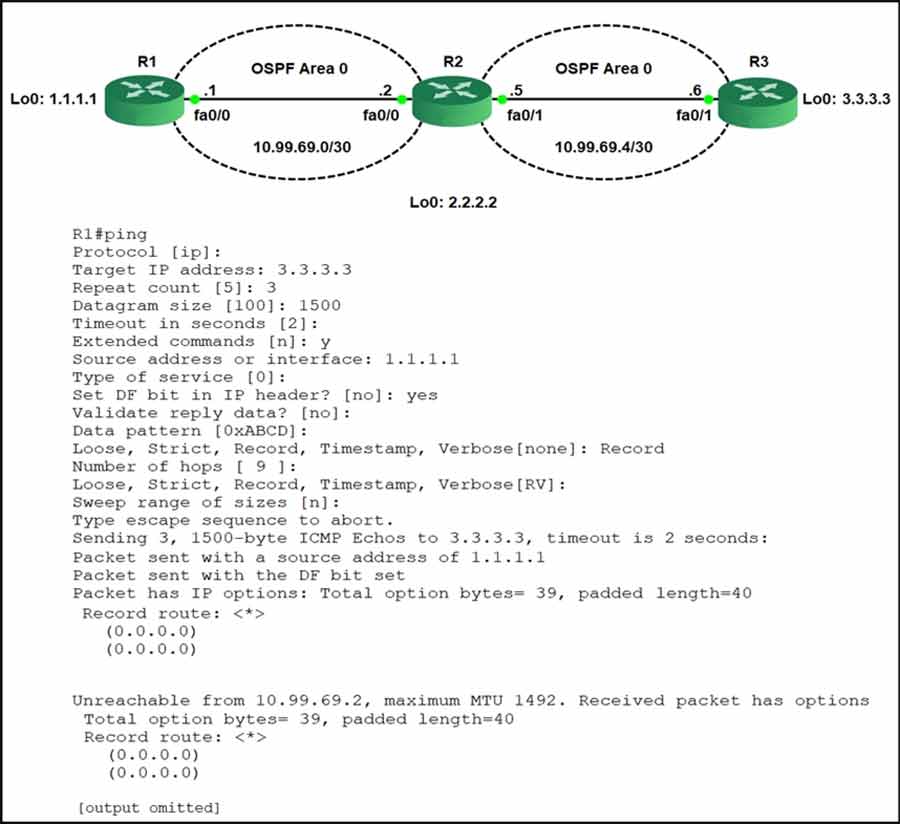
Refer to the exhibit. R1 is able to ping the R3 fa0/1 interface. Why do the extended pings fail?
• A. The maximum packet size accepted by the command is 1476 bytes.
• B. The DF bit has been set.
• C. R3 is missing a return route to 10.99.69.0/30.
• D. R2 and R3 do not have an OSPF adjacency.
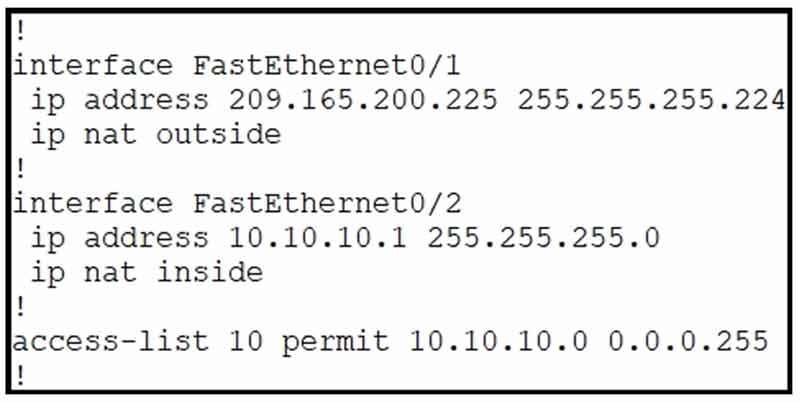
Refer to the exhibit. Which command allows hosts that are connected to FastEthernet0/2 to access the Internet?
• A. ip nat inside source list 10 interface FastEthernet0/2 overload
• B. ip nat inside source list 10 interface FastEthernet0/1 overload
• C. ip nat outside source static 209.165.200.225 10.10.10.0 overload
• D. ip nat outside source list 10 interface FastEthernet0/2 overload
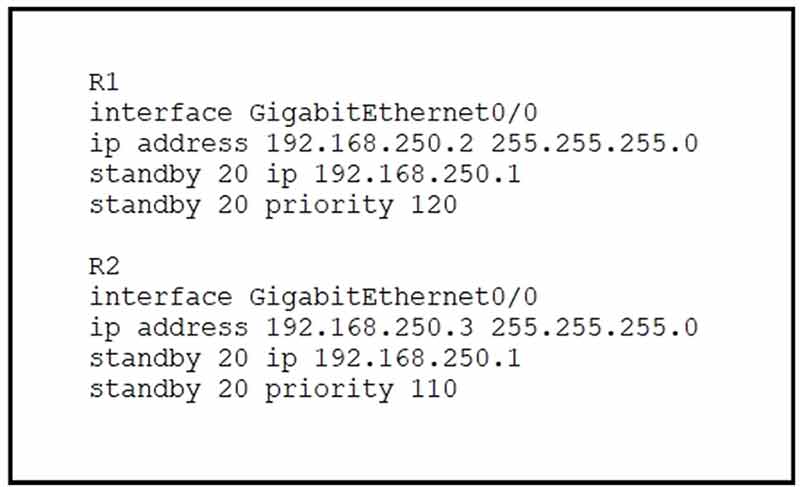
Refer to the exhibit. What are two effects of this configuration? (Choose two.)
• A. If R1 goes down, R2 becomes active but reverts to standby when R1 comes back online.
• B. If R2 goes down, R1 becomes active but reverts to standby when R2 comes back online.
• C. R1 becomes the active router.
• D. R1 becomes the standby router.
• E. If R1 goes down, R2 becomes active and remains the active device when R1 comes back online.
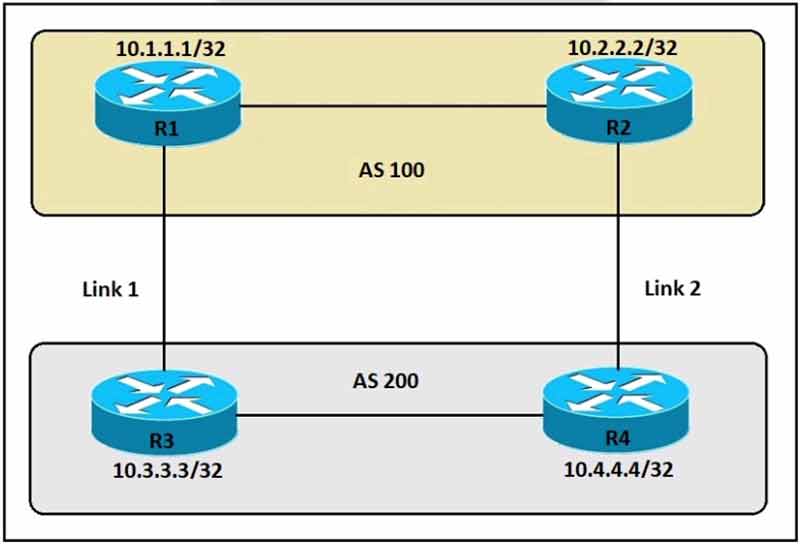
Refer to the exhibit. An engineer must ensure that all traffic entering AS 200 from AS 100 chooses Link 2 as an entry point. Assume that all BGP neighbor relationships have been formed and that the attributes have not been changed on any of the routers. Which configuration accomplishes this task?
• A. R3(config)#route-map PREPEND permit 10 R3(config-route-map)#set as-path prepend 200 200 200 R3(config)#router bgp 200 R3#(config-router)#neighbor 10.1.1.1 route-map PREPEND out
• B. R4(config)#route-map PREPEND permit 10 R4(config-route-map)#set as-path prepend 100 100 100 R4(config)#router bgp 200 R4(config-router)#neighbor 10.2.2.2 route-map PREPEND in
• C. R4(config)#route-map PREPEND permit 10 R4(config-route-map)#set as-path prepend 200 200 200 R4(config)#router bgp 200 R4(config-router)#neighbor 10.2.2.2 route-map PREPEND out
• D. R3(config)#route-map PREPEND permit 10 R3(config-route-map)#set as-path prepend 100 100 100 R3(config)#router bgp 200 R3(config-router)#neighbor 10.1.1.1 route-map PREPEND in
Which DHCP option provides the CAPWAP APs with the address of the wireless controller(s)?
• A. 43
• B. 66
• C. 69
• D. 150
Which two commands ensure that DSW1 becomes root bridge for VLAN 10? (Choose two.)
• A. DSW1(config)#spanning-tree vlan 10 priority 4096
• B. DSW1(config)#spanning-tree vlan 10 priority root
• C. DSW2(config)#spanning-tree vlan 10 priority 61440
• D. DSW1(config)#spanning-tree vlan 10 port-priority 0
• E. DSW2(config)#spanning-tree vlan 20 priority 0
What mechanism does PIM use to forward multicast traffic?
• A. PIM sparse mode uses a pull model to deliver multicast traffic.
• B. PIM dense mode uses a pull model to deliver multicast traffic.
• C. PIM sparse mode uses receivers to register with the RP.
• D. PIM sparse mode uses a flood and prune model to deliver multicast traffic.
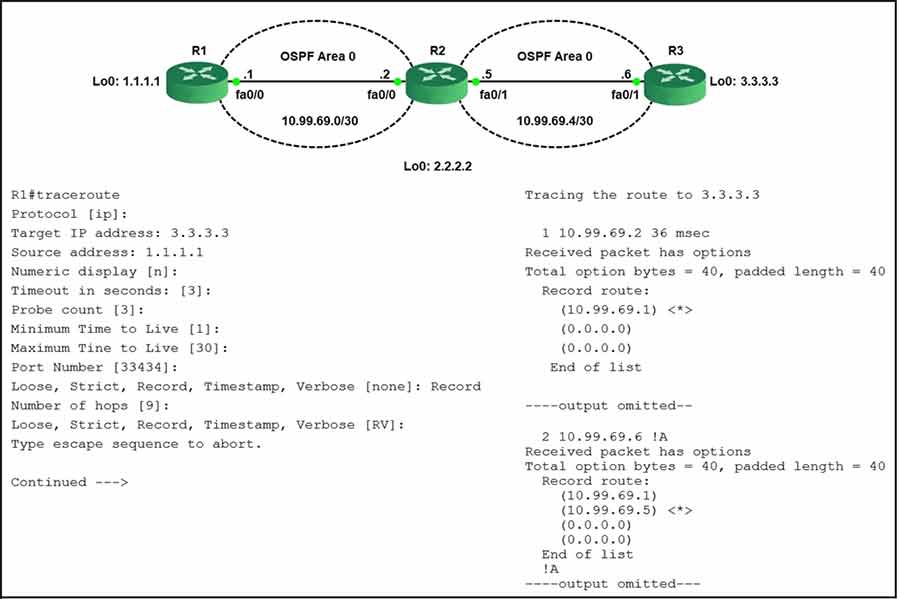
The traceroute fails from R1 to R3.
What is the cause of the failure?
• A. An ACL applied inbound on loopback0 of R2 is dropping the traffic.
• B. The loopback on R3 is in a shutdown state.
• C. Redistribution of connected routes into OSPF is not configured.
• D. An ACL applied inbound on fa0/1 of R3 is dropping the traffic.
Refer to the exhibit.
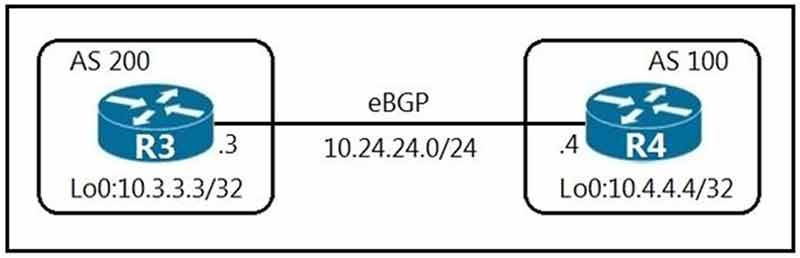
An engineer must establish eBGP peering between router R3 and router R4. Both routers should use their loopback interfaces as the BGP router ID.
Which configuration set accomplishes this task?
• A. R3(config)#router bgp 200 R3(config-router)#neighbor 10.4.4.4 remote-as 100 R3(config router)# neighbor 10.4.4.4 update-source Loopback0 R4(config)#router bgp 100 R4(config router)#neighbor 10.3.3.3 remote-as 200 R4(config-router)#network 10.3.3.3 update-source Loopback0
• B. R3(config)#router bgp 200 R3(config-router)#neighbor 10.24.24.4 remote-as 100 R3(config-router)#neighbor 10.24.24.4 update-source Loopback0 R4(config)#router bgp 100 R4(config-router)#neighbor 10.24.24.3 remote-as 200 R4(config-router)#neighbor 10.24.24.3 update-source Loopback0
• C. R3(config)#router bgp 200 R3(config-router)#neighbor 10.4.4.4 remote-as 100 R3(config router)#bgp router-id 10.3.3.3 R4(config)#router bgp 100 R4(config-router)#neighbor 10.3.3.3 remote-as 200 R4(config-router)#bgp router-id 10.4.4.4
• D. R3(config)#router bgp 200 R3(config-router)#neighbor 10.24.24.4 remote-as 100 R3(config-router)#bgp router-id 10.3.3.3 R4(config)#router bgp 100 R4(config router)#neighbor 10.24.24.3 remote-as 200 R4(config-router)#bgp router-id 10.4.4.4
An engineer is configuring GigabitEthernet1/0/0 for VRRP. When the router has the highest priority in group 5, it must assume the master role.
Which command set should the engineer add to the configuration to accomplish this task?
interface GigabitEthernet1/0/0 description To IDF A 38-70-774-10 ip address 172.16.13.2 255.255.255.0
• A. standby 5 ip 172.16.13.254 standby 5 priority 100 standby 5 track 1 decrement 10
• B. standby 5 ip 172.16.13.254 standby 5 priority 100 standby 5 preempt
• C. vrrp 5 ip 172.16.13.254 vrrp 5 priority 100
• D. vrrp 5 ip 172.16.13.254 255.255.255.0 vrrp 5 track 1 decrement 10 vrrp 5 preempt
Which two security features are available when implementing NTP? (Choose two.)
• A. encrypted authentication mechanism
• B. symmetric server passwords
• C. clock offset authentication
• D. broadcast association mode
• E. access list-based restriction scheme
How does the EIGRP metric differ from the OSPF metric?
• A. The EIGRP metric is calculated based on bandwidth only. The OSPF metric is calculated on delay only.
• B. The EIGRP metric is calculated based on delay only. The OSPF metric is calculated on bandwidth and delay.
• C. The EIGRP metric is calculated based on bandwidth and delay. The OSPF metric is calculated on bandwidth only.
• D. The EIGRP metric is calculated based on hop count and bandwidth. The OSPF metric is calculated on bandwidth and delay.
Refer to the exhibit.
An engineer is installing a new pair of routers in a redundant configuration.
Which protocol ensures that traffic is not disrupted in the event of a hardware failure?
• A. HSRPv1
• B. GLBP
• C. VRRP
• D. HSRPv2
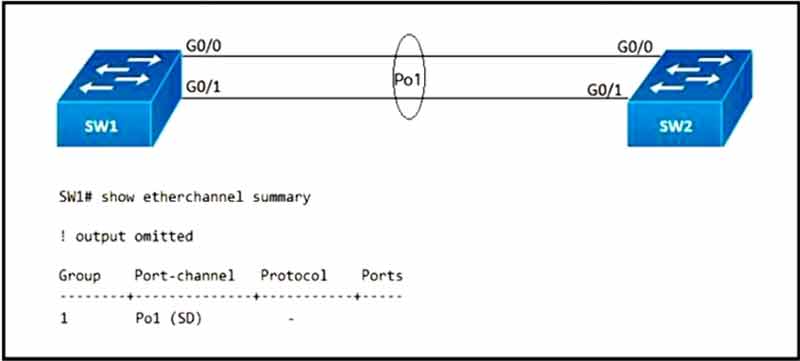
Refer to the exhibit. After an engineer configures an EtherChannel between switch SW1 and switch SW2, this error message is logged on switch SW2:
SW2#
09:45:32: %PM-4-ERR_DISABLE: channel-misconfig error detected on Gi0/0, putting Gi0/0 in err disable state
09:45:32: %PM-4-ERR_DISABLE: channel-misconfig error detected on Gi0/1, putting Gi0/1 in err disable state
Based on the output from switch SW1 and the log message received on switch SW2, what action should the engineer take to resolve this issue?
• A. Configure the same protocol on the EtherChannel on switch SW1 and SW2.
• B. Define the correct port members on the EtherChannel on switch SW1.
• C. Correct the configuration error on Interface Gi0/0 on switch SW1.
• D. Correct the configuration error on Interface Gi0/1 on switch SW1.
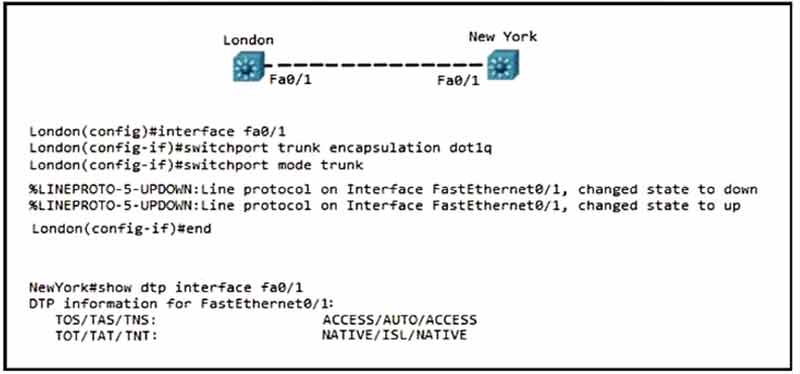
Refer to the exhibit. Communication between London and New York is down. Which command set must be applied to resolve this issue?
• A. NewYork(config)#int f0/1
NewYork(config)#switchport nonegotiate
NewYork(config)#end
NewYork#
• B. NewYork(config)#int f0/1
NewYork(config)#switchport mode trunk
NewYork(config)#end
NewYork#
• C. NewYork(config)#int f0/1
NewYork(config)#switchport trunk encap dot1q
NewYork(config)#end
NewYork#
• D. NewYork(config)#int f0/1
NewYork(config)#switchport mode dynamic desirable
NewYork(config)#end
NewYork#
Which encryption hashing algorithm does NTP use for authentication?
• A. SSL
• B. MD5
• C. AES128
• D. AES256
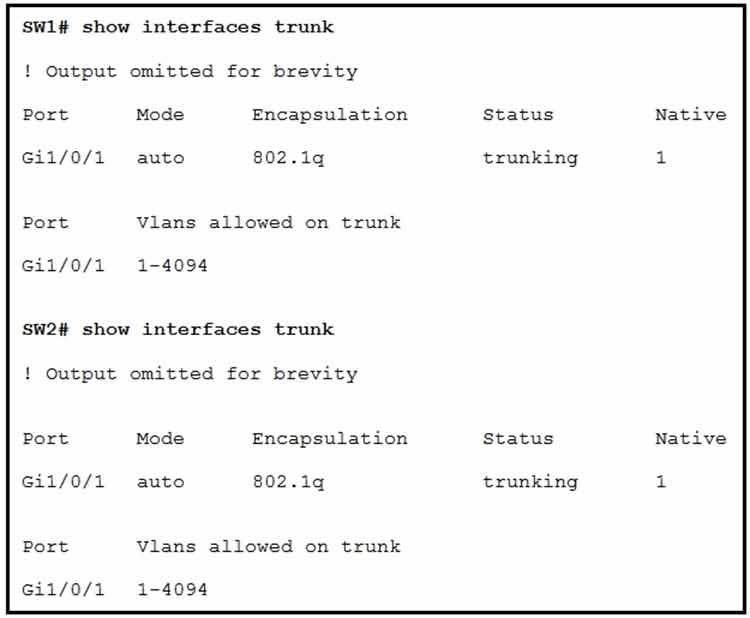
Refer to the exhibit. The trunk between Gig1/0/1 of switch SW2 and Gig1/0/1 of switch SW1 is not operational. Which action resolves this issue?
• A. Configure both interfaces to nonegotiate and ensure that the switches are in different VTP domains.
• B. Configure both interfaces in dynamic auto DTP mode and ensure that the switches are in the same VTP domain.
• C. Configure both interfaces in dynamic auto DTP mode and ensure that the switches are in different VTP domains.
• D. Configure both interfaces in dynamic desirable DTP mode and ensure that the switches are in the same VTP domain.
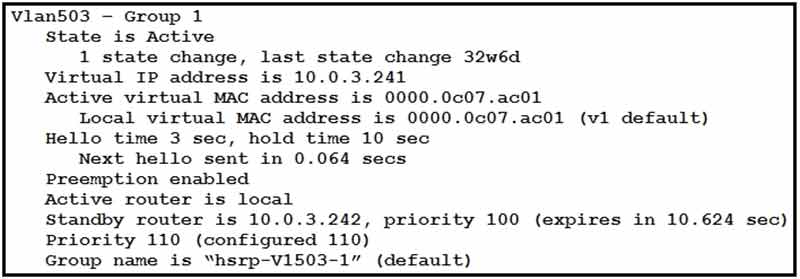
Refer to the exhibit. Which two facts does the device output confirm? (Choose two.)
• A. The device’s HSRP group uses the virtual IP address 10.0.3.242.
• B. The device is configured with the default HSRP priority.
• C. The device sends unicast messages to its peers.
• D. The standby device is configured with the default HSRP priority.
• E. The device is using the default HSRP hello timer.
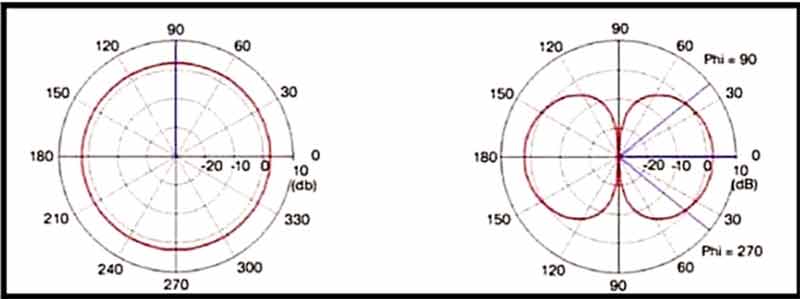
Refer to the exhibit. Which type of antenna is shown on the radiation patterns?
• A. patch
• B. dipole
• C. omnidirectional
• D. Yagi
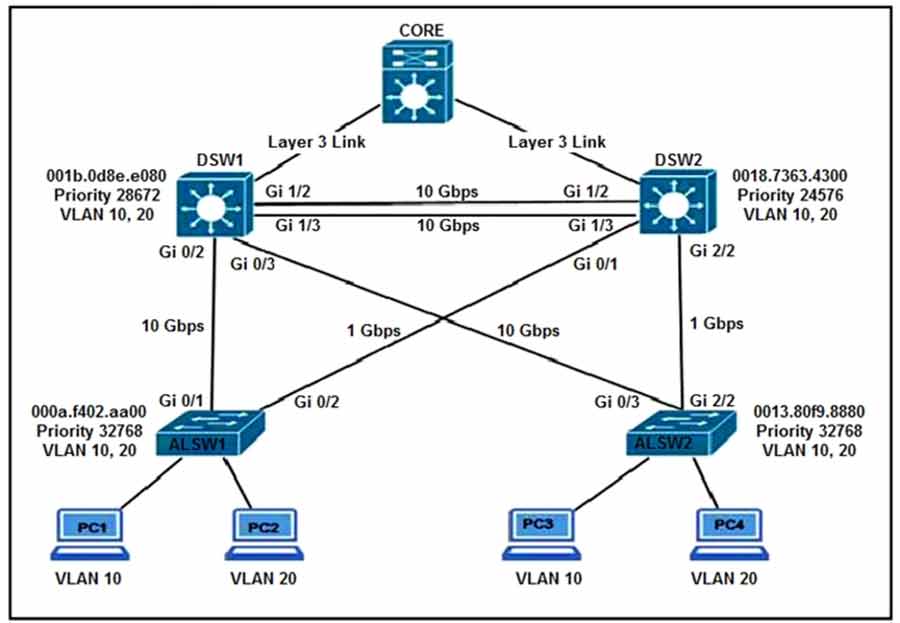
Refer to the exhibit. All switches are configured with the default port priority value. Which two commands ensure that traffic from PC1 is forwarded over the Gi1/3 trunk port between DSW1 and DSW2? (Choose two.)
• A. DSW2(config)#interface gi1/3
• B. DSW1(config-if)#spanning-tree port-priority 0
• C. DSW2(config-if)#spanning-tree port-priority 128
• D. DSW1(config)#interface gi1/3
• E. DSW2(config-if)#spanning-tree port-priority 16
A company has an existing Cisco 5520 HA cluster using SSO. An engineer deploys a new single Cisco Catalyst 9800 WLC to test new features. The engineer successfully configures a mobility tunnel between the 5520 cluster and 9800 WLC. Clients connected to the corporate WLAN roam seamlessly
between access points on the 5520 and 9800 WLC. After a failure on the primary 5520 WLC, all WLAN services remain functional; however, clients cannot roam between the 5520 and 9800 controllers without dropping their connection. Which feature must be configured to remedy the issue?
• A. mobility MAC on the 5520 cluster
• B. mobility MAC on the 9800 WLC
• C. new mobility on the 5520 cluster
• D. new mobility on the 9800 WLC
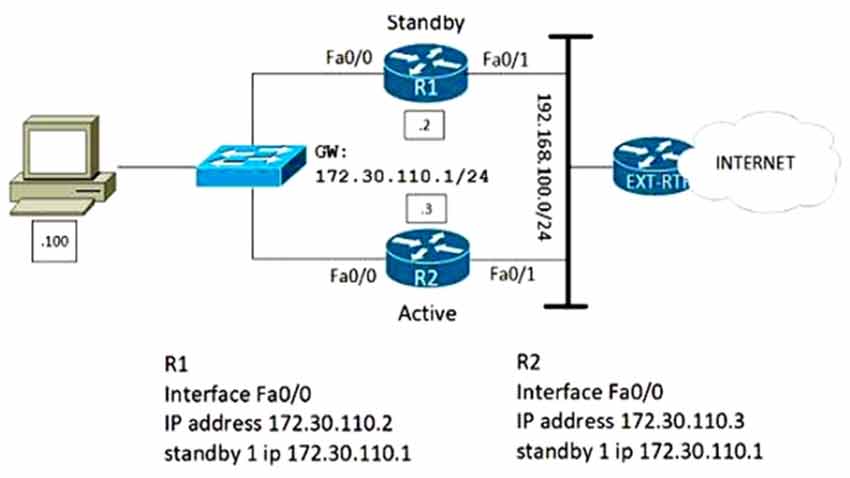
Refer to the exhibit. Which configuration change ensures that R1 is the active gateway whenever it is in a functional state for the 172.30.110.0/24 network?
• A. R2 standby 1 priority 90 standby 1 preempt
• B. R2 standby 1 priority 100 standby 1 preempt
• C. R1 standby 1 preempt R2 standby 1 priority 90
• D. R1 standby 1 preempt R2 standby 1 priority 100
A customer has completed the installation of a Wi-Fi 6 greenfield deployment at their new campus.
They want to leverage Wi-Fi 6 enhanced speeds on the trusted employee WLAN. To configure the employee WLAN, which two Layer 2 security policies should be used? (Choose two.)
• A. WPA2 (AES)
• B. 802.1X
• C. OPEN
• D. WEP
• E. WPA (AES)
Which two actions, when applied in the LAN network segment, will facilitate Layer 3 CAPWAP discovery for lightweight AP? (Choose two.)
• A. Utilize DHCP option 43.
• B. Utilize DHCP option 17.
• C. Configure an ip helper-address on the router interface.
• D. Enable port security on the switch port.
• E. Configure WLC IP address on LAN switch
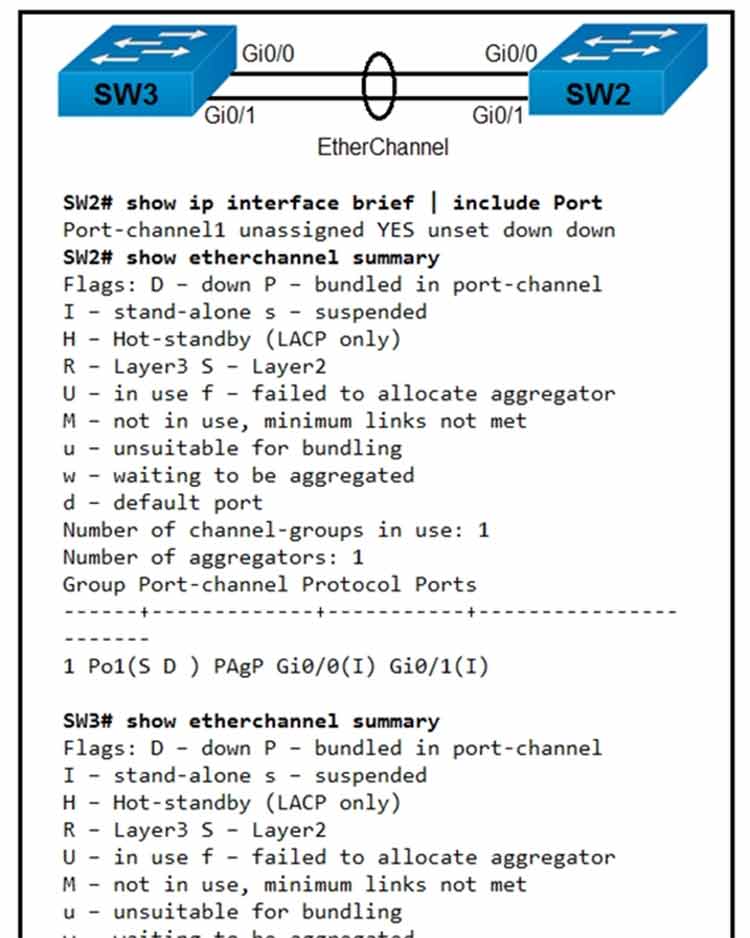
Refer to the exhibit. Which action resolves the EtherChannel issue between SW2 and SW3?
• A. Configure switchport mode trunk on SW2.
• B. Configure switchport nonegotiate on SW3.
• C. Configure channel-group 1 mode desirable on both interfaces.
• D. Configure channel-group 1 mode active on both interfaces.
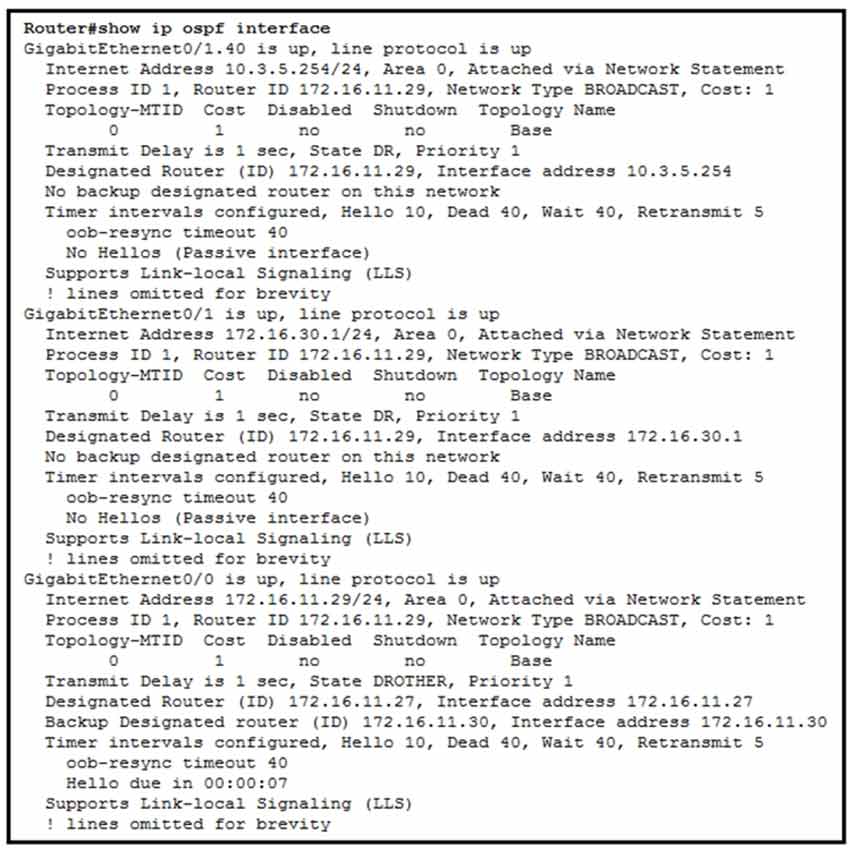
Refer to the exhibit. A network engineer configures OSPF and reviews the router configuration.
Which interface or interfaces are able to establish OSPF adjacency?
• A. GigabitEthernet0/0 and GigabitEthernet0/1
• B. only GigabitEthernet0/1
• C. only GigabitEthernet0/0
• D. GigabitEthernet0/1 and GigabitEthernet0/1.40
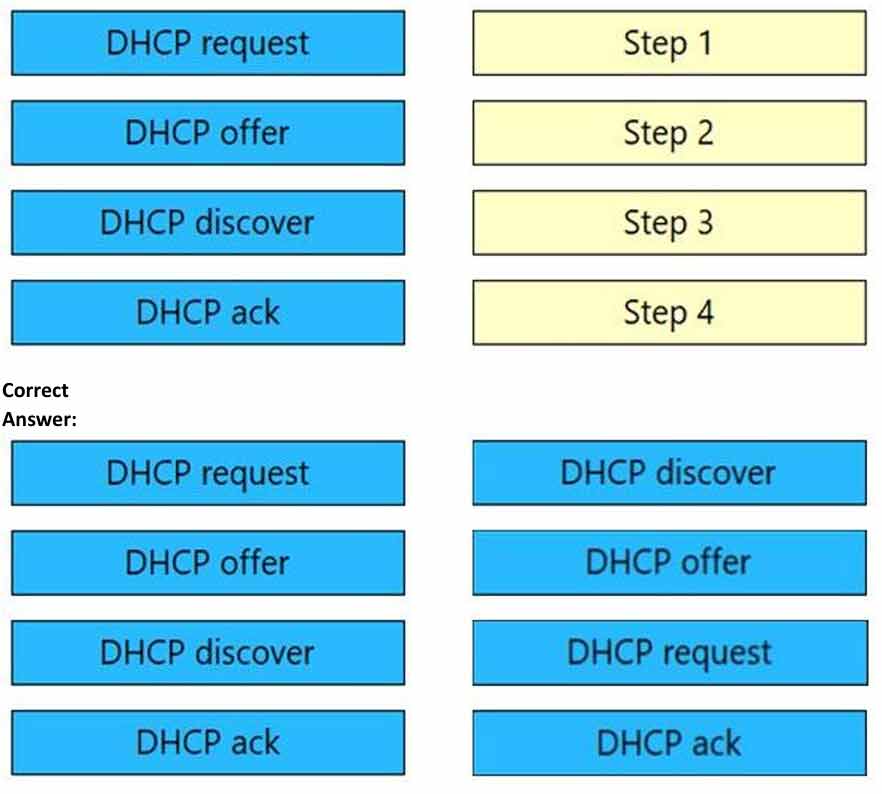
DRAG DROP –
Drag and drop the DHCP messages that are exchanged between a client and an AP into the order they are exchanged on the right.
Select and Place:
Which two methods are used by an AP that is trying to discover a wireless LAN controller? (Choose two.)
• A. Cisco Discovery Protocol neighbor
• B. querying other APs
• C. DHCP Option 43
• D. broadcasting on the local subnet
• E. DNS lookup CISCO-DNA-PRIMARY.localdomain
What is the responsibility of a secondary WLC?
• A. It enables Layer 2 and Layer 3 roaming between itself and the primary controller.
• B. It registers the LAPs if the primary controller fails.
• C. It avoids congestion on the primary controller by sharing the registration load on the LAPs.
• D. It shares the traffic load of the LAPs with the primary controller.
Refer to the exhibit.
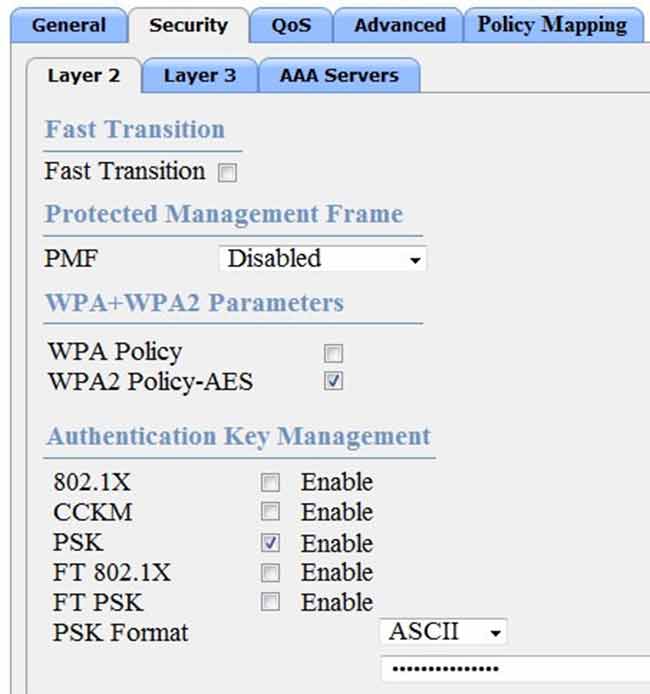
Based on the configuration in this WLAN security setting, which method can a client use to authenticate to the network?
• A. text string
• B. username and password
• C. RADIUS token
• D. certificate
A client device fails to see the enterprise SSID, but other client devices are connected to it.
What is the cause of this issue?
• A. The client has incorrect credentials stored for the configured broadcast SSID.
• B. The hidden SSID was not manually configured on the client.
• C. The broadcast SSID was not manually configured on the client.
• D. The client has incorrect credentials stored for the configured hidden SSID.
Which two descriptions of FlexConnect mode for Cisco APs are true? (Choose two.)
• A. APs that operate in FlexConnect mode cannot detect rogue APs.
• B. When connected to the controller, FlexConnect APs can tunnel traffic back to the controller.
• C. FlexConnect mode is used when the APs are set up in a mesh environment and used to bridge between each other.
• D. FlexConnect mode is a feature that is designed to allow specified CAPWAP-enabled APs to exclude themselves from managing data traffic between clients and infrastructure.
• E. FlexConnect mode is a wireless solution for branch office and remote office deployments.
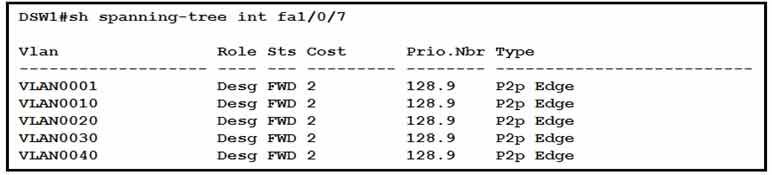
Refer to the exhibit. How was spanning-tree configured on this interface?
• A. By entering the command spanning-tree portfast trunk in the interface configuration mode.
• B. By entering the command spanning-tree mst1 vlan 10,20,30,40 in the global configuration mode.
• C. By entering the command spanning-tree portfast in the interface configuration mode.
• D. By entering the command spanning-tree vlan 10,20,30,40 root primary in the interface configuration mode.
Refer to the exhibit. Rapid PVST+ is enabled on all switches. Which command set must be configured on Switch1 to achieve the following results on port fa0/1?
✑ When a device is connected, the port transitions immediately to a forwarding state.
✑ The interface should not send or receive BPDUs.
✑ If a BPDU is received, it continues operating normally.
• A. Switch1(config)# spanning-tree portfast bpdufilter default
Switch1(config)# interface f0/1
Switch1(config-if)# spanning-tree portfast
• B. Switch1(config)# spanning-tree portfast bpduguard default
Switch 1 (config)# interfacef0/1
Switch1 (config-if)# spanning-tree portfast
• C. Switch1(config)# interface f0/1
Switch1(config-if)# spanning-tree portfast
• D. Switch1(config)# interface f0/1
Switch1(config-if)# spanning-tree portfast
Switch1 (config-if)# spanning-tree bpduguard enable
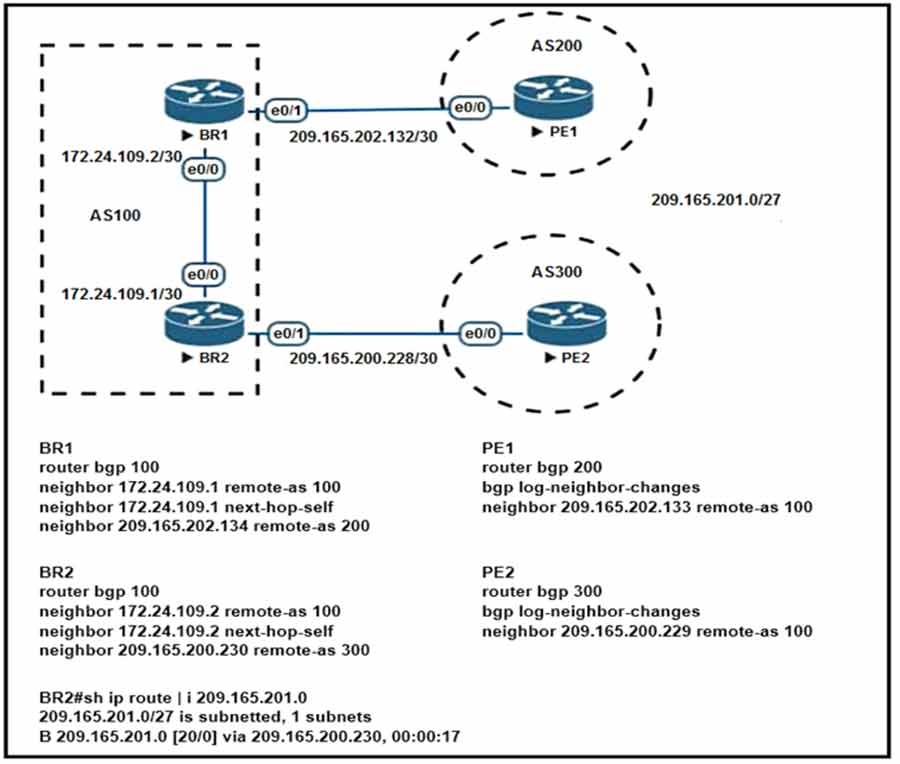
Refer to the exhibit. Which configuration change will force BR2 to reach 209.165.201.0/27 via BR1?
• A. Set the MED to 1 on PE2 toward BR2 outbound.
• B. Set the origin to igp on BR2 toward PE2 inbound.
• C. Set the weight attribute to 65,535 on BR1 toward PE1.
• D. Set the local preference to 150 on PE1 toward BR1 outbound.
DRAG DROP –
Drag and drop the characteristics from the left onto the protocols they apply to on the right.
Select and Place
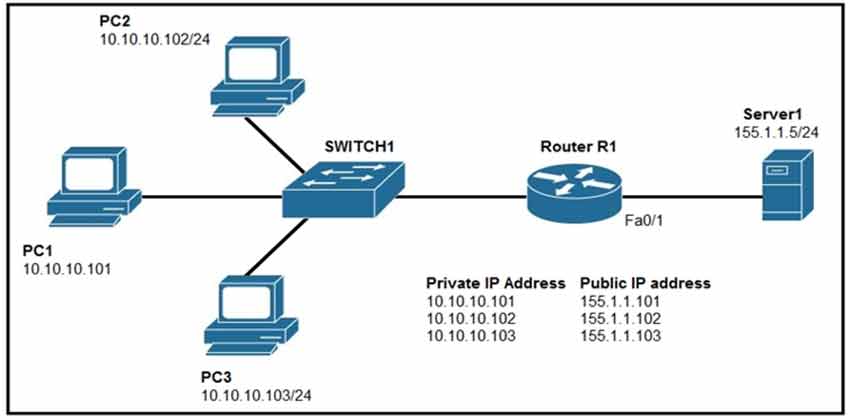
Refer to the exhibit. Which set of commands on router R1 allow deterministic translation of private hosts PC1, PC2, and PC3 to addresses in the public space?
• A. RouterR1(config)#int f0/0
RouterR1(config)#ip nat inside
RouterR1(config)#exit
RouterR1(config)#int f0/1
RouterR1(config)#ip nat outside
RouterR1(config)#exit
RouterR1(config)#access-list 1 10.10.10.0 0.0.0.255
RouterR1(config)#ip nat inside source list 1 interface f0/1 overload
• B. RouterR1(config)#int f0/0
RouterR1(config)#ip nat inside
RouterR1(config)#exit
RouterR1(config)#int f0/1
RouterR1(config)#ip nat outside
RouterR1(config)#exit
RouterR1(config)#access-list 1 10.10.10.0 0.0.0.255
RouterR1(config)#ip nat pool POOL 155.1.1.101 155.1.1.103 netmask 255.255.255.0
RouterR1(config)#ip nat inside source list 1 pool POOL
• C. RouterR1(config)#int f0/0
RouterR1(config)#ip nat inside
RouterR1(config)#exit
RouterR1(config)#int f0/1
RouterR1(config)#ip nat outside
RouterR1(config)#exit
RouterR1(config)#ip nat inside source static 10.10.10.101 155.1.1.101
RouterR1(config)#ip nat inside source static 10.10.10.102 155.1.1.102
RouterR1(config)#ip nat inside source static 10.10.10.103 155.1.1.103
• D. RouterR1(config)#int f0/0
RouterR1(config)#ip nat outside
RouterR1(config)#exit
RouterR1(config)#int f0/1
RouterR1(config)#ip nat inside
RouterR1(config)#exit
RouterR1(config)#ip nat inside source static 10.10.10.101 155.1.1.101
RouterR1(config)#ip nat inside source static 10.10.10.102 155.1.1.102
RouterR1(config)#ip nat inside source static 10.10.10.103 155.1.1.103
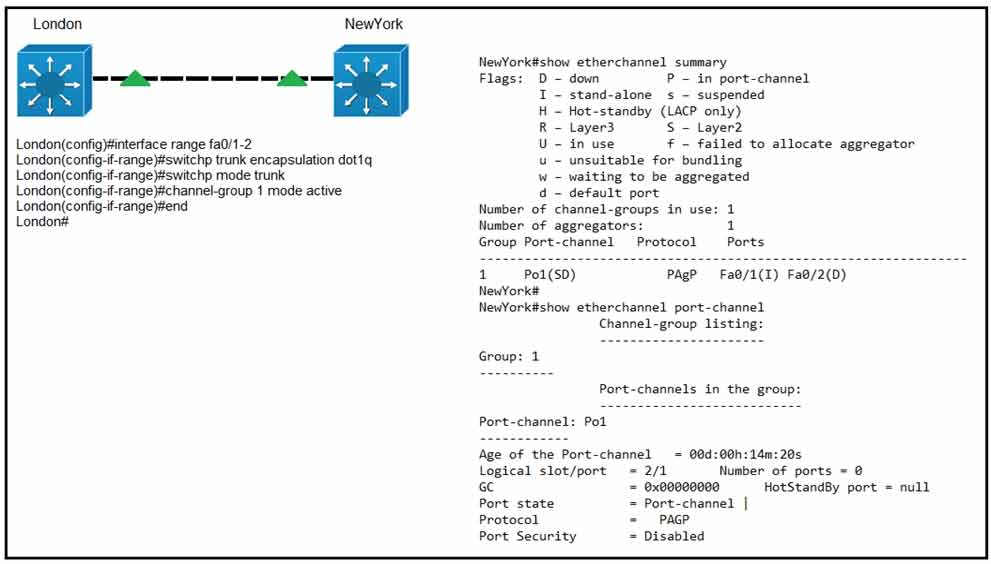
Refer to the exhibit. Communication between London and New York is down. Which command set must be applied to the NewYork switch to resolve the issue?
• A. NewYork(config)#no interface po1
NewYork(config)#interface range fa0/1-2
NewYork(config-if)#channel-group 1 mode negotiate
NewYork(config-if)#end
NewYork#
• B. NewYork(config)#no interface po1
NewYork(config)#interface range fa0/1-2
NewYork(config-if)#channel-group 1 mode on
NewYork(config-if)#end
NewYork#
• C. NewYork(config)#no interface po1
NewYork(config)#interface range fa0/1-2
NewYork(config-if)#channel-group 1 mode passive
NewYork(config-if)#end
NewYork#
• D. NewYork(config)#no interface po1
NewYork(config)#interface range fa0/1-2
NewYork(config-if)#channel-group 1 mode auto
NewYork(config-if)#end
NewYork#
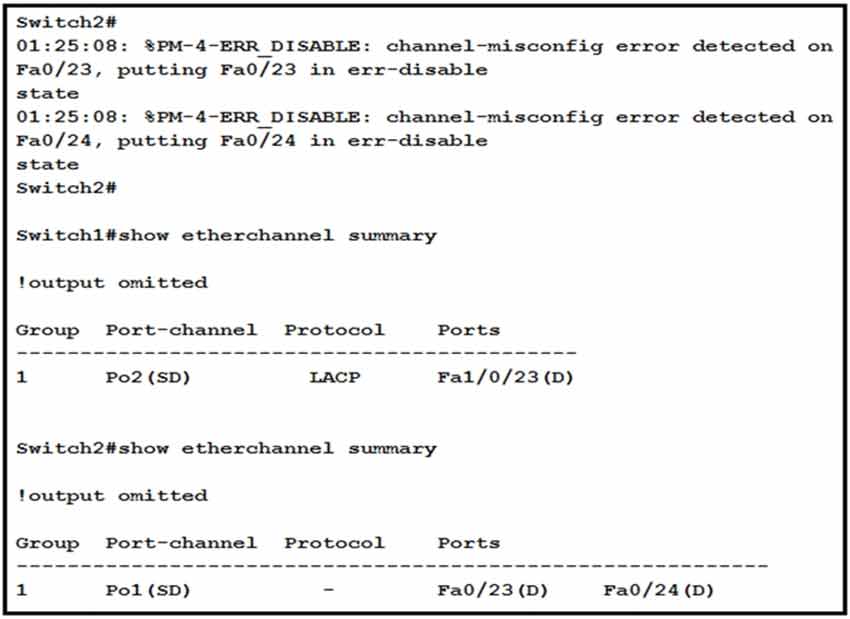
Refer to the exhibit. An engineer is configuring an EtherChannel between Switch1 and Switch2 and notices the console message on Switch2. Based on the output, which action resolves this issue?
• A. Configure more member ports on Switch1.
• B. Configure less member ports on Switch2.
• C. Configure the same port channel interface number on both switches.
• D. Configure the same EtherChannel protocol on both switches.
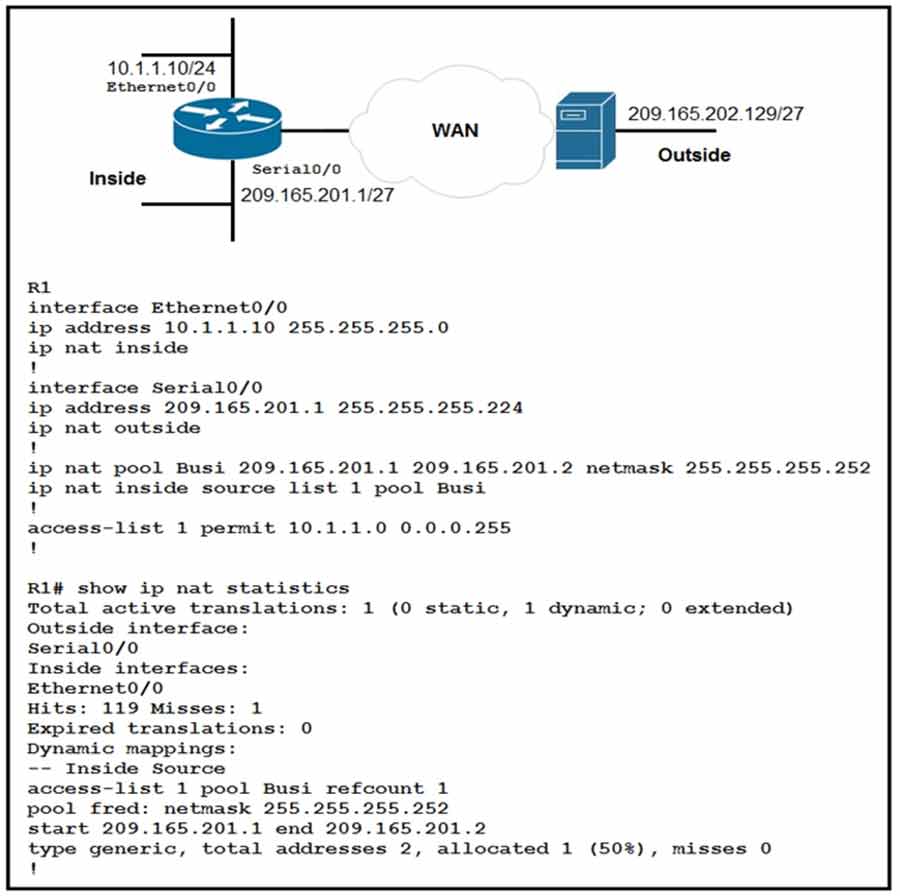
Refer to the exhibit. A network engineer configures NAT on R1 and enters the show command to verify the configuration. What does the output confirm?
• A. The first packet triggered NAT to add an entry to the NAT table.
• B. R1 is configured with NAT overload parameters.
• C. A Telnet session from 160.1.1.1 to 10.1.1.10 has been initiated.
• D. R1 is configured with PAT overload parameters.
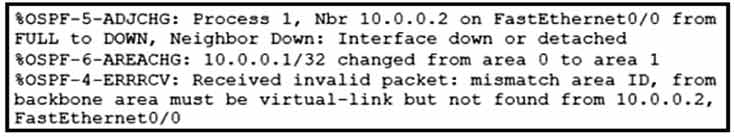
Refer to the exhibit. What is the cause of the log messages?
• A. OSPF area change
• B. MTU mismatch
• C. IP address mismatch
• D. hello packet mismatch
A network engineer configures BGP between R1 and R2. Both routers use BGP peer group CORP and are set up to use MD5 authentication. This message is logged to the console of router R1:
`May 5 39:85:55.469: %TCP-6-BADAUTH` Invalid MD5 digest from 10.10.10.1 (29832) to 10.120.10.1 (179) tebleid -0
Which two configurations allow a peering session to form between R1 and R2? (Choose two.)
• A. R1(config-router)#neighbor 10.10.10.1 peer-group CORP
R1(config-router)#neighbor CORP password Cisco
• B. R2(config-router)#neighbor 10.120.10.1 peer-group CORP
R2(config-router)#neighbor CORP password Cisco
• C. R2(config-router)#neighbor 10.10.10.1 peer-group CORP
R2(config-router)#neighbor PEER password Cisco
• D. R1(config-router)#neighbor 10.120.10.1 peer-group CORP
R1(config-router)#neighbor CORP password Cisco
• E. R2(config-router)#neighbor 10.10.10.1 peer-group CORP
R2(config-router)#neighbor CORP password Cisco
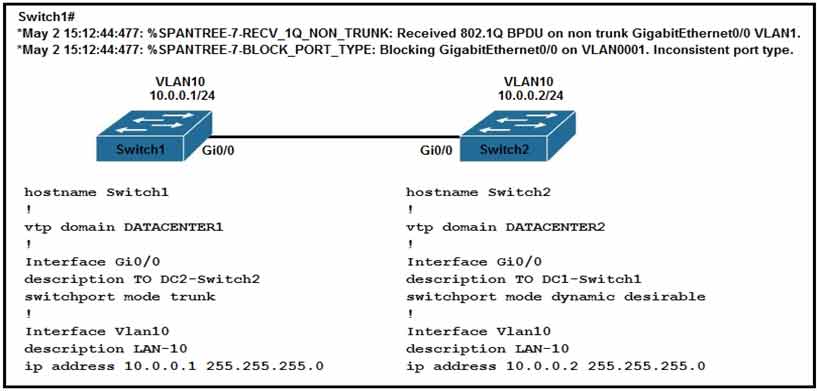
Refer to the exhibit. An engineer implemented several configuration changes and receives the logging message on Switch1. Which action should the engineer take to resolve this issue?
• A. Change Switch2 to switch port mode dynamic auto.
• B. Change the VTP domain to match on both switches.
• C. Change Switch1 to switch port mode dynamic auto.
• D. Change Switch1 to switch port mode dynamic desirable.
DRAG DROP –
Drag and drop the characteristics of PIM Dense Mode from the left to the right. Not all options are
used. Select and Place:
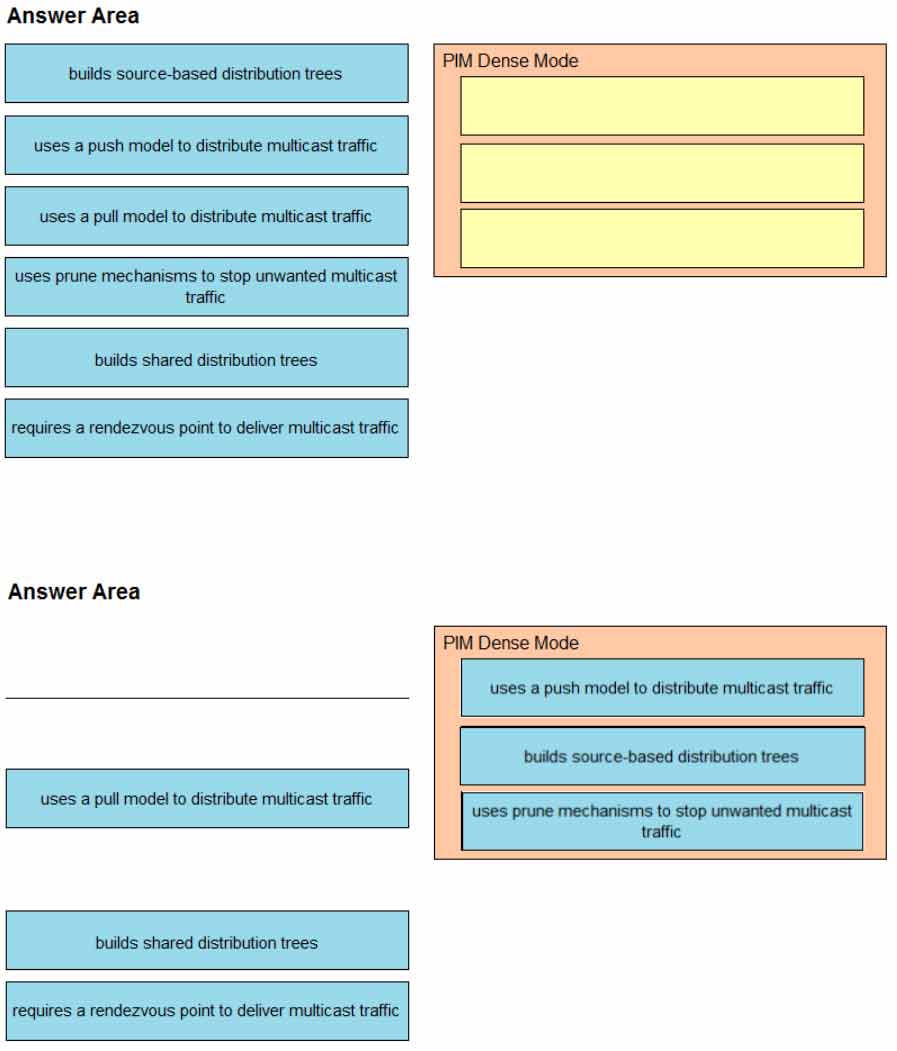
DRAG DROP –
Drag and drop the wireless elements on the left to their definitions on the right.
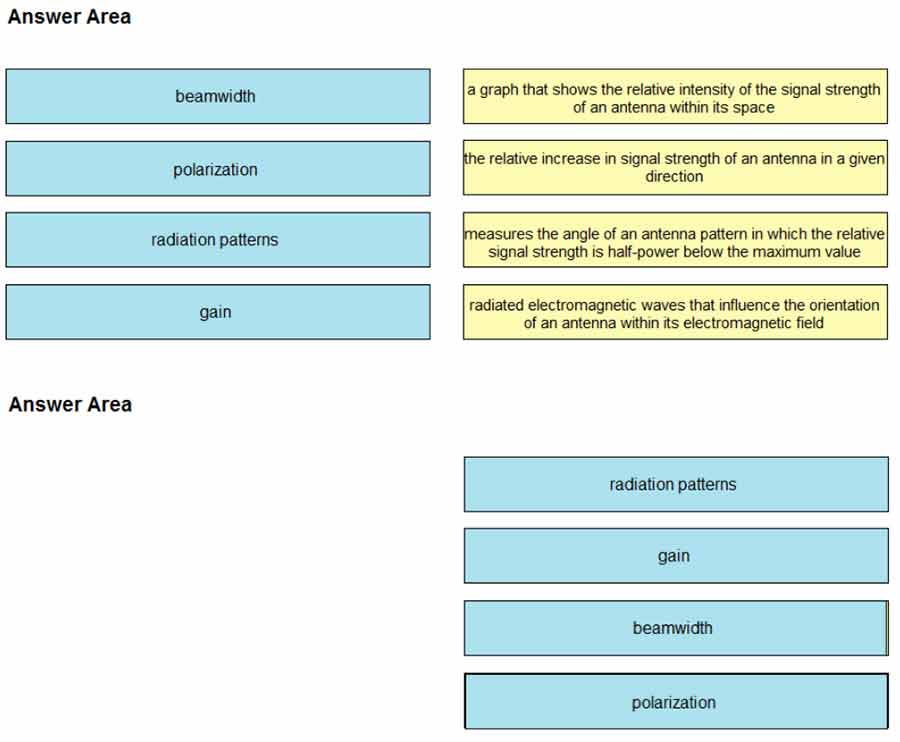
How are the different versions of IGMP compatible?
• A. IGMPv2 is compatible only with IGMPv2.
• B. IGMPv3 is compatible only with IGMPv3.
• C. IGMPv2 is compatible only with IGMPv1.
• D. IGMPv3 is compatible only with IGMPv1
Which measurement is used from a post wireless survey to depict the cell edge of the access points?
• A. SNR
• B. Noise
• C. RSSI
• D. CCI
If a client’s radio device receives a signal strength of -67 dBm and the noise floor is -85 dBm, what is the SNR value?
• A. 15 dB
• B. 16 dB
• C. 18 dB
• D. 20 dB
Which AP mode allows an engineer to scan configured channels for rogue access points?
• A. monitor
• B. bridge
• C. local
• D. sniffer
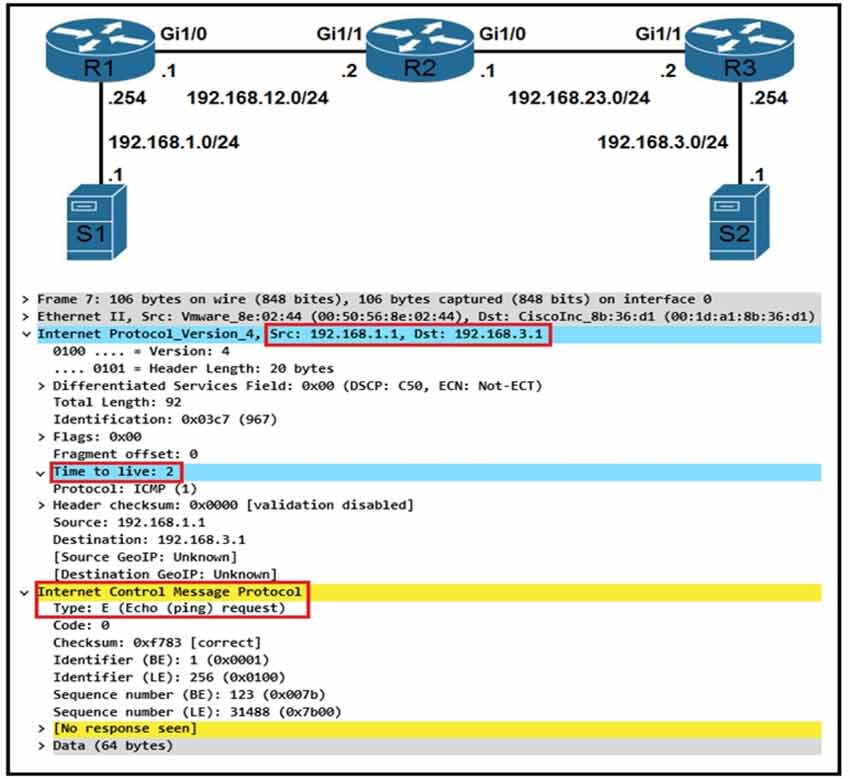
Refer to the exhibit. While troubleshooting a routing issue, an engineer issues a ping from S1 to S2.
Which two actions result from the initial value of the TTL? (Choose two.)
• A. The packet reaches R2, and the TTL expires.
• B. R1 replies with a TTL exceeded message.
• C. The packet reaches R3, and the TTL expires.
• D. R2 replies with a TTL exceeded message.
• E. R3 replies with a TTL exceeded message.
• F. The packet reaches R1, and the TTL expires.
What is the wireless Received Signal Strength Indicator?
• A. the value given to the strength of the wireless signal received compared to the noise level
• B. the value of how strong the wireless signal is leaving the antenna using transmit power, cable loss, and antenna gain
• C. the value of how much wireless signal is lost over a defined amount of distance
• D. the value of how strong a wireless signal is received, measured in dBm
Which two operational modes enable an AP to scan one or more wireless channels for rogue access points and at the same time provide wireless services to clients? (Choose two.)
• A. monitor
• B. rogue detector
• C. FlexConnect
• D. sniffer
• E. local
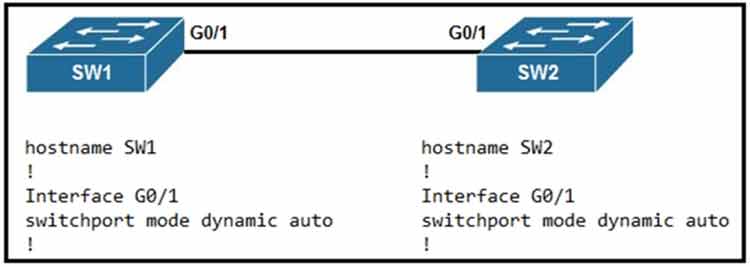
Refer to the exhibit. An engineer attempts to configure a trunk between switch SW1 and switch SW2 using DTP, but the trunk does not form. Which command should the engineer apply to switch SW2 to resolve this issue?
• A. switchport nonegotiate
• B. no switchport
• C. switchport mode dynamic desirable
• D. switchport mode access
An engineer is troubleshooting the AP join process using DNS. Which FQDN must be resolvable on the network for the access points to successfully register to the WLC?
• A. wlchostname.domain.com
• B. cisco-capwap-controller.domain.com
• C. ap-manager.domain.com
• D. primary-wlc.domain.com
Which new enhancement was implemented in Wi-Fi 6?
• A. Uplink and Downlink Orthogonal Frequency Division Multiple Access
• B. Channel bonding
• C. Wi-Fi Protected Access 3
• D. 4096 Quadrature Amplitude Modulation Mode
Which device makes the decision for a wireless client to roam?
• A. wireless client
• B. wireless LAN controller
• C. access point
• D. WCS location server
An engineer configures GigabitEthernet 0/1 for VRRP group 115. The router must assume the primary role when it has the highest priority in the group.
Which command set is required to complete this task?
interface GigabitEthernet0/1
ip address 10.10.10.2 255.255.255.0
vrrp 115 ip 10.10.10.1
vrrp 115 authentication 407441579
• A. Router(config if)# vrrp 115 track 1 decrement 100 Router(config-if)# vrrp 115 preempt
• B. Router(config-if)# vrrp 115 priority 100
• C. Router(config-if)# vrrp 115 track 1 decrement 10 Router(config-if)# vrrp 115 preempt
• D. Router(config-if)# standby 115 priority 100 Router(config-if)# standby 115 preempt
How is MSDP used to interconnect multiple PIM-SM domains?
• A. MSDP allows a rendezvous point to dynamically discover active sources outside of its domain.
• B. MSDP SA request messages are used to request a list of active sources for a specific group.
• C. MSDP depends on BGP or multiprotocol BGP for interdomain operation.
• D. MSDP messages are used to advertise active sources in a domain.
If the noise floor is -90 dBm and the wireless client is receiving a signal of
SNR?
• A. 15
• B. 1.2
• C. 165
• D. 83
Refer to the exhibit.
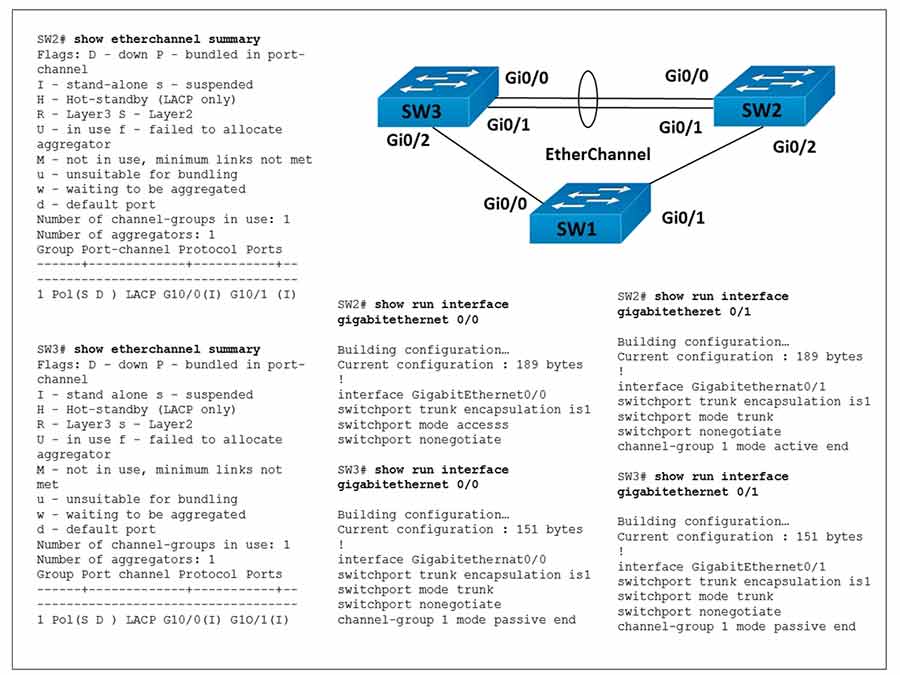
The EtherChannel between SW2 and SW3 is not operational. Which action resolves this issue?
• A. Configure the channel-group mode on SW3 Gi0/0 and Gi0/1 to active.
• B. Configure the mode on SW2 Gi0/0 to trunk.
• C. Configure the channel-group mode on SW2 Gi0/0 and Gi0/1 to on.
• D. Configure the mode on SW2 Gi0/1 to access.
Refer to the exhibit.
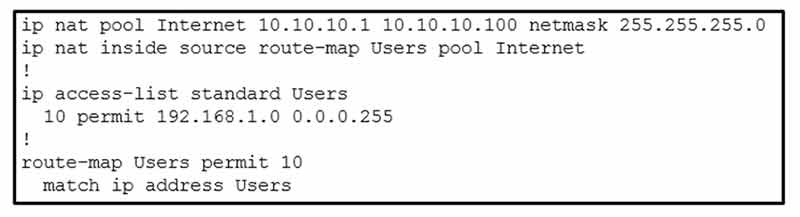
Which action completes the configuration to achieve a dynamic continuous mapped NAT for all users?
• A. Reconfigure the pool to use the 192.168.1.0 address range.
• B. Configure a match-host type NAT pool.
• C. Increase the NAT pool size to support 254 usable addresses.
• D. Configure a one-to-one type NAT pool.
How does EIGRP differ from OSPF?
• A. EIGRP is more prone to routing loops than OSPF.
• B. EIGRP uses more CPU and memory than OSPF.
• C. EIGRP has a full map of the topology, and OSPF only knows directly connected neighbors.
• D. EIGRP supports equal or unequal path cost, and OSPF supports only equal path cost.
Which AP mode allows a supported AP to function like a WLAN client would, associating and identifying client connectivity issues?
• A. client mode
• B. SE-connect mode
• C. sensor mode
• D. sniffer mode
A client device roams between wireless LAN controllers that are mobility peers. Both controllers have dynamic interfaces on the same client VLAN. Which type of roam is described?
• A. intra-VLAN
• B. inter-controller
• C. intra-controller
• D. inter-subnet
Which component does Cisco Threat Defense use to measure bandwidth, application performance, and utilization?
• A. TrustSec
• B. Advanced Malware Protection for Endpoints
• C. NetFlow
• D. Cisco Umbrella
Which IP SLA operation requires the IP SLA responder to be configured on the remote end?
• A. UDP jitter
• B. ICMP jitter
• C. TCP connect
• D. ICMP echo
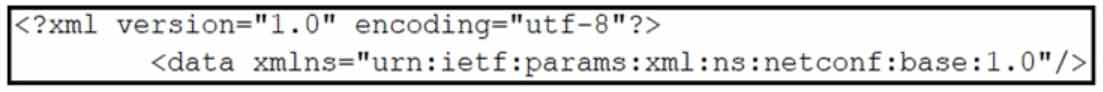
Refer to the exhibit. What does the error message relay to the administrator who is trying to configure a Cisco IOS device?
• A. The device received a valid NETCONF request and serviced it without error.
• B. The NETCONF running datastore is currently locked.
• C. A NETCONF request was made for a data model that does not exist.
• D. A NETCONF message with valid content based on the YANG data models was made, but the request failed.
Which three methods does Cisco DNA Center use to discover devices? (Choose three.)
• A. CDP
• B. SNMP
• C. LLDP
• D. ping
• E. NETCONF
• F. a specified range of IP addresses
Which statement about TLS is accurate when using RESTCONF to write configurations on network devices?
• A. It is used for HTTP and HTTPS requests.
• B. It requires certificates for authentication.
• C. It is provided using NGINX acting as a proxy web server.
• D. It is not supported on Cisco devices.
What do Cisco DNA southbound APIs provide?
• A. interface between the controller and the consumer
• B. RESTful API interface for orchestrator communication
• C. interface between the controller and the network devices
• D. NETCONF API interface for orchestrator communication
Which statement about an RSPAN session configuration is true?
• A. Only one session can be configured at a time.
• B. A special VLAN type must be used as the RSPAN destination.
• C. A filter must be configured for RSPAN sessions.
• D. Only incoming traffic can be monitored.
Which feature must be configured to allow packet capture over Layer 3 infrastructure?
• A. RSPAN
• B. ERSPAN
• C. VSPAN
• D. IPSPAN
Refer to the exhibit.
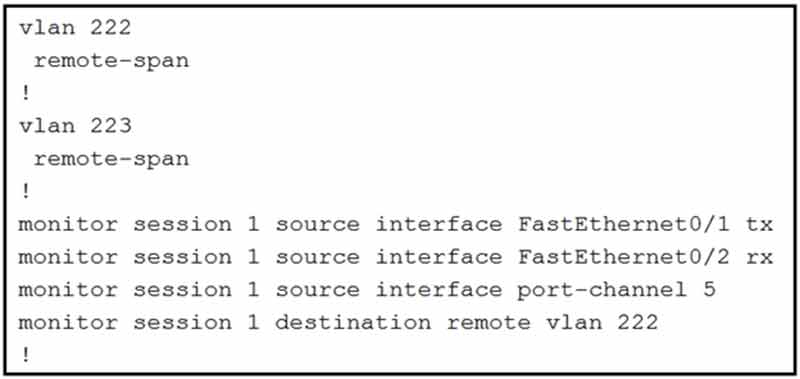
What is the result when a technician adds the monitor session 1 destination remote vlan 223 command?
• A. The RSPAN VLAN is replaced by VLAN 223.
• B. RSPAN traffic is sent to VLANs 222 and 223.
• C. An error is flagged for configuring two destinations.
• D. RSPAN traffic is split between VLANs 222 and 223.
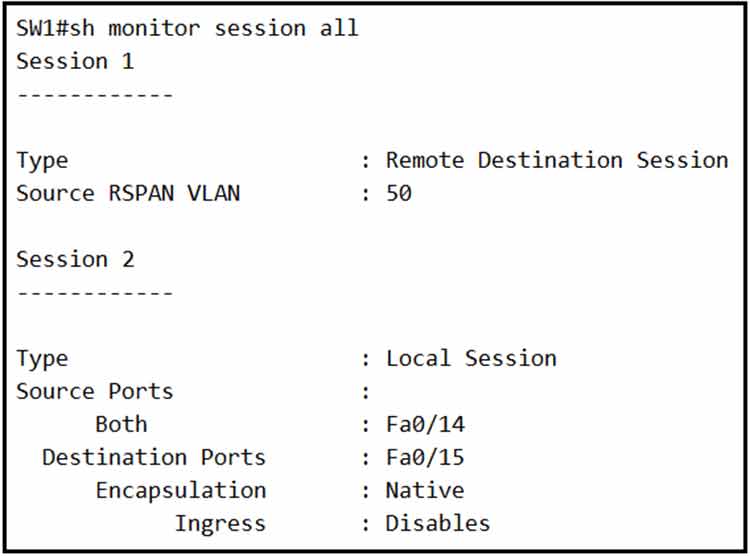
Refer to the exhibit. An engineer configures monitoring on SW1 and enters the show command to verify operation. What does the output confirm?
• A. RSPAN session 1 is incompletely configured for monitoring.
• B. RSPAN session 1 monitors activity on VLAN 50 of a remote switch.
• C. SPAN session 2 monitors all traffic entering and exiting port FastEthernet 0/15.
• D. SPAN session 2 only monitors egress traffic exiting port FastEthernet 0/14.
A network is being migrated from IPv4 to IPv6 using a dual-stack approach. Network management is already 100% IPv6 enabled.
In a dual-stack network with two dual-stack NetFlow collectors, how many flow exporters are needed per network device in the flexible NetFlow configuration?
• A. 1
• B. 2
• C. 4
• D. 8
A network engineer is configuring Flexible NetFlow and enters these commands. sampler NetFlow1 mode random one-out-of 100 interface fastethernet 1/0 flow-sampler NetFlow1 What are two results of implementing this feature instead of traditional NetFlow? (Choose two.)
• A. Only the flows of top 100 talkers are exported.
• B. CPU and memory utilization are reduced.
• C. The number of packets to be analyzed are reduced.
• D. The data export flow is more secure.
• E. The accuracy of the data to be analyzed is improved.
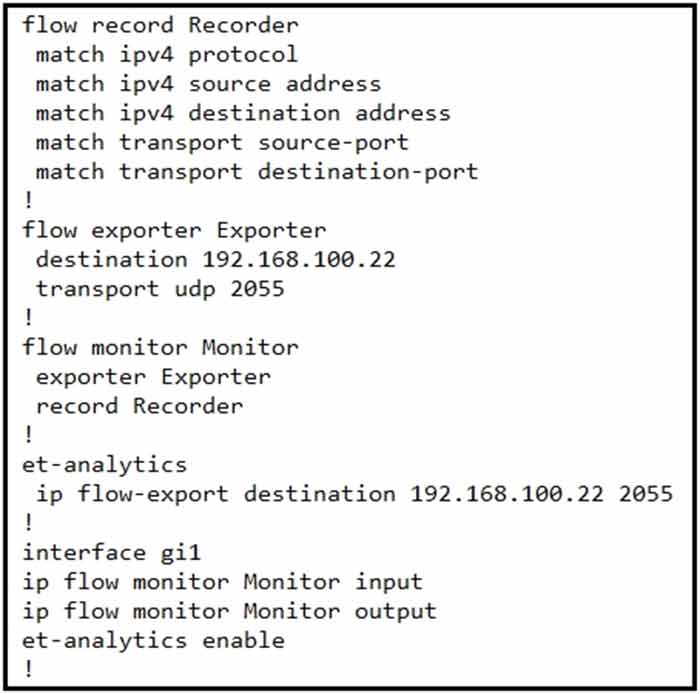
Refer to the exhibit. An engineer must add the SNMP interface table to the NetFlow protocol flow records. Where should the SNMP table option be added?
• A. under the interface
• B. under the flow record
• C. under the flow monitor
• D. under the flow exporter
A network administrator is implementing a routing configuration change and enables routing debugs to track routing behavior during the change. The logging output on the terminal is interrupting the command typing process.
Which two actions can the network administrator take to minimize the possibility of typing commands incorrectly? (Choose two.)
• A. Configure the logging synchronous global configuration command.
• B. Configure the logging synchronous command under the vty.
• C. Increase the number of lines on the screen using the terminal length command.
• D. Configure the logging delimiter feature.
• E. Press the TAB key to reprint the command in a new line.
When using TLS for syslog, which configuration allows for secure and reliable transportation of messages to its default port?
• A. logging host 10.2.3.4 vrf mgmt transport tcp port 514
• B. logging host 10.2.3.4 vrf mgmt transport udp port 514
• C. logging host 10.2.3.4 vrf mgmt transport tcp port 6514
• D. logging host 10.2.3.4 vrf mgmt transport udp port 6514
Refer to this output.
R1# *Feb 14 37:09:53.129: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/1,
changed state to up
What is the logging severity level?
• A. notification
• B. emergency
• C. critical
• D. alert
An engineer reviews a router’s logs and discovers the following entry. What is the event’s logging severity level?
Router# *Jan 01 38:24:04.401: %LINK-3-UPDOWN: Interface GigabitEthernet0/1, changed state to up
• A. error
• B. warning
• C. informational
• D. notification
Refer to the exhibit.
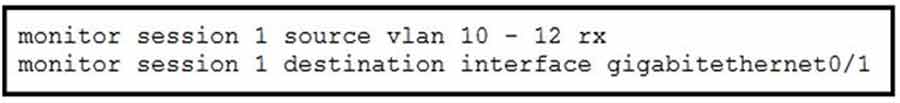
An engineer must configure a SPAN session.
What is the effect of the configuration?
• A. Traffic received on VLANs 10, 11, and 12 is copied and sent to interface g0/1.
• B. Traffic sent on VLANs 10 and 12 only is copied and sent to interface g0/1.
• C. Traffic sent on VLANs 10, 11, and 12 is copied and sent to interface g0/1.
• D. Traffic received on VLANs 10 and 12 only is copied and sent to interface g0/1.
Refer to the exhibit.
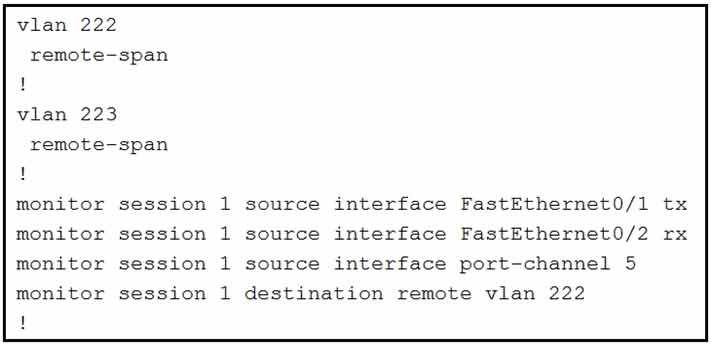
These commands have been added to the configuration of a switch.
Which command flags an error if it is added to this configuration?
• A. monitor session 1 source interface port-channel 6
• B. monitor session 1 source vlan 10
• C. monitor session 1 source interface FastEthemet0/1 rx
• D. monitor session 1 source interface port-channel 7, port-channel 8
Which method does Cisco DNA Center use to allow management of non-Cisco devices through southbound protocols?
• A. It creates device packs through the use of an SDK.
• B. It uses an API call to interrogate the devices and register the returned data.
• C. It obtains MIBs from each vendor that details the APIs available.
• D. It imports available APIs for the non-Cisco device in a CSV format.
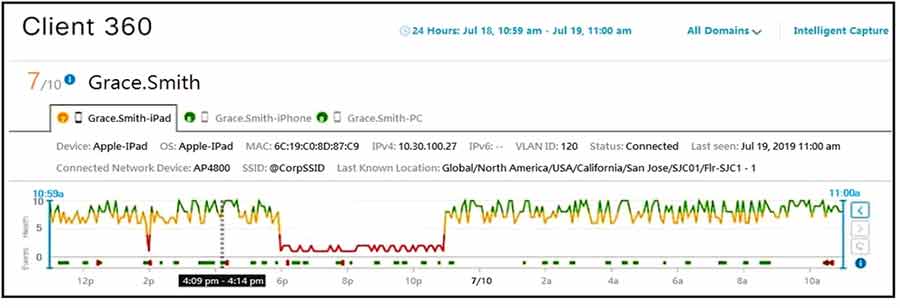
Refer to the exhibit. Cisco DNA Center has obtained the username of the client and the multiple devices that the client is using on the network. How is Cisco DNA Center getting these context details?
• A. Those details are provided to Cisco DNA Center by the Identity Services Engine.
• B. The administrator had to assign the username to the IP address manually in the user database tool on Cisco DNA Center.
• C. Cisco DNA Center pulled those details directly from the edge node where the user connected.
• D. User entered those details in the Assurance app available on iOS and Android devices.
Which command set configures RSPAN to capture outgoing traffic from VLAN 3 on interface GigabitEthernet 0/3 while ignoring other VLAN traffic on the same interface?
• A. monitor session 2 source interface gigabitethernet0/3 rx monitor session 2 filter vlan 3
• B. monitor session 2 source interface gigabitethernet0/3 rx monitor session 2 filter vlan 1 – 2, 4 – 4094
• C. monitor session 2 source interface gigabitethernet0/3 tx monitor session 2 filter vlan 3
• D. monitor session 2 source interface gigabitethernet0/3 tx monitor session 2 filter vlan 1- 2, 4 – 4094
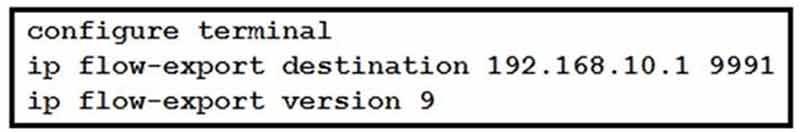
Refer to the exhibit. What is required to configure a second export destination for IP address 192.168.10.1?
• A. Specify a different UDP port.
• B. Specify a different TCP port.
• C. Configure a version 5 flow-export to the same destination.
• D. Specify a different flow ID.
• E. Specify a VRF.
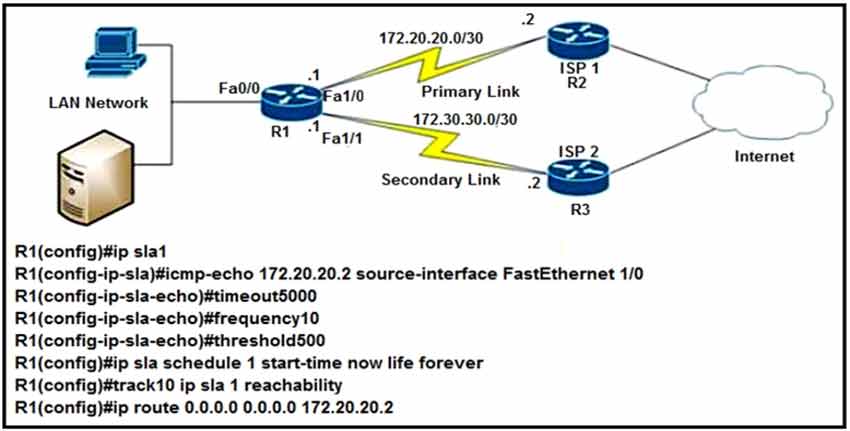
Refer to the exhibit. After implementing the configuration, 172.20.20.2 stops replying to ICMP echos, but the default route fails to be removed. What is the reason for this behavior?
• A. The threshold value is wrong.
• B. The source-interface is configured incorrectly.
• C. The destination must be 172.30.30.2 for icmp-echo.
• D. The default route is missing the track feature.
Refer to the exhibit.
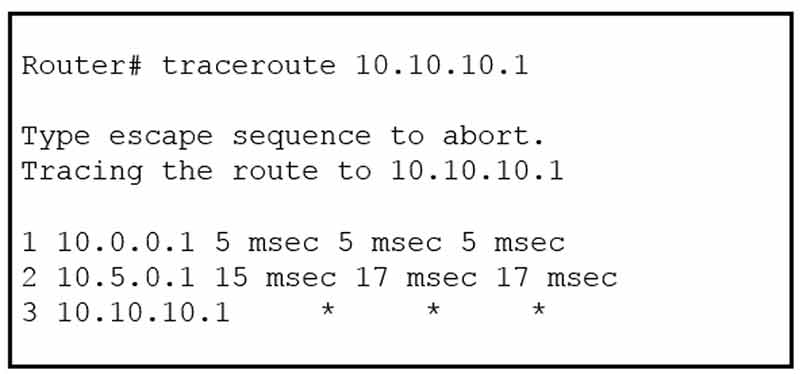
An engineer is troubleshooting a connectivity issue and executes a traceroute. What does the result confirm?
• A. The destination port is unreachable.
• B. The probe timed out.
• C. The destination server reported it is too busy.
• D. The protocol is unreachable.
Which Cisco DNA Center application is responsible for group-based access control permissions?
• A. Provision
• B. Design
• C. Assurance
• D. Policy
An engineer is concerned with the deployment of a new application that is sensitive to inter-packet
delay variance. Which command configures the router to be the destination of jitter measurements?
• A. Router(config)# ip sla responder udp-connect 172.29.139.134 5000
• B. Router(config)# ip sla responder tcp-connect 172.29.139.134 5000
• C. Router(config)# ip sla responder udp-echo 172.29.139.134 5000
• D. Router(config)# ip sla responder tcp-echo 172.29.139.134 5000
Which NGFW mode blocks flows crossing the firewall?
• A. tap
• B. inline
• C. passive
• D. inline tap
How does Cisco TrustSec enable more flexible access controls for dynamic networking environments and data centers?
• A. uses flexible NetFlow
• B. assigns a VLAN to the endpoint
• C. classifies traffic based on advanced application recognition
• D. classifies traffic based on the contextual identity of the endpoint rather than its IP address
The login method is configured on the VTY lines of a router with these parameters:
* The first method for authentication is TACACS
* If TACACS is unavailable, login is allowed without any provided credentials
Which configuration accomplishes this task?
A.
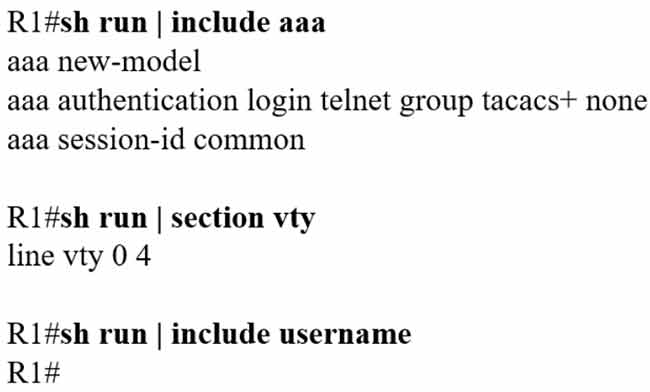
B.
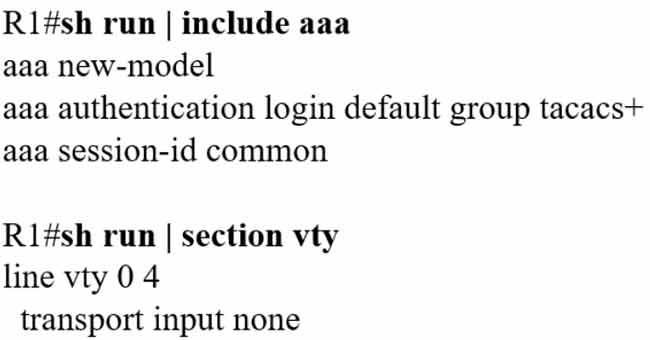
C.
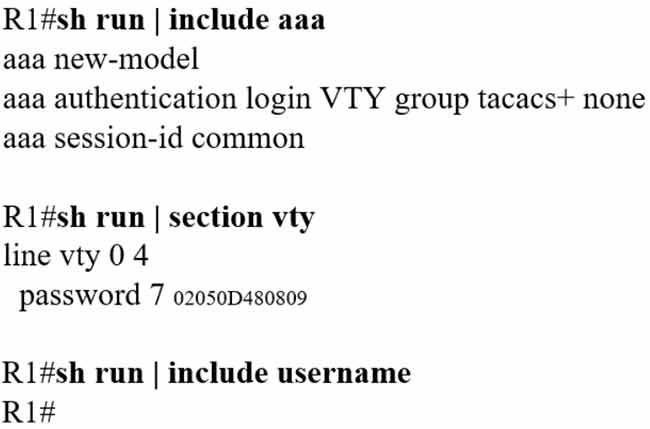
D.
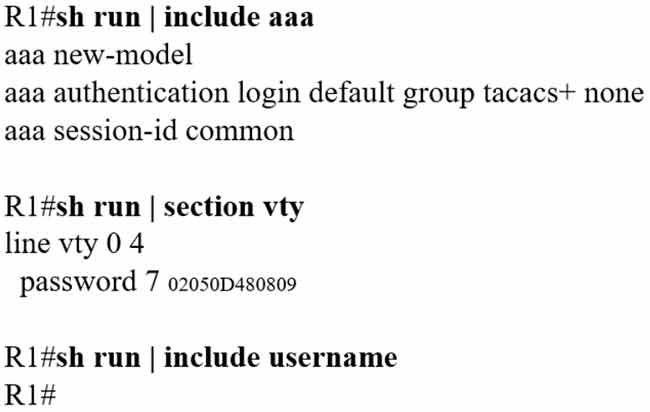
Correct Answer: D
Which feature does Cisco TrustSec use to provide scalable, secure communication throughout a network?
• A. security group tag ACL assigned to each port on a switch
• B. security group tag number assigned to each user on a switch
• C. security group tag number assigned to each port on a network
• D. security group tag ACL assigned to each router on a network
Which technology provides a secure communication channel for all traffic at Layer 2 of the OSI model?
• A. SSL
• B. Cisco TrustSec
• C. MACsec
• D. IPsec
An engineer is configuring local web authentication on a WLAN. The engineer chooses the Authentication radio button under the Layer 3 Security options for Web Policy.
Which device presents the web authentication for the WLAN?
• A. ISE server
• B. RADIUS server
• C. anchor WLC
• D. local WLC
Which method does the enable secret password option use to encrypt device passwords?
• A. MD5
• B. PAP
• C. CHAP
• D. AES
On which protocol or technology is the fabric data plane based in Cisco SD-Access fabric?
• A. VXLAN
• B. LISP
• C. Cisco TrustSec
• D. IS-IS
What is the difference between the enable password and the enable secret password when service password encryption is enabled on an IOS device?
• A. The enable secret password is protected via stronger cryptography mechanisms.
• B. The enable password cannot be decrypted.
• C. The enable password is encrypted with a stronger encryption method.
• D. There is no difference and both passwords are encrypted identically.
Which access control list allows only TCP traffic with a destination port range of 22-443, excluding port 80?
• A. deny tcp any any eq 80 permit tcp any any gt 21 lt 444
• B. permit tcp any any range 22 443 deny tcp any any eq 80
• C. permit tcp any any eq 80
• D. deny tcp any any eq 80 permit tcp any any range 22 443
A network administrator applies the following configuration to an IOS device: aaa new-model aaa authentication login default local group tacacs+
What is the process of password checks when a login attempt is made to the device?
• A. A TACACS+ server is checked first. If that check fails, a local database is checked.
• B. A TACACS+ server is checked first. If that check fails, a RADIUS server is checked. If that check fails, a local database is checked.
• C. A local database is checked first. If that check fails, a TACACS+ server is checked. If that check fails, a RADIUS server is checked.
• D. A local database is checked first. If that check fails, a TACACS+ server is checked.
Refer to the exhibit.
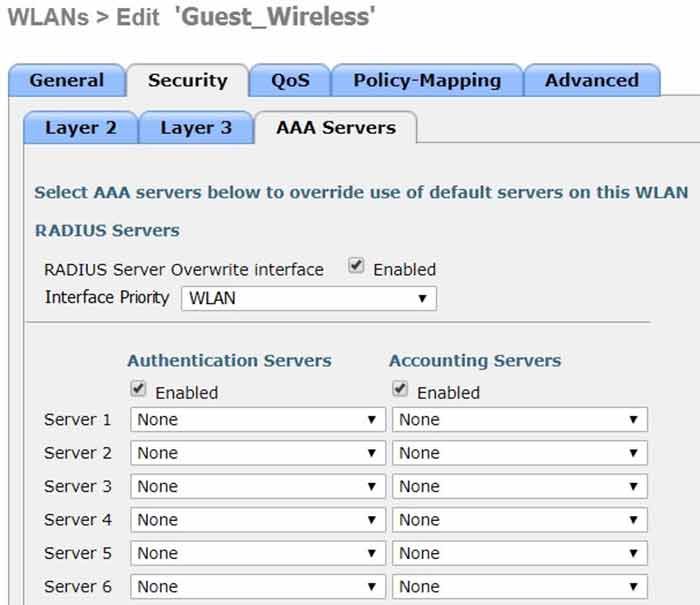
Assuming the WLC’s interfaces are not in the same subnet as the RADIUS server, which interface would the WLC use as the source for all RADIUS-related traffic?
• A. the controller management interface
• B. the controller virtual interface
• C. the interface specified on the WLAN configuration
• D. any interface configured on the WLC
Which component of the Cisco Cyber Threat Defense solution provides user and flow context analysis?
• A. Cisco Firepower and FireSIGHT
• B. Cisco Stealthwatch system
• C. Advanced Malware Protection
• D. Cisco Web Security Appliance
An engineer must protect their company against ransomware attacks.
Which solution allows the engineer to block the execution stage and prevent file encryption?
• A. Use Cisco Firepower and block traffic to TOR networks.
• B. Use Cisco AMP deployment with the Malicious Activity Protection engine enabled.
• C. Use Cisco Firepower with Intrusion Policy and snort rules blocking SMB exploitation.
• D. Use Cisco AMP deployment with the Exploit Prevention engine enabled.
Refer to the exhibit.
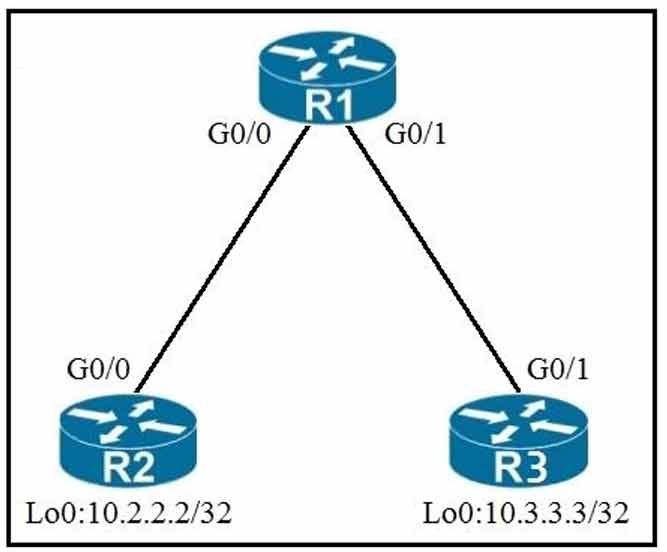
An engineer must deny Telnet traffic from the loopback interface of router R3 to the loopback interface of router R2 during the weekend hours. All other traffic between the loopback interfaces of routers R3 and R2 must be allowed at all times.
Which command set accomplishes this task?
• A. R3(config)#time-range WEEKEND
R3(config-time-range)#periodic Saturday Sunday 00:00 to 23:59
R3(config)#access-list 150 deny tcp host 10.3.3.3 host 10.2.2.2 eq 23 time-range WEEKEND
R3(config)#access-list 150 permit ip any any time-range WEEKEND
R3(config)#interface G0/1 R3(config-if)#ip access-group 150 out
• B. R1(config)#time-range WEEKEND
R1(config-time-range)#periodic weekend 00:00 to 23:59
R1(config)#access-list 150 deny tcp host 10.3.3.3 host 10.2.2.2 eq 23 time-range WEEKEND
R1(config)#access-list 150 permit ip any any R1(config)#interface G0/1
R1(config-if)#ip access-group 150 in
• C. R3(config)#time-range WEEKEND
R3(config-time-range)#periodic weekend 00:00 to 23:59
R3(config)#access-list 150 permit tcp host 10.3.3.3 host 10.2.2.2 eq 23 time-range WEEKEND
R3(config)#access-list 150 permit ip any any time-range WEEKEND
R3(config)#interface G0/1
R3(config-if)#ip access-group 150 out
• D. R1(config)#time-range WEEKEND
R1(config-time-range)#periodic Friday Sunday 00:00 to 00:00
R1(config)#access-list 150 deny tcp host 10.3.3.3 host 10.2.2.2 eq 23 time-range WEEKEND
R1(config)#access-list 150 permit ip any any R1(config)#interface G0/1
R1(config if)#ip access-group 150 in
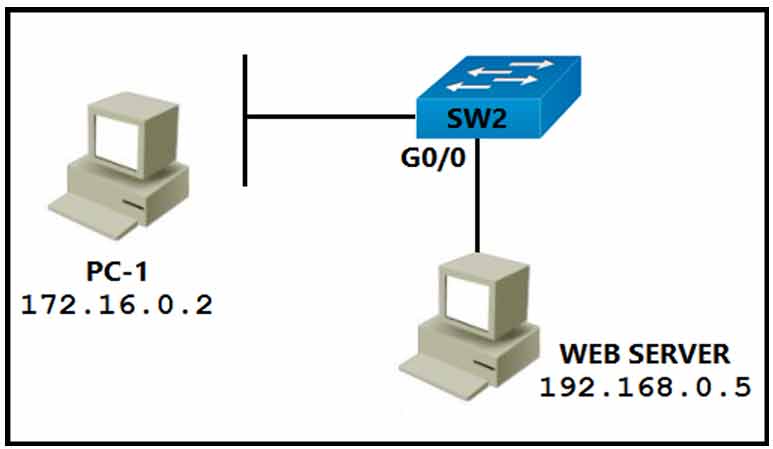
Refer to the exhibit. PC-1 must access the web server on port 8080. To allow this traffic, which statement must be added to an access control list that is applied on SW2 port G0/0 in the inbound direction?
• A. permit tcp host 172.16.0.2 host 192.168.0.5 eq 8080
• B. permit tcp host 192.168.0.5 host 172.16.0.2 eq 8080
• C. permit tcp host 192.168.0.5 eq 8080 host 172.16.0.2
• D. permit tcp host 192.168.0.5 lt 8080 host 172.16.0.2
What is the result of applying this access control list?
ip access-list extended STATEFUL
10 permit tcp any any established
20 deny ip any any
• A. TCP traffic with the URG bit set is allowed.
• B. TCP traffic with the SYN bit set is allowed.
• C. TCP traffic with the ACK bit set is allowed.
• D. TCP traffic with the DF bit set is allowed.
Which outbound access list, applied to the WAN interface of a router, permits all traffic except for http traffic sourced from the workstation with IP address 10.10.10.1?
• A. ip access-list extended 200 deny tcp host 10.10.10.1 eq 80 any permit ip any any
• B. ip access-list extended 10 deny tcp host 10.10.10.1 any eq 80 permit ip any any
• C. ip access-list extended NO_HTTP deny tcp host 10.10.10.1 any eq 80
• D. ip access-list extended 100 deny tcp host 10.10.10.1 any eq 80 permit ip any any
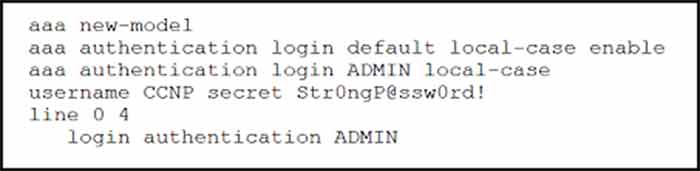
Refer to the exhibit. An engineer must create a configuration that executes the show run command and then terminates the session when user CCNP logs in. Which configuration change is required?
• A. Add the access-class keyword to the username command.
• B. Add the autocommand keyword to the aaa authentication command.
• C. Add the access-class keyword to the aaa authentication command.
• D. Add the autocommand keyword to the username command.
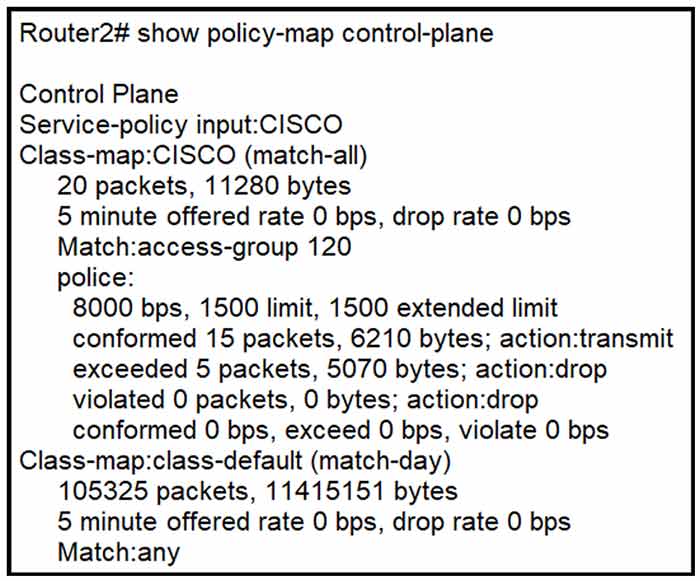
Refer to the exhibit. An engineer configures CoPP and enters the show command to verify the implementation. What is the result of the configuration?
• A. All traffic will be policed based on access-list 120.
• B. If traffic exceeds the specified rate, it will be transmitted and remarked.
• C. Class-default traffic will be dropped.
• D. ICMP will be denied based on this configuration.
DRAG DROP –
Drag and drop the threat defense solutions from the left onto their descriptions on the right.
Select and Place:
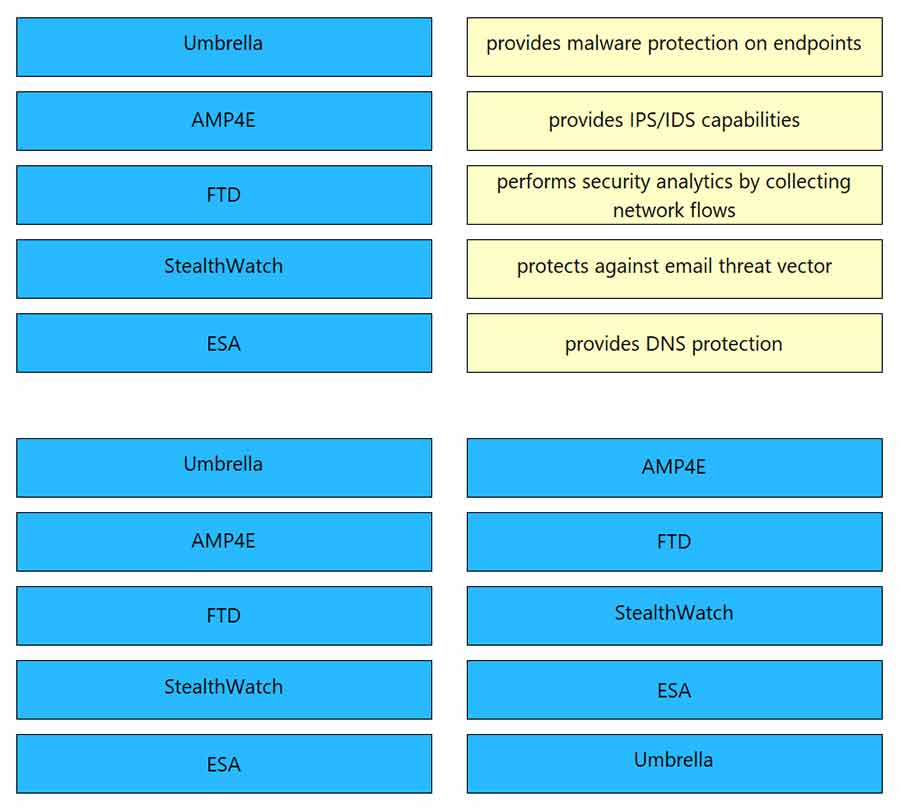
Refer to the exhibit.
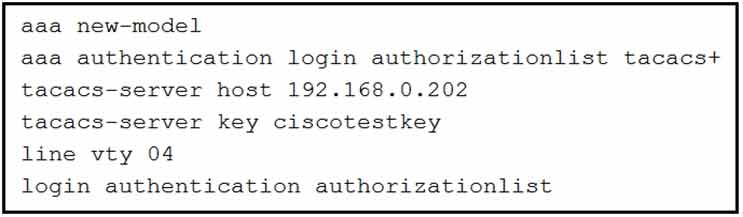
What is the effect of this configuration?
• A. The device will allow users at 192.168.0.202 to connect to vty lines 0 through 4 using the password ciscotestkey.
• B. The device will authenticate all users connecting to vty lines 0 through 4 against TACACS+.
• C. The device will allow only users at 192.168.0.202 to connect to vty lines 0 through 4.
• D. When users attempt to connect to vty lines 0 through 4, the device will authenticate them against TACACS+ if local authentication fails.
Which deployment option of Cisco NGFW provides scalability?
• A. inline tap
• B. high availability
• C. clustering
• D. tap
DRAG DROP –
Drag and drop the REST API authentication methods from the left onto their descriptions on the
right.
Select and Place:
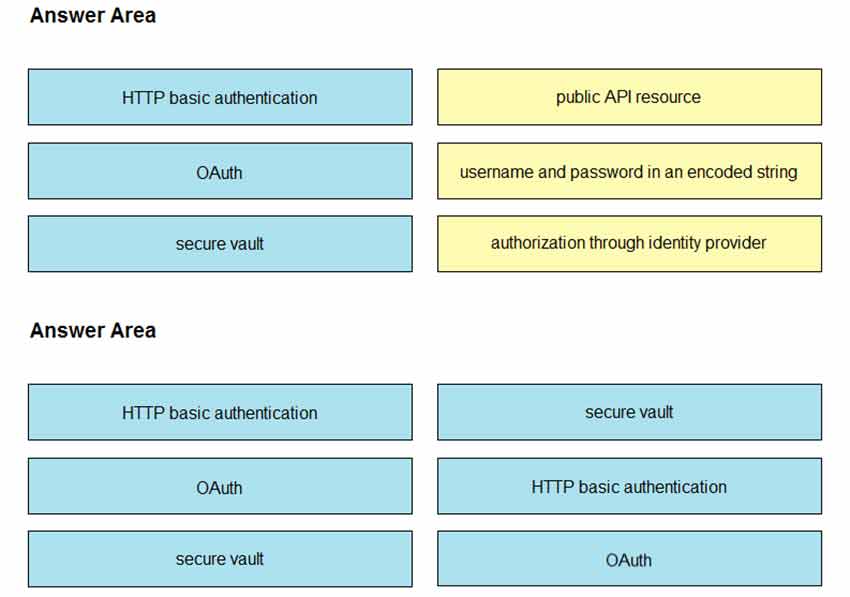
In a Cisco SD-Access solution, what is the role of the Identity Services Engine?
• A. It is leveraged for dynamic endpoint to group mapping and policy definition.
• B. It provides GUI management and abstraction via apps that share context.
• C. It is used to analyze endpoint to app flows and monitor fabric status.
• D. It manages the LISP EID database.
DRAG DROP –
Drag and drop the solutions that compromise Cisco Cyber Threat Defense from the left onto the
objectives they accomplish on the right.
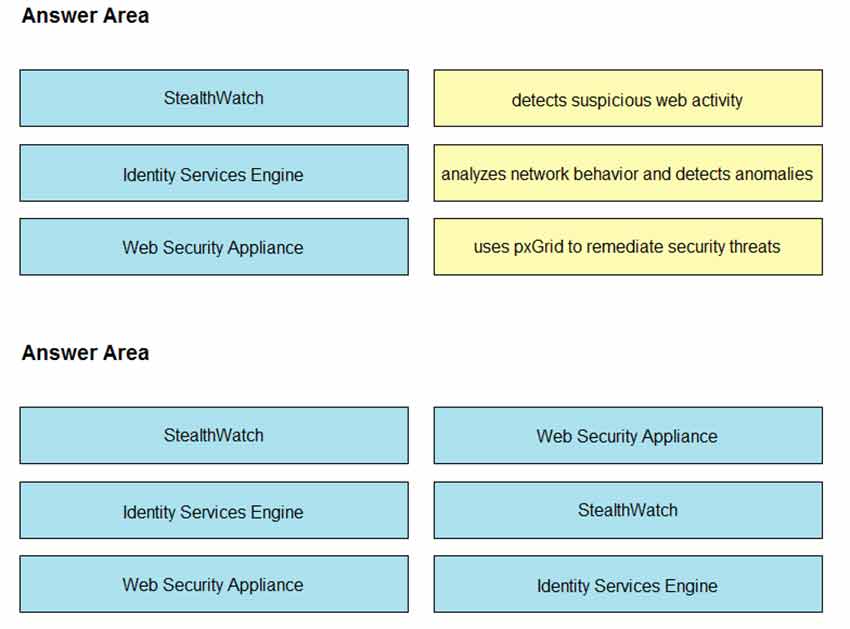
Question 414
DRAG DROP –
An engineer creates the configuration below. Drag and drop the authentication methods from the
left into the order of priority on the right. Not all options are used.
R1#sh run | i aaa – aaa new-model
aaa authentication login default group ACE group AAA_RADIUS local-case aaa session-id common
R1#
Select and Place:
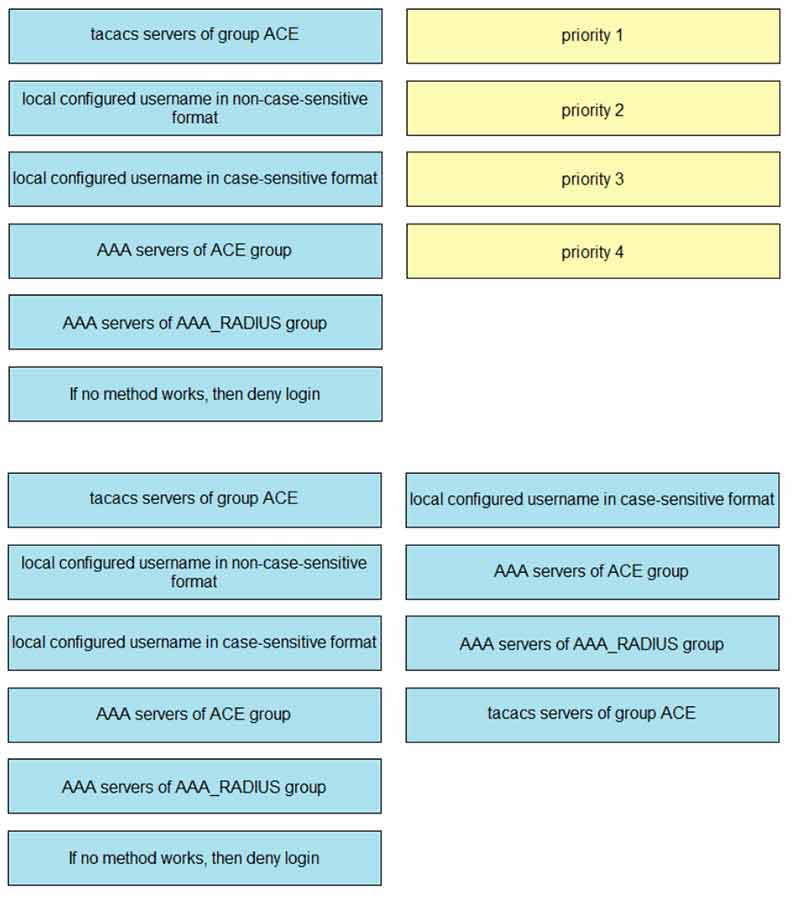
What is provided by the Stealthwatch component of the Cisco Cyber Threat Defense solution?
• A. real-time threat management to stop DDoS attacks to the core and access networks
• B. real-time awareness of users, devices, and traffic on the network
• C. malware control
• D. dynamic threat control for web traffic
An engineer must configure an ACL that permits packets which include an ACK in the TCP header.
Which entry must be included in the ACL?
• A. access-list 110 permit tcp any any eq 21 tcp-ack
• B. access-list 10 permit tcp any any eq 21 established
• C. access-list 110 permit tcp any any eq 21 established
• D. access-list 10 permit ip any any eq 21 tcp-ack
A client with IP address 209.165.201.25 must access a web server on port 80 at 209.165.200.225. To allow this traffic, an engineer must add a statement to an access control list that is applied in the inbound direction on the port connecting to the web server. Which statement allows this traffic?
• A. permit tcp host 209.165.200.225 lt 80 host 209.165.201.25
• B. permit tcp host 209.165.201.25 host 209.165.200.225 eq 80
• C. permit tcp host 209.165.200.225 eq 80 host 209.165.201.25
• D. permit tcp host 209.165.200.225 host 209.165.201.25 eq 80
Which standard access control entry permits traffic from odd-numbered hosts in the 10.0.0.0/24 subnet?
• A. permit 10.0.0.0 0.0.0.1
• B. permit 10.0.0.1 0.0.0.254
• C. permit 10.0.0.1 0.0.0.0
• D. permit 10.0.0.0 255.255.255.254
Refer to the exhibit.
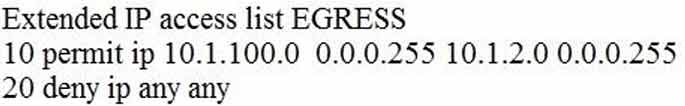
An engineer must modify the access control list EGRESS to allow all IP traffic from subnet 10.1.10.0/24 to 10.1.2.0/24. The access control list is applied in the outbound direction on router interface GigabitEthernet 0/1.
Which configuration command set will allow this traffic without disrupting existing traffic flows?
A.
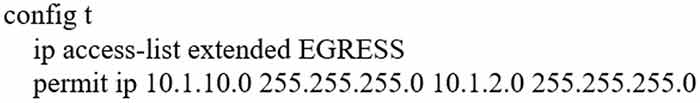
B.
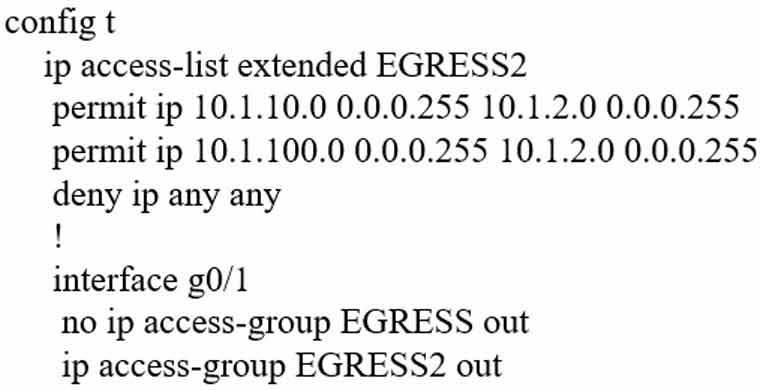
C.
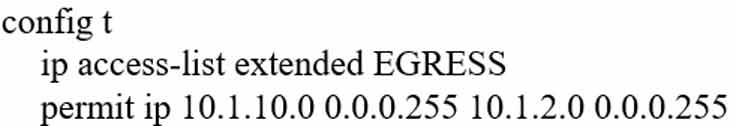
D.
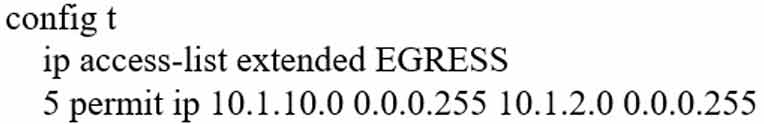
Correct Answer: D
Which configuration restricts the amount of SSH traffic that a router accepts to 100 kbps?
A.
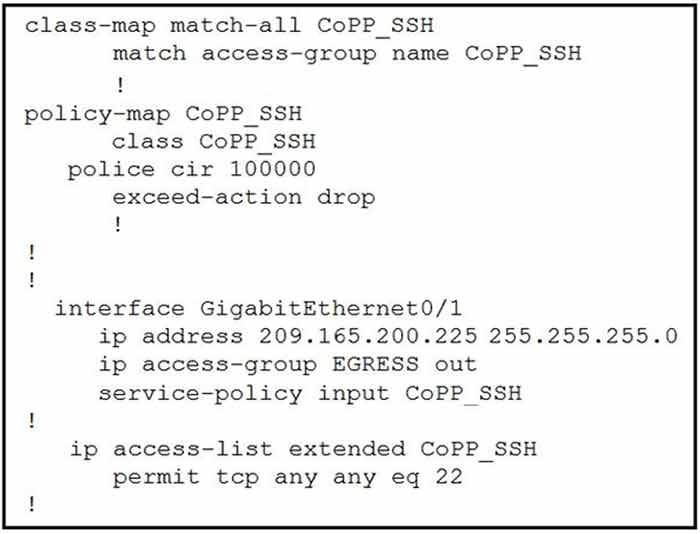
B.
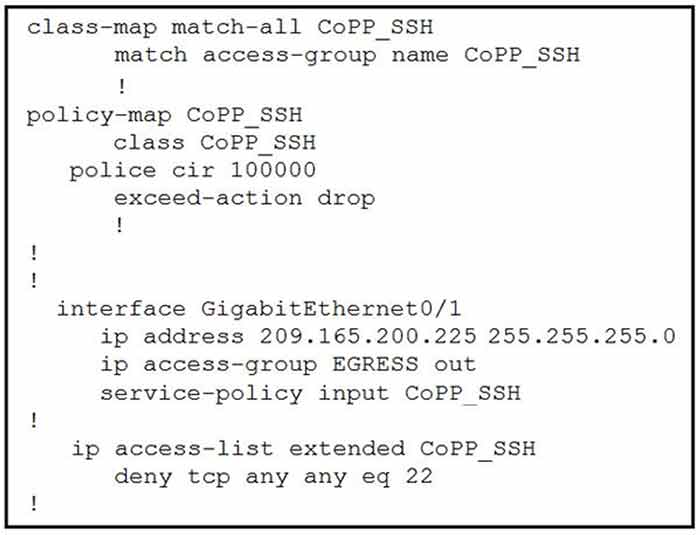
C.
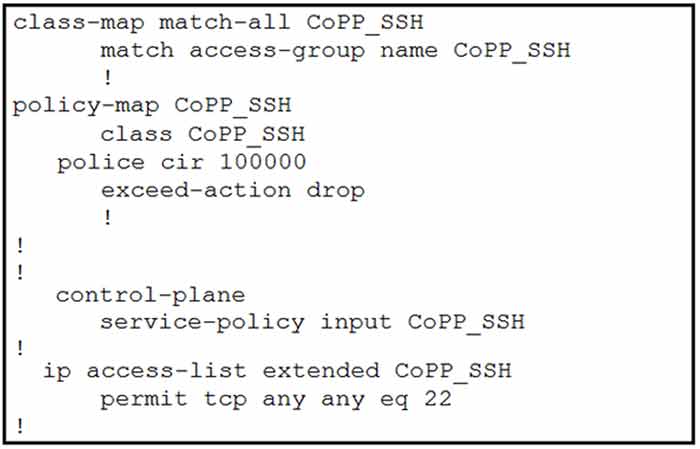
D.
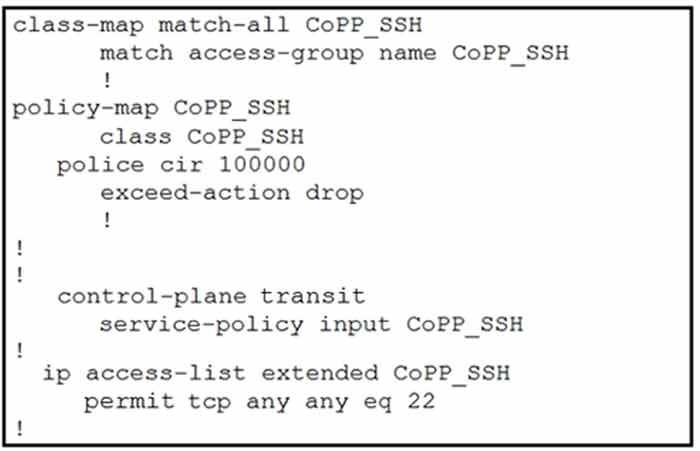
Correct Answer: C
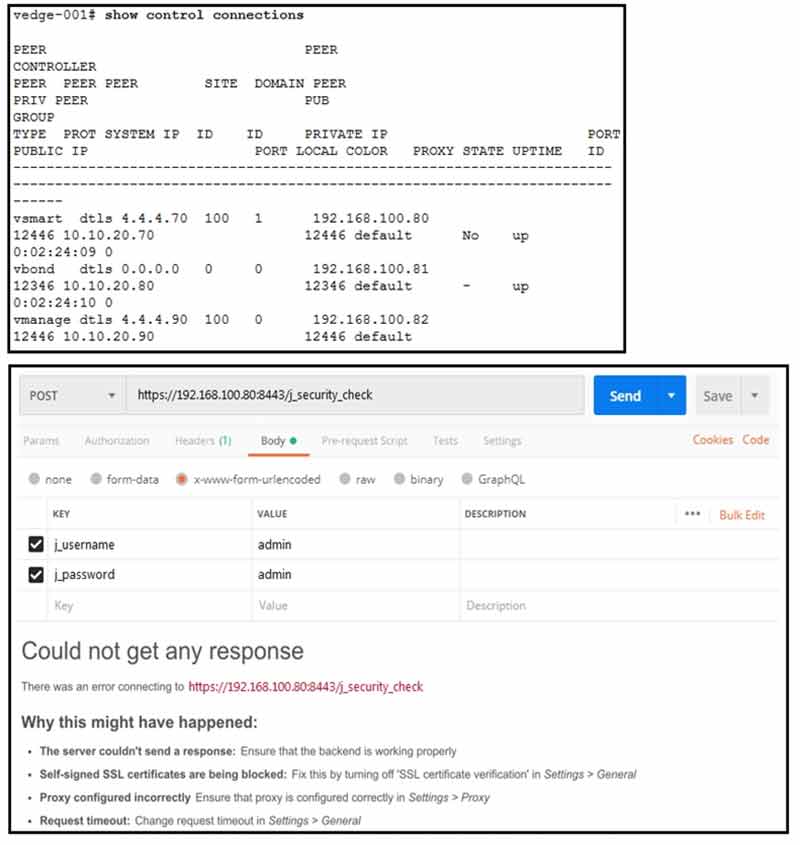
Refer to the exhibit. What step resolves the authentication issue?
• A. use basic authentication
• B. change the port to 12446
• C. target 192.168.100.82 in the URI
• D. restart the vsmart host
Refer to the exhibit.
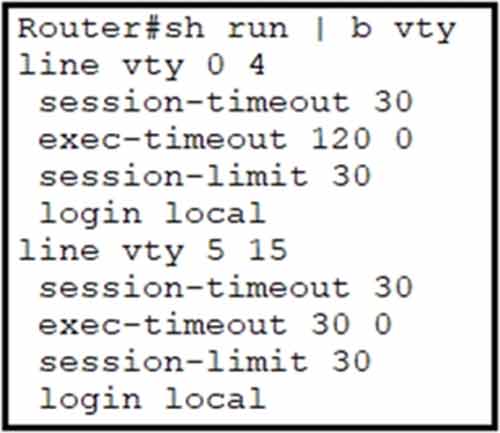
Security policy requires all idle exec sessions to be terminated in 600 seconds. Which configuration achieves this goal?
• A. line vty 0 15 absolute-timeout 600
• B. line vty 0 15 no exec-timeout
• C. line vty 0 15 exec-timeout 10 0
• D. line vty 0 4 exec-timeout 600
Refer to the exhibit.
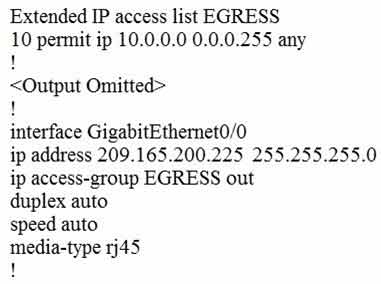
An engineer must block all traffic from a router to its directly connected subnet 209.165.200.0/24.
The engineer applies access control list EGRESS in the outbound direction on the GigabitEthernet0/0 interface of the router. However, the router can still ping hosts on the 209.165.200.0/24 subnet. What explains this behavior?
• A. Access control lists that are applied outbound to a router interface do not affect traffic that is sourced from the router.
• B. After an access control list is applied to an interface, that interface must be shut and no shut for the access control list to take effect.
• C. Only standard access control lists can block traffic from a source IP address.
• D. The access control list must contain an explicit deny to block traffic from the router.
What is a characteristic of a next-generation firewall?
• A. only required at the network perimeter
• B. required in each layer of the network
• C. filters traffic using Layer 3 and Layer 4 information only
• D. provides intrusion prevention
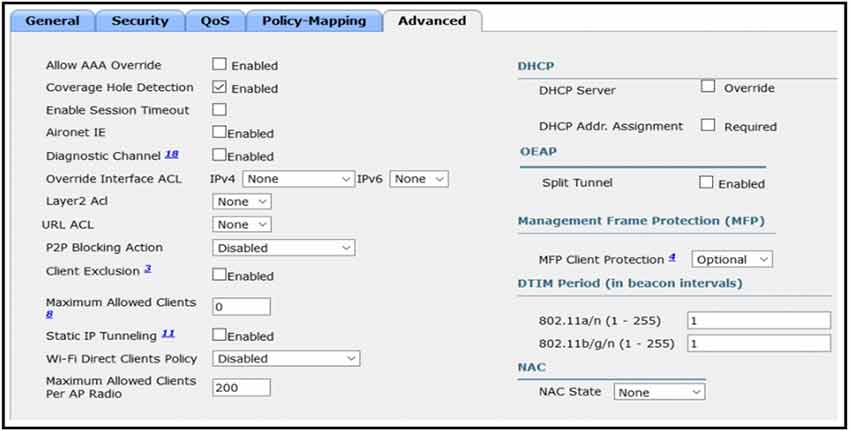
Refer to the exhibit. An engineer is investigating why guest users are able to access other guest user devices when the users are connected to the customer guest WLAN. What action resolves this issue?
• A. implement P2P blocking
• B. implement MFP client protection
• C. implement Wi-Fi direct policy
• D. implement split tunneling
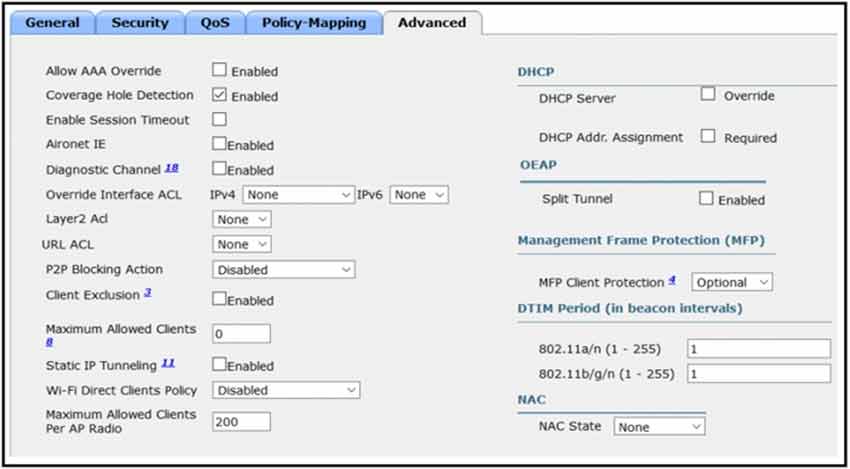
Refer to the exhibit. An engineer has configured Cisco ISE to assign VLANs to clients based on their method of authentication, but this is not working as expected. Which action will resolve this issue?
• A. enable AAA override
• B. set a NAC state
• C. utilize RADIUS profiling
• D. require a DHCP address assignment
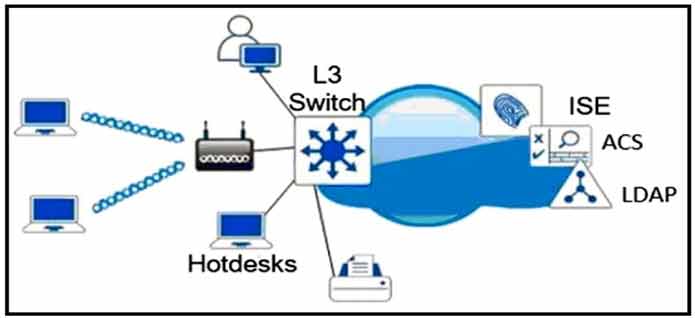
Refer to the exhibit. Which single security feature is recommended to provide Network Access Control in the enterprise?
• A. MAB
• B. 802.1X
• C. WebAuth
• D. port security sticky MAC
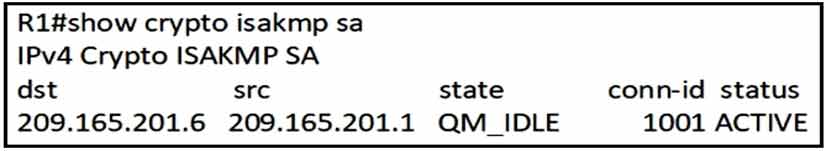
Refer to the exhibit. After configuring an IPsec VPN, an engineer enters the show command to verify the ISAKMP SA status. What does the status show?
• A. VPN peers agreed on parameters for the ISAKMP SA.
• B. Peers have exchanged keys, but ISAKMP SA remains unauthenticated.
• C. ISAKMP SA is authenticated and can be used for Quick Mode.
• D. ISAKMP SA has been created, but it has not continued to form.
Which two threats does AMP4E have the ability to block? (Choose two.)
• A. email phishing
• B. DDoS
• C. Microsoft Word macro attack
• D. SQL injection
• E. ransomware
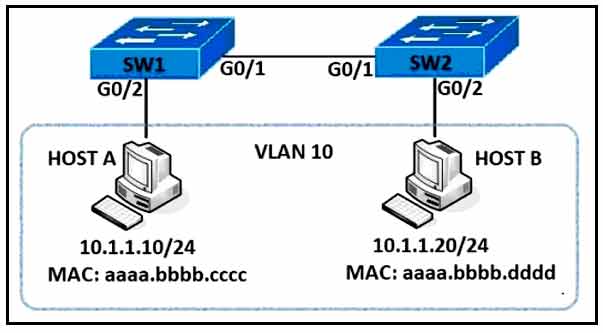
Refer to the exhibit. An engineer must deny HTTP traffic from host A to host B while allowing all other communication between the hosts. Drag and drop the commands into the configuration to achieve these results. Some commands may be used more than once. Not all commands are used.
Select and Place:
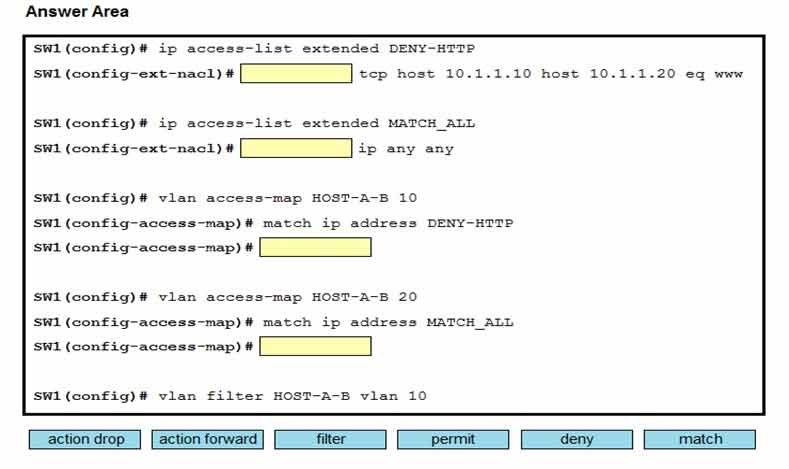
Answer:
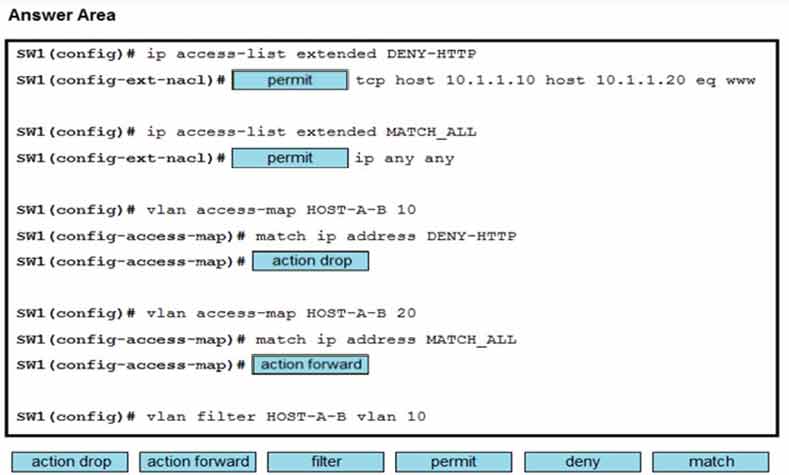
An engineer must configure the strongest password authentication to locally authenticate on a router. Which configuration must be used?
• A. username netadmin secret 5 $1$b1Ju$kZbBS1Pyh4QzwXyZ1kSZ2
• B. username netadmin secret 9 $9$vFpMf8elb4RVV8$seZ/bDAx1uV
• C. username netadmin secret $1$b1Ju$k406689705QzwXyZ1kSZ2
• D. line Console 0 password $1$b1Ju$
What is a characteristic of MACsec?
• A. 802.1AE is built between the host and switch using the MKA protocol, which negotiates encryption keys based on the primary session key from a successful 802.1X session.
• B. 802.1AE is negotiated using Cisco AnyConnect NAM and the SAP protocol.
• C. 802.1AE is built between the host and switch using the MKA protocol using keys generated via the Diffie-Hellman algorithm (anonymous encryption mode).
• D. 802.1AE provides encryption and authentication services.
Question 433
Refer to the exhibit. A network engineer attempts to connect to the Router1 console port.
Which configuration is needed to allow Telnet connections?
• A. Router1(config)# line vty 0 15
Router1(config-line)# transport output telnet
• B. Router1(config)# telnet client
• C. Router1(config)# line console 0
Router1(config-line)# transport output telnet
• D. Router1(config)# access-list 100 permit tcp any any eq telnet
Router1(config)# line console 0
Router1(config-line)# access-class 100 out
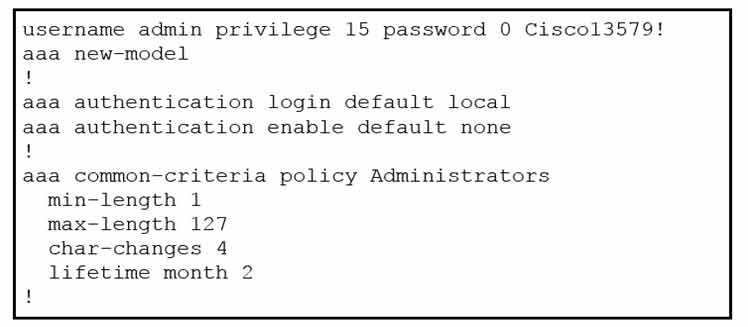
A network engineer must configure a password expiry mechanism on the gateway router for all local passwords to expire after 60 days. What is required to complete this task?
• A. Add the username admin privilege 15 common-criteria-policy Administrators password 0 Cisco13579! command.
• B. The password expiry mechanism is on the AAA server and must be configured there.
• C. Add the aaa authentication enable default Administrators command.
• D. No further action is required. The configuration is complete.
Refer to the exhibit.
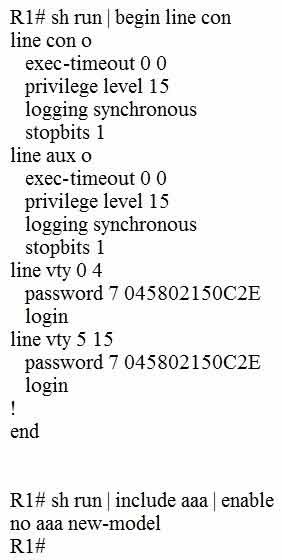
Which privilege level is assigned to VTY users?
• A. 1
• B. 7
• C. 13
• D. 15
Which statements are used for error handling in Python?
• A. try/catch
• B. catch/release
• C. block/rescue
• D. try/except
How do agent-based versus agentless configuration management tools compare?
• A. Agentless tools use proxy nodes to interface with slave nodes.
• B. Agentless tools require no messaging systems between master and slaves.
• C. Agent-based tools do not require a high-level language interpreter such as Python or Ruby on slave nodes.
• D. Agent-based tools do not require installation of additional software packages on the slave nodes.
Question 438
Refer to the exhibit.
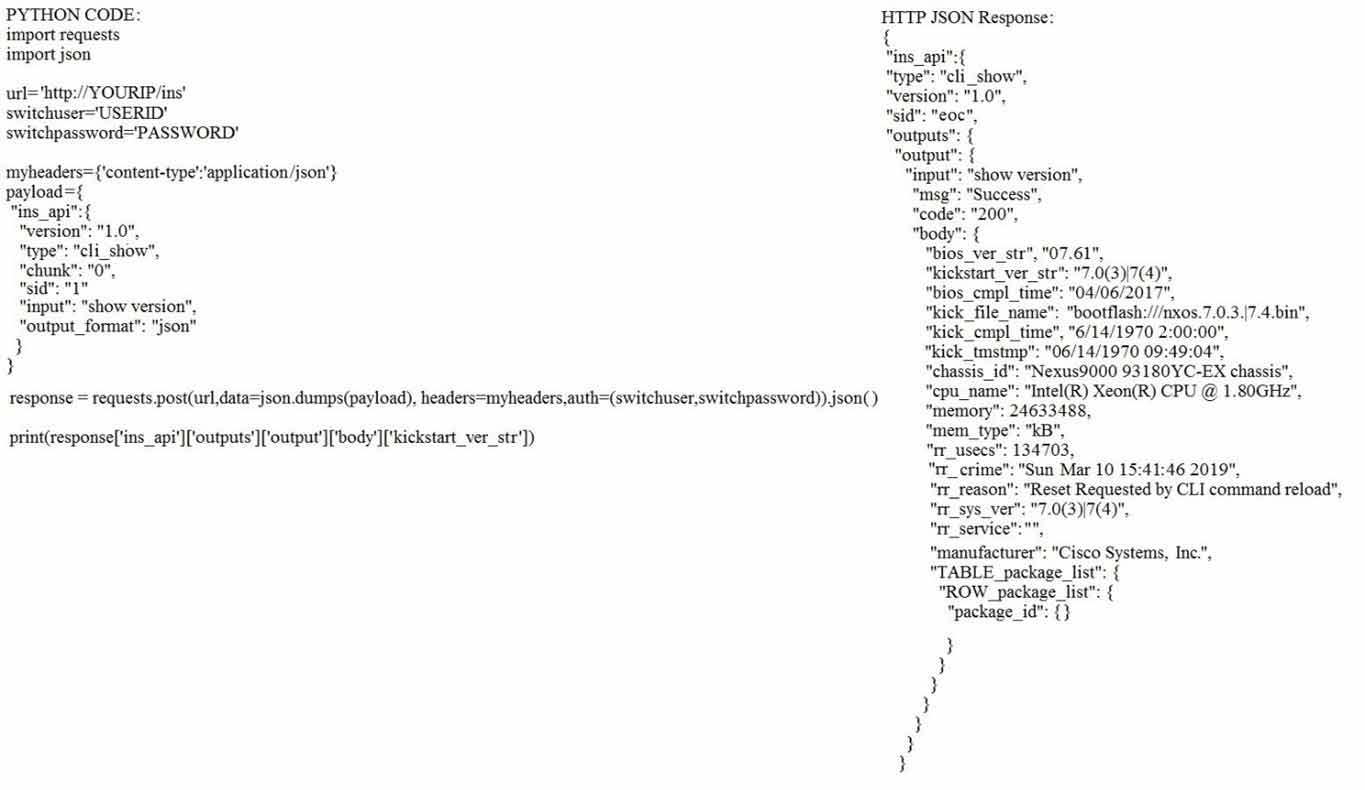
Which HTTP JSON response does the Python code output give?
• A. 7.0(3)|7(4)
• B. 7.61
• C. NameError: name ‘json’ is not defined
• D. KeyError: ‘kickstart_ver_str’
A network administrator is preparing a Python script to configure a Cisco IOS XE-based device on the network. The administrator is worried that colleagues will make changes to the device while the script is running.
Which operation of the ncclient manager prevents colleagues from making changes to the devices while the script is running?
• A. m.lock(config=’running’)
• B. m.lock(target=’running’)
• C. m.freeze(target=’running’)
• D. m.freeze(config=’running’)
Which outcome is achieved with this Python code?
client.connect (ip, port= 22, username= usr, password= pswd ) stdin, stdout, stderr =
client.exec_command ( ‘show ip bgp 192.168.101.0 bestpath\n ‘ ) print (stdout)
• A. connects to a Cisco device using SSH and exports the BGP table for the prefix
• B. displays the output of the show command in a formatted way
• C. connects to a Cisco device using SSH and exports the routing table information
• D. connects to a Cisco device using Telnet and exports the routing table information

Refer to the exhibit. Which JSON syntax is derived from this data?
• A. {[{‘First Name’: ‘Johnny’, ‘Last Name’: ‘Table’, ‘Hobbies’: [‘Running’, ‘Video games’]}, {‘First Name’: ‘Billy’, ‘Last Name’: ‘Smith’, ‘Hobbies’: [‘Napping’, ‘Reading’]}]}
• B. {‘Person’: [{‘First Name’: ‘Johnny’, ‘Last Name’: ‘Table’, ‘Hobbies’: ‘Running’, ‘Video games’}, {‘First Name’: ‘Billy’, ‘Last Name’: ‘Smith’, ‘Hobbies’: ‘Napping’, ‘Reading’}]}
• C. {[{‘First Name’: ‘Johnny’, ‘Last Name’: ‘Table’, ‘Hobbies’: ‘Running’, ‘Hobbies’: ‘Video games’}, {‘First Name’: ‘Billy’, ‘Last Name’: ‘Smith’, ‘Hobbies’: ‘Napping’, ‘Reading’}]}
• D. {‘Person’: [{‘First Name’: ‘Johnny’, ‘Last Name’: ‘Table’, ‘Hobbies’: [‘Running’, ‘Video games’]}, {‘First Name’: ‘Billy’, ‘Last Name’: ‘Smith’, ‘Hobbies’: [‘Napping’, ‘Reading’]}]}
Which data is properly formatted with JSON?
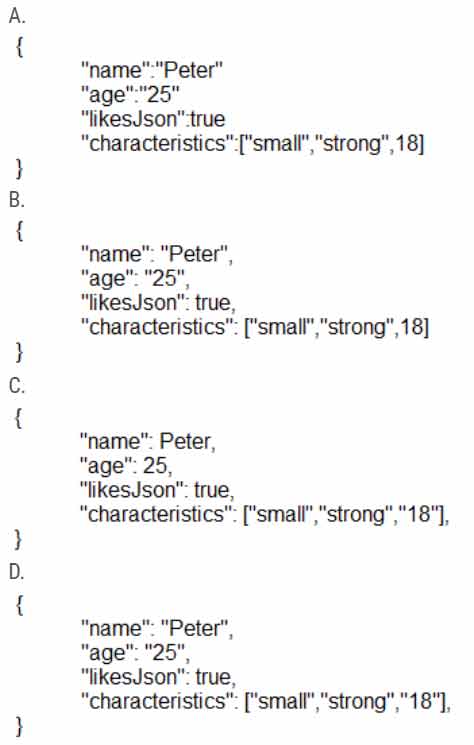
Correct Answer: B
Question 443
Based on the output below, which Python code shows the value of the “upTime” key?
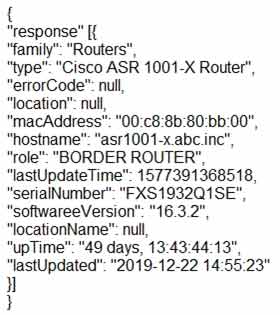
• A. json_data = response.json() print(json_data[‘response’][0][‘upTime’])
• B. json_data = response.json() print(json_data[response][0][upTime])
• C. json_data = json.loads(response.text) print(json_data[‘response’][‘family’][‘upTime’])
• D. json_data = response.json() print(json_data[‘response’][family][‘upTime’])
Which exhibit displays a valid JSON file?
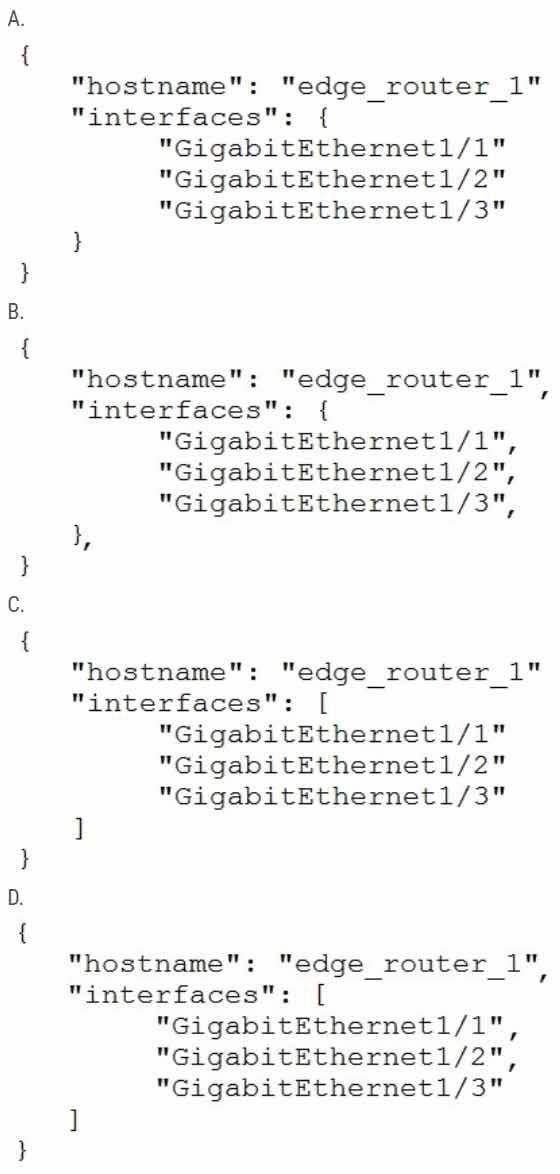
Correct Answer: D
Refer to the exhibit.
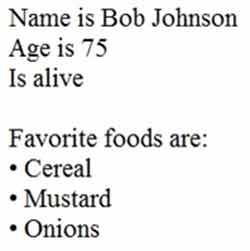
What is the JSON syntax that is formed from the data?
- A. {Name: Bob Johnson, Age: 75, Alive: true, Favorite Foods: [Cereal, Mustard, Onions]}
- B. {“Name” : “Bob Johnson”, “Age”: 75, “Alive”: true, “Favorite Foods”: [“Cereal”, “Mustard”, “Onions”]}
- C. {“Name”: “Bob Johnson”, “Age”: 75, “Alive”: True, “Favorite Foods”: “Cereal”, “Mustard”, “Onions”}
- D. {“Name”: “Bob Johnson”, “Age”: Seventyfive, “Alive”: true, “Favorite Foods”: [“Cereal”, “Mustard”, “Onions”]}
Which JSON syntax is valid?
- A. {“switch”: “name”: “dist”, “interfaces”: [“gig1”, “gig2”, “gig3”]}
- B. {/”switch/”: {/”name/”: “dist”, /”interfaces/”: [“gig1”, “gig2”, “gig3”]}}
- C. {“switch”: {“name”: “dist”, “interfaces”: [“gig1”, “gig2”, “gig3”]}}
- D. {“switch”: (“name”: “dist”, “interfaces”: [“gig1”, “gig2”, “gig3”])}
What is the structure of a JSON web token?
• A. three parts separated by dots: header, payload, and signature
• B. three parts separated by dots: version, header, and signature
• C. header and payload
• D. payload and signature
A response code of 404 is received while using the REST API on Cisco DNA Center to POST to this URI:
/dna/intent/api/v1/template-programmer/project
What does the code mean?
• A. The POST/PUT request was fulfilled and a new resource was created. Information about the resource is in the response body.
• B. The request was accepted for processing, but the processing was not completed.
• C. The client made a request for a resource that does not exist.
• D. The server has not implemented the functionality that is needed to fulfill the request.
Which two operations are valid for RESTCONF? (Choose two.)
• A. PULL
• B. PUSH
• C. PATCH
• D. REMOVE
• E. ADD
• F. HEAD
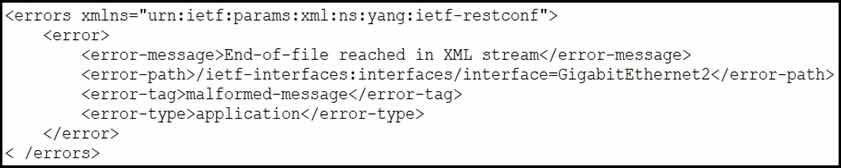
Refer to the exhibit. An engineer is using XML in an application to send information to a RESTCONF enabled device. After sending the request, the engineer gets this response message and an HTTP response code of 400. What do these responses tell the engineer?
• A. The Accept header sent was application/xml.
• B. POST was used instead of PUT to update.
• C. The Content-Type header sent was application/xml.
• D. A JSON body was used.
What is used to validate the authenticity of client and is sent in HTTP requests as a JSON object?
• A. SSH
• B. HTTPS
• C. JWT
• D. TLS
What is YANG used for?
• A. scraping data via CLI
• B. processing SNMP read-only polls
• C. describing data models
• D. providing a transport for network configuration data between client and server
Which HTTP status code is the correct response for a request with an incorrect password applied to a REST API session?
• A. HTTP Status Code: 200
• B. HTTP Status Code: 302
• C. HTTP Status Code: 401
• D. HTTP Status Code: 504
Which protocol does REST API rely on to secure the communication channel?
• A. HTTP
• B. SSH
• C. HTTPS
• D. TCP
At which layer does Cisco DNA Center support REST controls?
• A. session layer
• B. northbound APIs
• C. EEM applets or scripts
• D. YAML output from responses to API calls
Which algorithms are used to secure REST API from brute attacks and minimize the impact?
• A. SHA-512 and SHA-384
• B. MD5 algorithm-128 and SHA-384
• C. SHA-1, SHA-256, and SHA-512
• D. PBKDF2, BCrypt, and SCrypt
Which method of account authentication does OAuth 2.0 use within REST APIs?
• A. username/role combination
• B. access tokens
• C. cookie authentication
• D. basic signature workflow
Which two protocols are used with YANG data models? (Choose two.)
• A. TLS
• B. RESTCONF
• C. SSH
• D. NETCONF
• E. HTTPS
What is a benefit of data modeling languages like YANG?
• A. They create more secure and efficient SNMP OIDs.
• B. They provide a standardized data structure, which results in configuration scalability and consistency.
• C. They enable programmers to change or write their own applications within the device operating system.
• D. They make the CLI simpler and more efficient.
Which protocol infers that a YANG data model is being used?
• A. SNMP
• B. RESTCONF
• C. REST
• D. NX-API
Which method displays text directly into the active console with a synchronous EEM applet policy?
• A. event manager applet boom event syslog pattern ‘UP’ action 1.0 syslog priority direct msg ‘logging directly to console’
• B. event manager applet boom event syslog pattern ‘UP’ action 1.0 gets ‘logging directly to console’
• C. event manager applet boom event syslog pattern ‘UP’ action 1.0 string ‘logging directly to console’
• D. event manager applet boom event syslog pattern ‘UP’ action 1.0 puts ‘logging directly to console’
Which two steps are required for a complete Cisco DNA Center upgrade? (Choose two.)
• A. automation backup
• B. system update
• C. golden image selection
• D. proxy configuration
• E. application updates
Which method creates an EEM applet policy that is registered with EEM and runs on demand or manually?
• A. event manager applet ondemand event none action 1.0 syslog priority critical msg ‘This is a message from ondemand’
• B. event manager applet ondemand action 1.0 syslog priority critical msg ‘This is a message from ondemand’
• C. event manager applet ondemand event register action 1.0 syslog priority critical msg ‘This is a message from ondemand’
• D. event manager applet ondemand event manual action 1.0 syslog priority critical msg ‘This is a message from ondemand’
What does this EEM applet event accomplish?
“event snmp oid 1.3.6.1.3.7.6.5.3.9.3.8.7 get-type next entry-op gt entry-val 75 poll-interval 5”
• A. Upon the value reaching 75%, a SNMP event is generated and sent to the trap server.
• B. It reads an SNMP variable, and when the value exceeds 75%, it triggers an action.
• C. It issues email when the value is greater than 75% for five polling cycles.
• D. It presents a SNMP variable that can be interrogated.
What is a requirement for an Ansible-managed node?
• A. It must have an SSH server running.
• B. It must be a Linux server or a Cisco device.
• C. It must support ad hoc commands.
• D. It must have an Ansible Tower installed.
Which characteristic distinguishes Ansible from Chef?
• A. Ansible uses Ruby to manage configurations. Chef uses YAML to manage configurations.
• B. The Ansible server can run on Linux, Unix or Windows. The Chef server must run on Linux or Unix.
• C. Ansible pushes the configuration to the client. Chef client pulls the configuration from the server.
• D. Ansible lacks redundancy support for the primary server. Chef runs two primary servers in active/active mode.
DRAG DROP –
Drag and drop the characteristics from the left onto the orchestration tools that they describe on the
right.
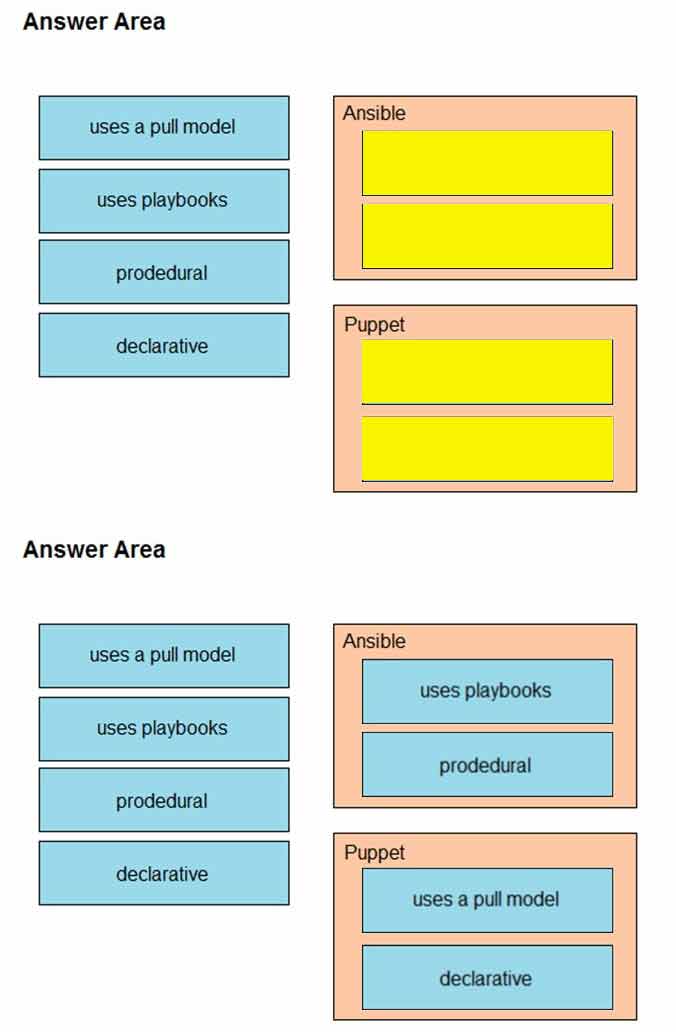
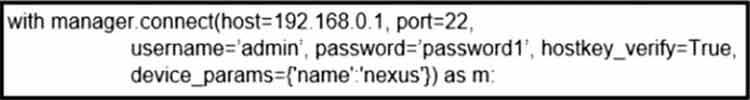
Refer to the exhibit. What does the snippet of code achieve?
• A. It creates an SSH connection using the SSH key that is stored, and the password is ignored.
• B. It creates a temporary connection to a Cisco Nexus device and retrieves a token to be used for API calls.
• C. It opens an ncclient connection to a Cisco Nexus device and maintains it for the duration of the context.
• D. It opens a tunnel and encapsulates the login information, if the host key is correct.
Which two characteristics define the Intent API provided by Cisco DNA Center? (Choose two.)
• A. northbound API Most Voted
• B. business outcome oriented
• C. device-oriented
• D. southbound API
• E. procedural
In a Cisco DNA Center Plug and Play environment, why would a device be labeled unclaimed?
• A. The device has not been assigned a workflow.
• B. The device could not be added to the fabric.
• C. The device had an error and could not be provisioned.
• D. The device is from a third-party vendor.
What does the Cisco DNA Center use to enable the delivery of applications through a network and to yield analytics for innovation?
• A. process adapters
• B. Command Runner
• C. intent-based APIs
• D. domain adapters
Which devices does Cisco DNA Center configure when deploying an IP-based access control policy?
• A. all devices integrating with ISE
• B. selected individual devices
• C. all devices in selected sites
• D. all wired devices
Which tool is used in Cisco DNA Center to build generic configurations that are able to be applied on devices with similar network settings?
• A. Command Runner
• B. Application Policies
• C. Template Editor
• D. Authentication Template
In which part of the HTTP message is the content type specified?
• A. HTTP method
• B. body
• C. header
• D. URI
An engineer must create an EEM applet that sends a syslog message in the event a change happens in the network due to trouble with an OSPF process. Which action should the engineer use? event manager applet LogMessage event routing network 172.30.197.0/24 type all
• A. action 1 syslog msg ג€OSPF ROUTING ERROR ג €
• B. action 1 syslog send ג€OSPF ROUTING ERROR ג €
• C. action 1 syslog pattern ג €OSPF ROUTING ERRORג€
• D. action 1 syslog write ג €OSPF ROUTING ERROR ג €
An engineer runs the code against an API of Cisco DNA Center, and the platform returns this output.
What does the response indicate?
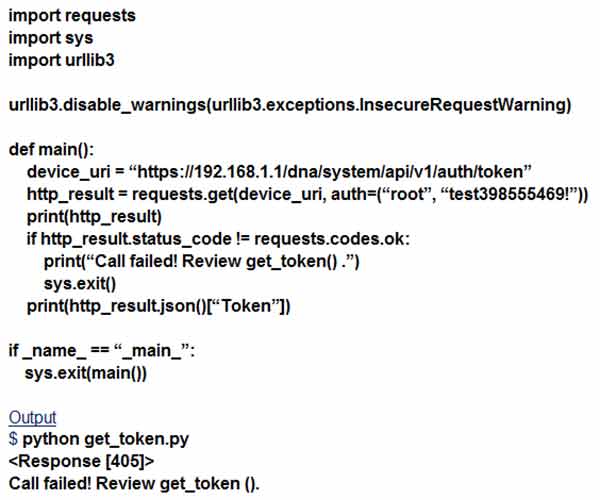
• A. The authentication credentials are incorrect.
• B. The URI string is incorrect.
• C. The Cisco DNA Center API port is incorrect.
• D. The HTTP method is incorrect.
What are two benefits of YANG? (Choose two.)
• A. It enforces the use of a specific encoding format for NETCONF.
• B. It collects statistical constraint analysis information.
• C. It enables multiple leaf statements to exist within a leaf list.
• D. It enforces configuration semantics.
• E. It enforces configuration constraints.
DRAG DROP –
Drag and drop the characteristics from the left onto the orchestration tools they describe on the
right.
Select and Place:
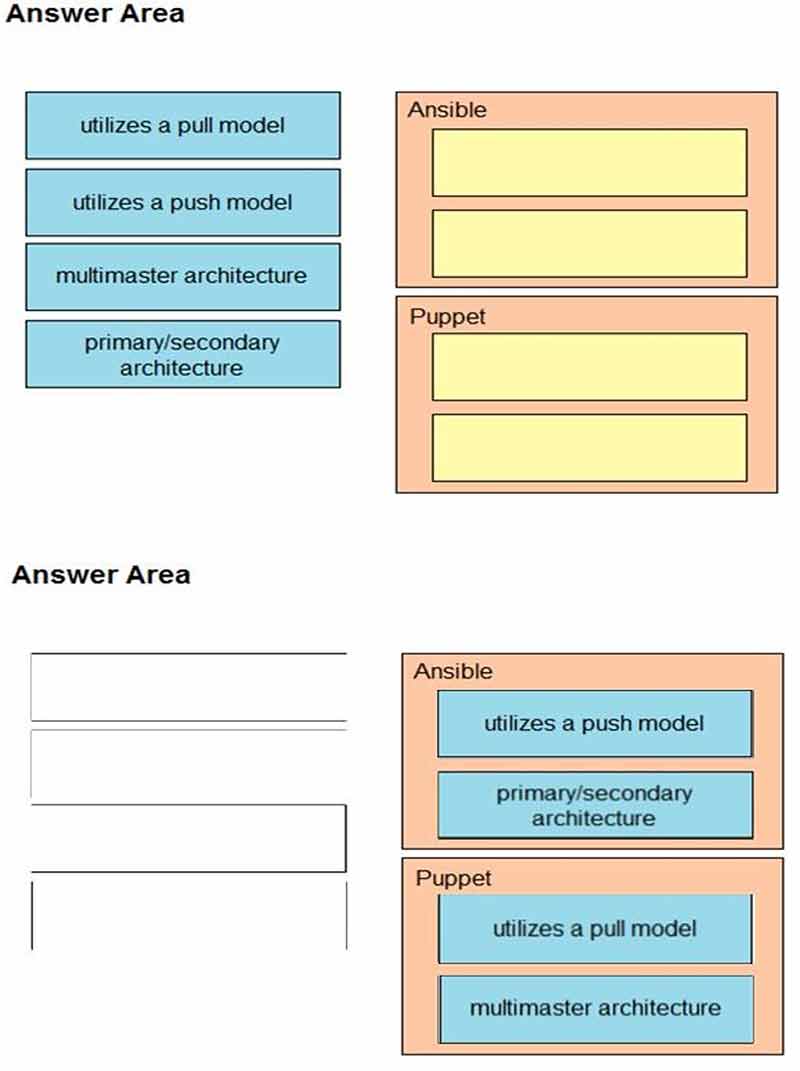
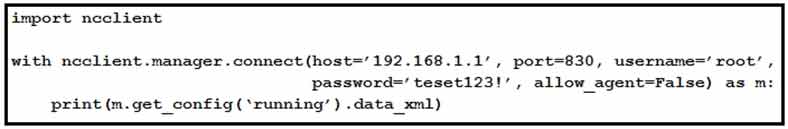
Refer to the exhibit. After running the code in the exhibit, which step reduces the amount of data that the NETCONF server returns to the NETCONF client, to only the interface’s configuration?
• A. Use the Ixml library to parse the data returned by the NETCONF server for the interface’s configuration.
• B. Create an XML filter as a string and pass it to get_config() method as an argument.
• C. Create a JSON filter as a string and pass it to the get_config() method as an argument.
• D. Use the JSON library to parse the data returned by the NETCONF server for the interface’s configuration.
Running the script causes the output in the exhibit. Which change to the first line of the script resolves the error?
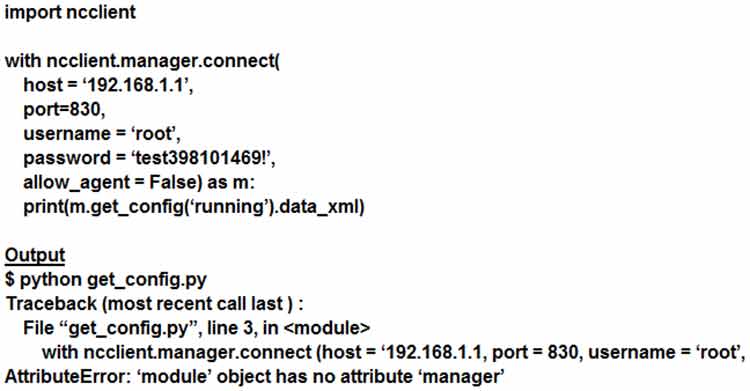
• A. from ncclient import
• B. import manager
• C. from ncclient import *
• D. import ncclient manager
Which line must be added in the Python function to return the JSON object {`cat_9k`: `FXS1932Q2SE`}?
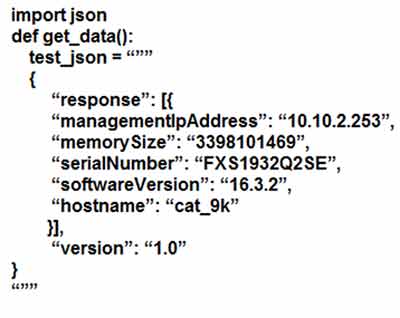
• A. return (json.dumps({d[‘hostname’]: d[‘serialNumber’] for d in json.loads(test_json)[‘response’]}))
• B. return (json.dumps({for d in json.loads(test_json)[‘response’]: d[‘hostname’]: d[‘serialNumber’]}))
• C. return (json.loads({d[‘hostname’]: d[‘serialNumber’] for d in json.dumps(test_json)[‘response’}))
• D. return (json.loads({for d in json.dumps(test_json)[‘response’]: d[‘hostname’]: d[‘serialNumber’]}))
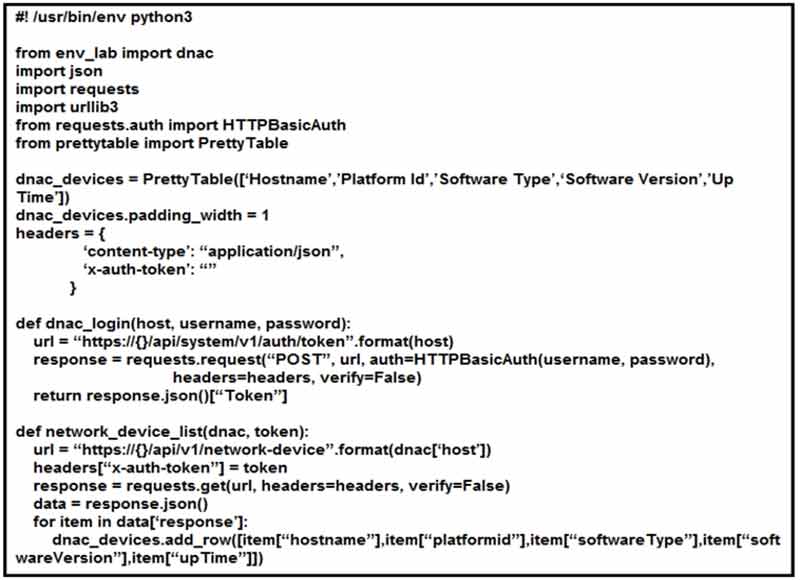
Refer to the exhibit. Which code results in the working Python script displaying a list of network devices from the Cisco DNA Center?
• A. network_device_list(dnac[ג€host ג €], dnac[ג€usernameג€],dnac[ ג €passwordג€]) login = dnac_login(dnac) print(dnac_devices)
• B. login = dnac_login(dnac[ג€hostג€], dnac[ג€usernameג€], dnac[ג€password ג €]) network_device_list(dnac, login) print(dnac_devices)
• C. login = dnac_login(dnac[ג€hostג€], dnac[ג€usernameג€], dnac[ג€password ג €]) network_device_list(dnac, login) for item in dnac_devices: print(dnac_devices.item)
• D. network_device_list(dnac[ג€host ג €], dnac[ג€usernameג€], dnac[ ג €passwordג€]) login = dnac_login(dnac) for item in dnac_devices: print(dnac_devices.item)
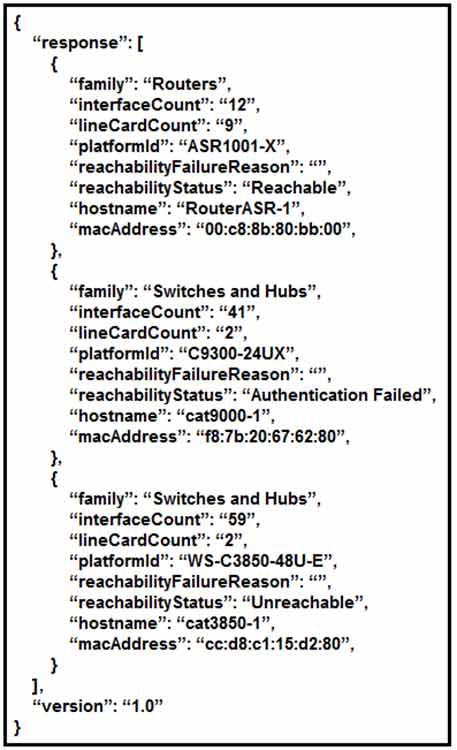
What does the Cisco DNA REST response indicate?
• A. Cisco DNA Center has the incorrect credentials for cat3850-1
• B. Cisco DNA Center is unable to communicate with cat9000-1
• C. Cisco DNA Center has the incorrect credentials for cat9000-1
• D. Cisco DNA Center has the incorrect credentials for RouterASR-1
What is a characteristic of YANG?
• A. It is a Cisco proprietary language that models NETCONF data.
• B. It allows model developers to create custom data types.
• C. It structures data in an object-oriented fashion to promote model reuse.
• D. It provides loops and conditionals to control flow within models.
DRAG DROP –
Drag and drop the snippets onto the blanks within the code to construct a script that changes the routing from gateway 1 to gateway 2 from 11:00 p.m. to 12:00 a.m. (2300 to 2400) only, daily. Not all options are used, and some options may be used twice.
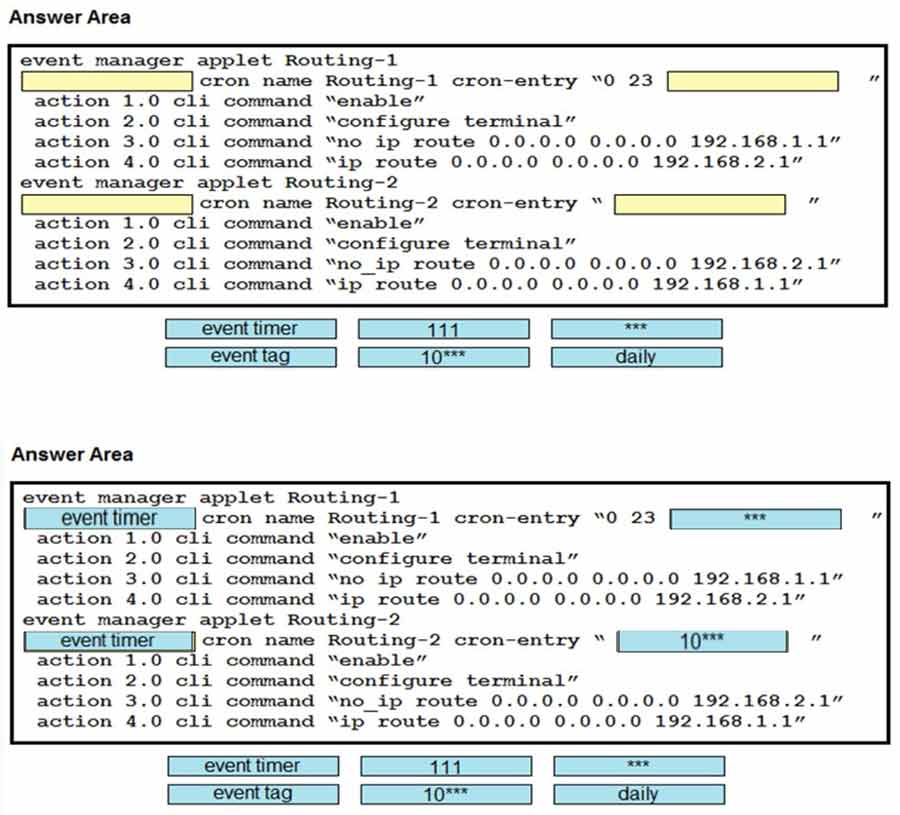
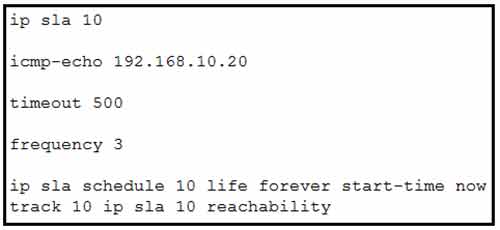
Refer to the exhibit. The IP SLA is configured in a router. An engineer must configure an EEM applet to shut down the interface and bring it back up when there is a problem with the IP SLA. Which configuration should the engineer use?
• A. event manager applet EEM_IP_SLA event track 10 state down
• B. event manager applet EEM_IP_SLA event track 10 state unreachable
• C. event manager applet EEM_IP_SLA event sla 10 state unreachable
• D. event manager applet EEM_IP_SLA event sla 10 state down
Refer to the exhibit.
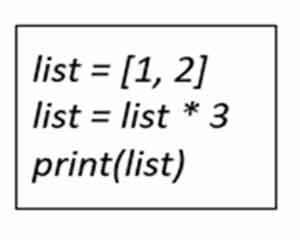
What is the value of the variable list after the code is run?
• A. [1, 2], [1, 2], [1, 2]
• B. [1, 2] * 3
• C. [1, 2, 1, 2, 1, 2]
• D. [3, 6]
Refer to the exhibit.
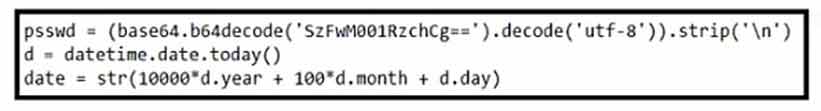
Which result does the Python code achieve?
• A. The code encrypts a base64 decrypted password.
• B. The code converts time to the Epoch LINUX time format.
• C. The code converts time to the “year/month/day” time format.
• D. The code converts time to the yyyymmdd representation.
Refer to the exhibit.
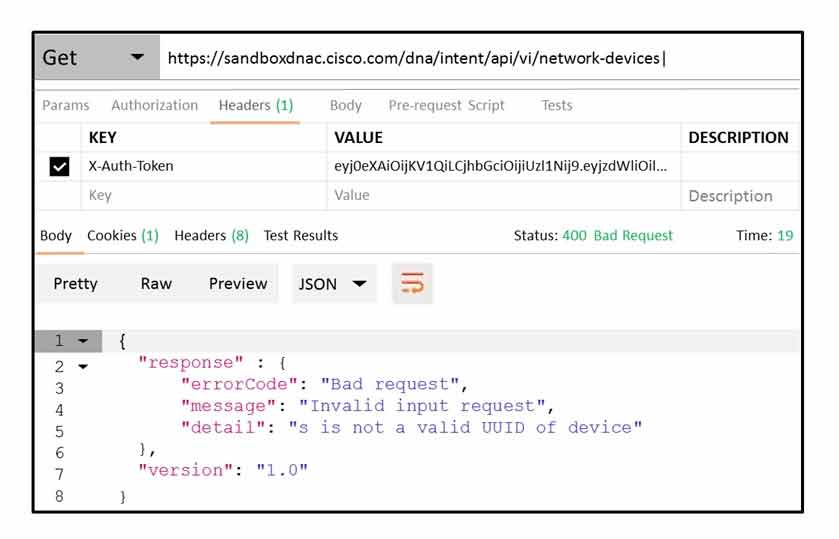
POSTMAN is showing an attempt to retrieve network device information from Cisco DNA Center API.
What is the issue?
• A. The URI string is incorrect.
• B. The token has expired.
• C. Authentication has failed.
• D. The JSON payload contains the incorrect UUID.
Refer to the exhibit.
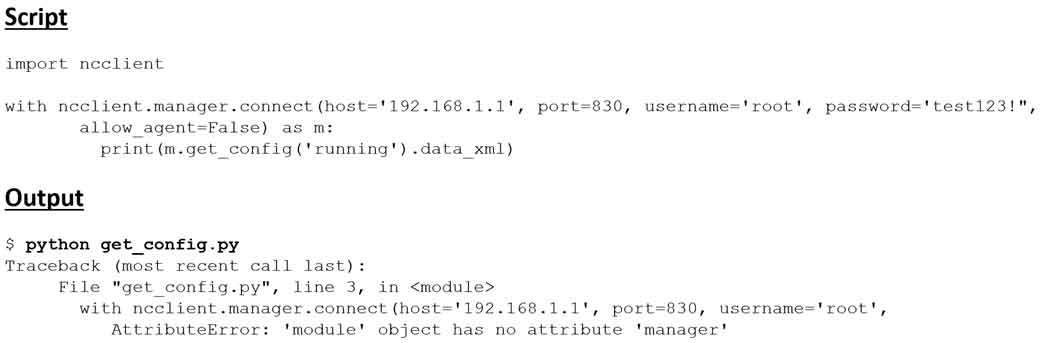
Running the script causes the output in the exhibit. What should be the first line of the script?
• A. from ncclient import manager
• B. import manager
• C. from ncclient import *
• D. ncclient manager import
Refer to the exhibit.
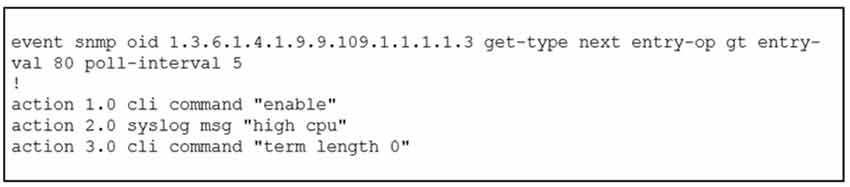
An engineer must create a script that appends the output of the show process cpu sorted command to a file. Which action completes the configuration?
• A. action 4.0 syslog command “show process cpu sorted | append flash:high-cpu-file”
• B. action 4.0 cli command “show process cpu sorted | append flash:high-cpu-file”
• C. action 4.0 cns-event “show process cpu sorted | append flash:high-cpu-file”
• D. action 4.0 publish-event “show process cpu sorted | append flash:high-cpu-file”
What is an advantage of utilizing data models in a multivendor environment?
• A. lowering CPU load incurred to managed devices
• B. improving communication security with binary encoded protocols
• C. facilitating a unified approach to configuration and management
• D. removing the distinction between configuration and runtime state data
How is a data modeling language used?
• A. To enable data to be easily structured, grouped, validated, and replicated.
• B. To represent finite and well-defined network elements that cannot be changed.
• C. To model the flows of unstructured data within the infrastructure.
• D. To provide human readability to scripting languages.
A network engineer is configuring OSPF on a router. The engineer wants to prevent having a route to 172.16.0.0/16 learned via OSPF in the routing table and configures a prefix list using the command ip prefix-list OFFICE seq 5 deny 172.16.0.0/16. Which two additional configuration commands must be
applied to accomplish the goal? (Choose two.)
• A. ip prefix-list OFFICE seq 10 permit 0.0.0.0/0 le 32
• B. distribute-list prefix OFFICE in under the OSPF process
• C. distribute-list OFFICE in under the OSPF process
• D. distribute-list OFFICE out under the OSPF process
• E. ip prefix-list OFFICE seq 10 permit 0.0.0.0/0 ge 32
DRAG DROP –
Drag and drop the characteristics from the left onto the technology types on the right.
Select and Place:
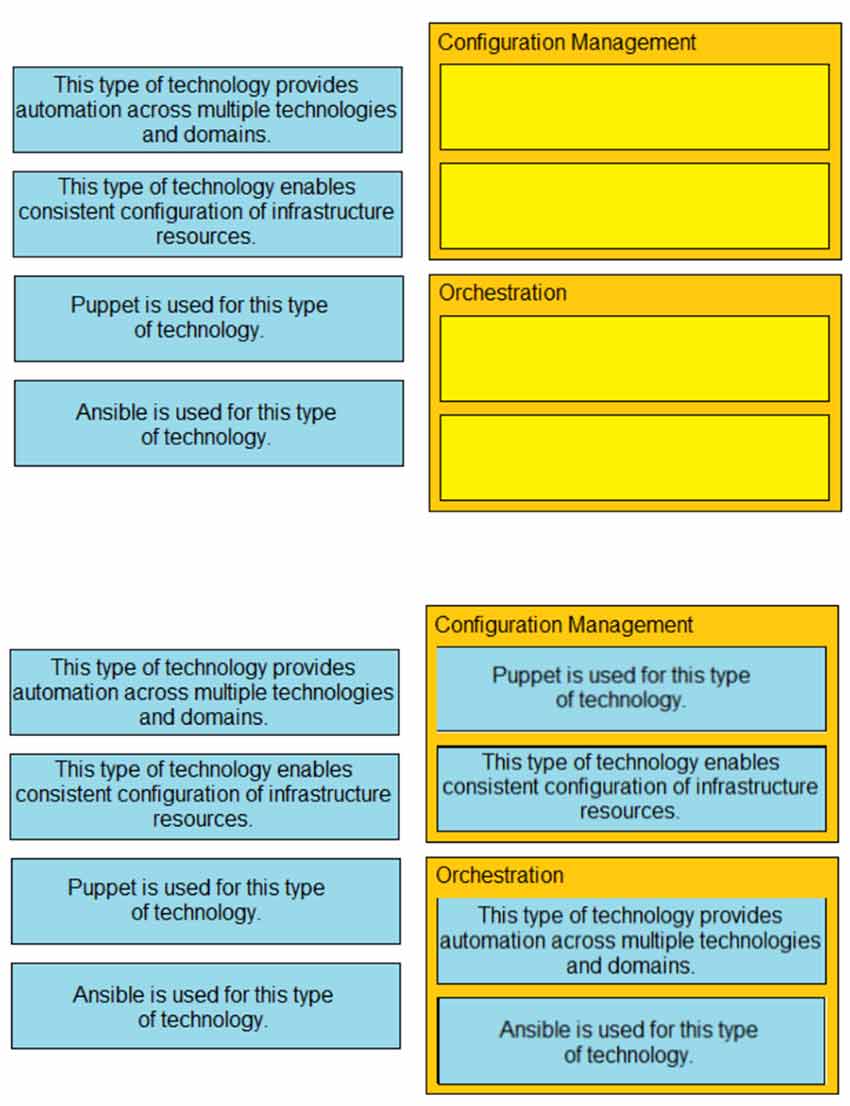
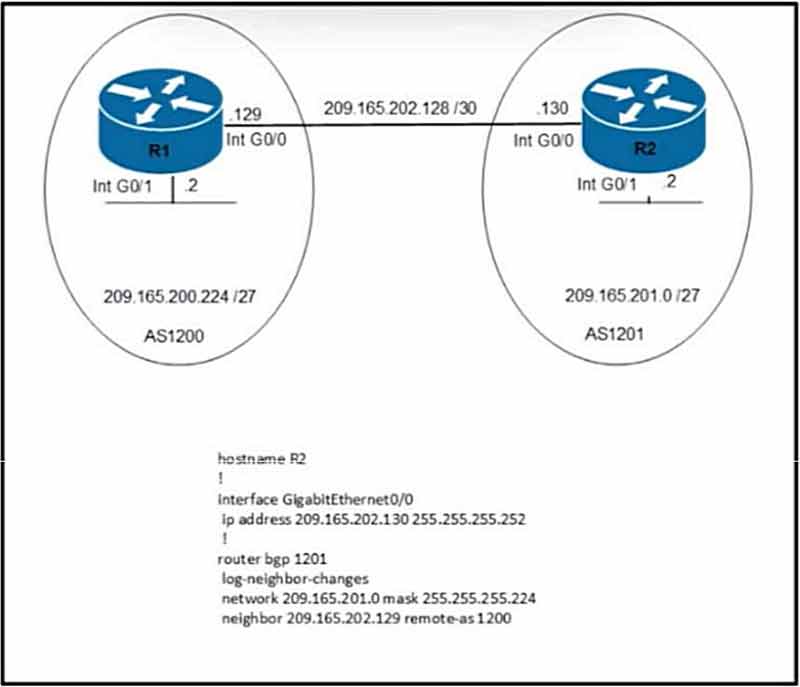
Refer to the exhibit. Which command set must be applied on R1 to establish a BGP neighborship with R2 and to allow communication from R1 to reach the networks?
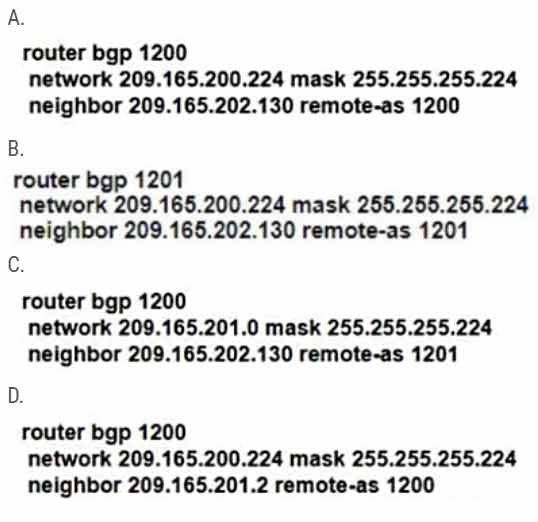
Correct Answer: B
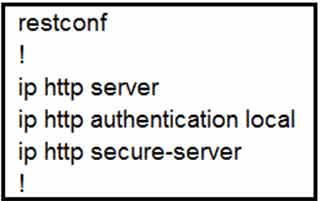
Refer to the exhibit. Which command must be configured for RESTCONF to operate on port 8888?
• A. restconf port 8888
• B. ip http restconf port 8888
• C. ip http port 8888
• D. restconf http port 8888
Why would a log file contain a * next to the date?
• A. The network device was receiving NTP time when the log messages were recorded.
• B. The network device was unable to reach the NTP server when the log messages were recorded.
• C. The network device is not configured to use NTP.
• D. The network device is not configured to use NTP time stamps for logging.
What is one difference between EIGRP and OSPF?
• A. EIGRP uses the DUAL distance vector algorithm, and OSPF uses the Dijkstra link-state algorithm.
• B. OSPF uses the DUAL distance vector algorithm, and EIGRP uses the Dijkstra link-state algorithm.
• C. EIGRP uses the variance command for unequal cost load balancing, and OSPF supports unequal cost balancing by default.
• D. OSPF is a Cisco proprietary protocol, and EIGRP is an IETF open standard protocol.
DRAG DROP –
Drag and drop the characteristics from the left onto the routing protocols they describe on the right.
Select and Place:
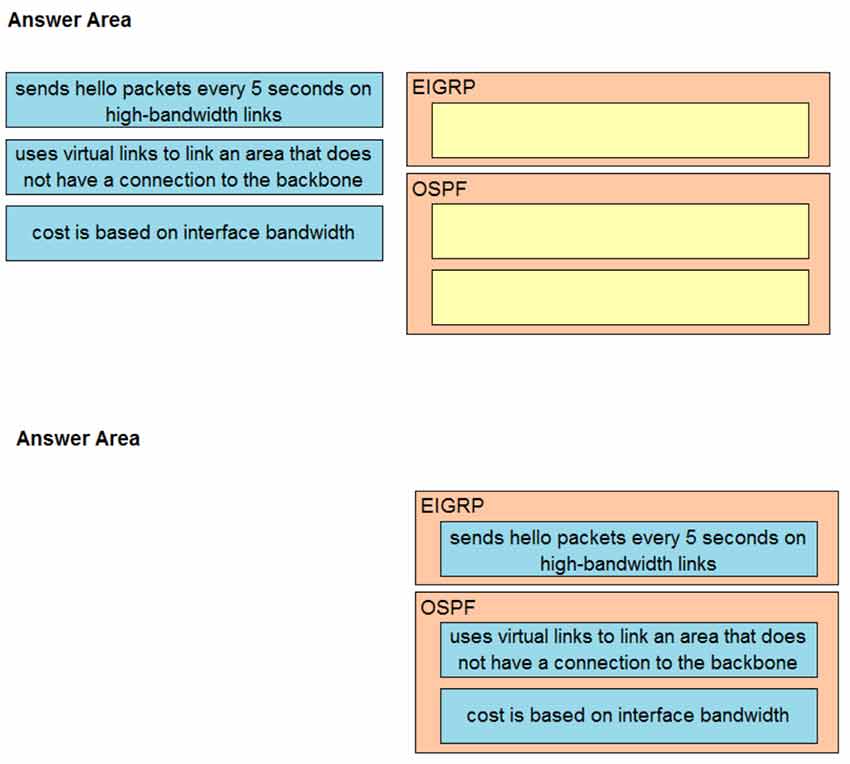
A network engineer must configure a router to send logging messages to a syslog server based on these requirements:
* uses syslog IP address: 10.10.10.1
* uses a reliable protocol
* must not use any well-known TCP/UDP ports
Which configuration must be used?
• A. logging host 10.10.10.1 transport tcp port 1024
• B. logging host 10.10.10.1 transport udp port 1024
• C. logging host 10.10.10.1 transport udp port 1023
• D. logging origin-id 10.10.10.1
Question 501
